Ethical Hacking Course Module 19 Cryptography Lab Session

Ethical Hacking Lab Pdf Welcome to practical demonstration of cryptography withe the help of cryptography portal. it has great resource if you want to learn about the encryption and decryption of data. This repository contains the official study modules for ceh v13 (certified ethical hacker) in pdf format. these materials are meant to help cybersecurity students and professionals understand key concepts in ethical hacking and prepare for the ceh certification.

Online Course Ethical Hacking Cryptography From Pluralsight Class Smce you are an expert ethical hacker and penetration tester, your it director will instruct you to encrypt data usmg various encrypting algorithms m order to secure the organization's information. lab objectives this lab will show you how to encrypt data and how to use it. Since you are an expert ethical hacker and penetration tester, your it director will instruct you to encrypt data using various encrypting algorithms in order to secure the organization's information. We will use a cryptool portal which has many tools for this session. this is a great tool to learn about different kinds of cryptography. Since you are an expert ethical hacker and penetration tester, your it director will instruct you to encrypt data using various encrypting algorithms111 order to secure the organization’s information. lab objectives tins lab will show you how to encrypt data and how to use it.
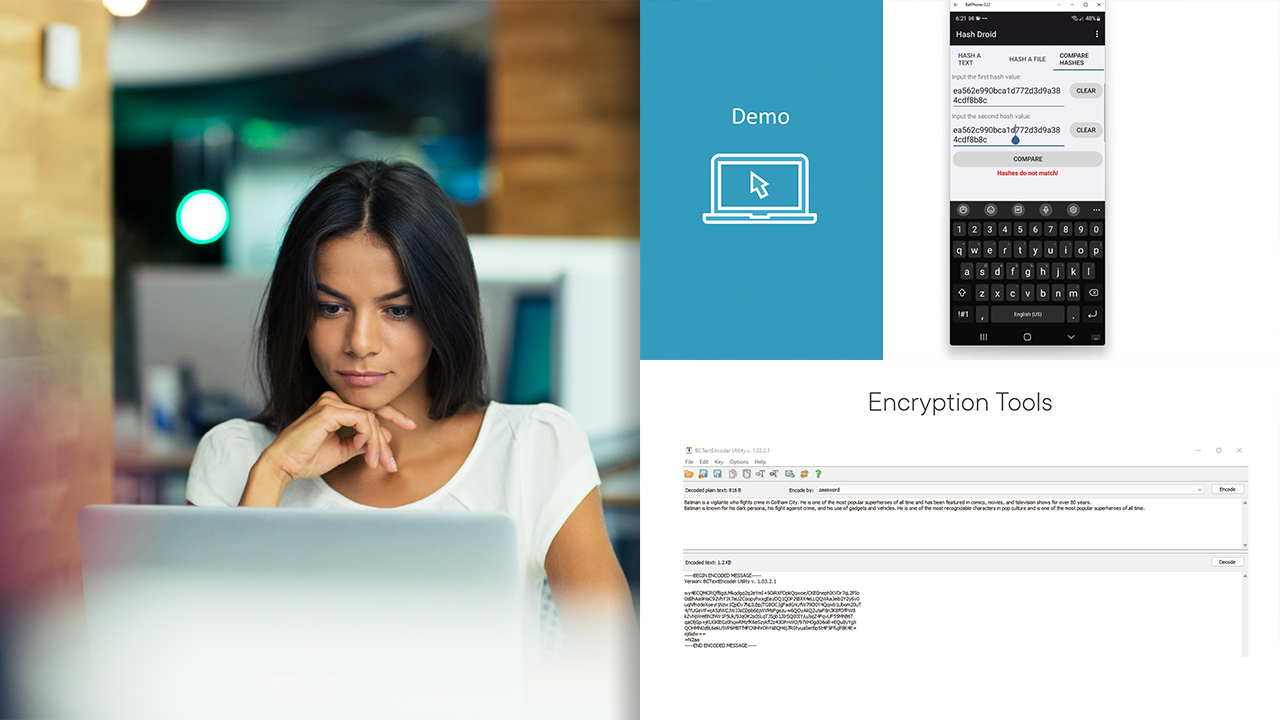
Ethical Hacking Cryptography We will use a cryptool portal which has many tools for this session. this is a great tool to learn about different kinds of cryptography. Since you are an expert ethical hacker and penetration tester, your it director will instruct you to encrypt data using various encrypting algorithms111 order to secure the organization’s information. lab objectives tins lab will show you how to encrypt data and how to use it. The accredited course provides the advanced hacking tools and techniques used by hackers and information security professionals alike to break into an organization. You will learn practical cybersecurity skills including web application hacking, network penetration testing, linux privilege escalation, cryptography, forensics, reverse engineering, and more. The syllabus aims to teach students the various phases of ethical hacking through hands on activities in a structured manner over the course of multiple modules. Preview text ethical hacking lab series lab 19: using certificates to encrypt email certified ethical hacking domain: cryptography document version: 2015 08.

Certified Ethical Hacking Course In Delhi Ceh V13 Ai Training And The accredited course provides the advanced hacking tools and techniques used by hackers and information security professionals alike to break into an organization. You will learn practical cybersecurity skills including web application hacking, network penetration testing, linux privilege escalation, cryptography, forensics, reverse engineering, and more. The syllabus aims to teach students the various phases of ethical hacking through hands on activities in a structured manner over the course of multiple modules. Preview text ethical hacking lab series lab 19: using certificates to encrypt email certified ethical hacking domain: cryptography document version: 2015 08.

Ethical Hacking Lab Experiments Guide Pdf Internet Computing The syllabus aims to teach students the various phases of ethical hacking through hands on activities in a structured manner over the course of multiple modules. Preview text ethical hacking lab series lab 19: using certificates to encrypt email certified ethical hacking domain: cryptography document version: 2015 08.

Solution Cehv8 Module 19 Cryptography Studypool
Comments are closed.