Ethical Hacking Bug Bounty Syllabus Pdf Security Computer Security
Syllabus Ethical Hacking Pdf Ethical hacking & bug bounty syllabus free download as pdf file (.pdf), text file (.txt) or read online for free. the document outlines a cyber security summer internship focused on ethical hacking and bug bounty hunting, lasting 8 weeks online. This course provides a structured learning path for individuals looking to enter the bug bounty and ethical hacking industry, offering practical insights into hacking methodologies, vulnerability identification, and responsible disclosure practices.
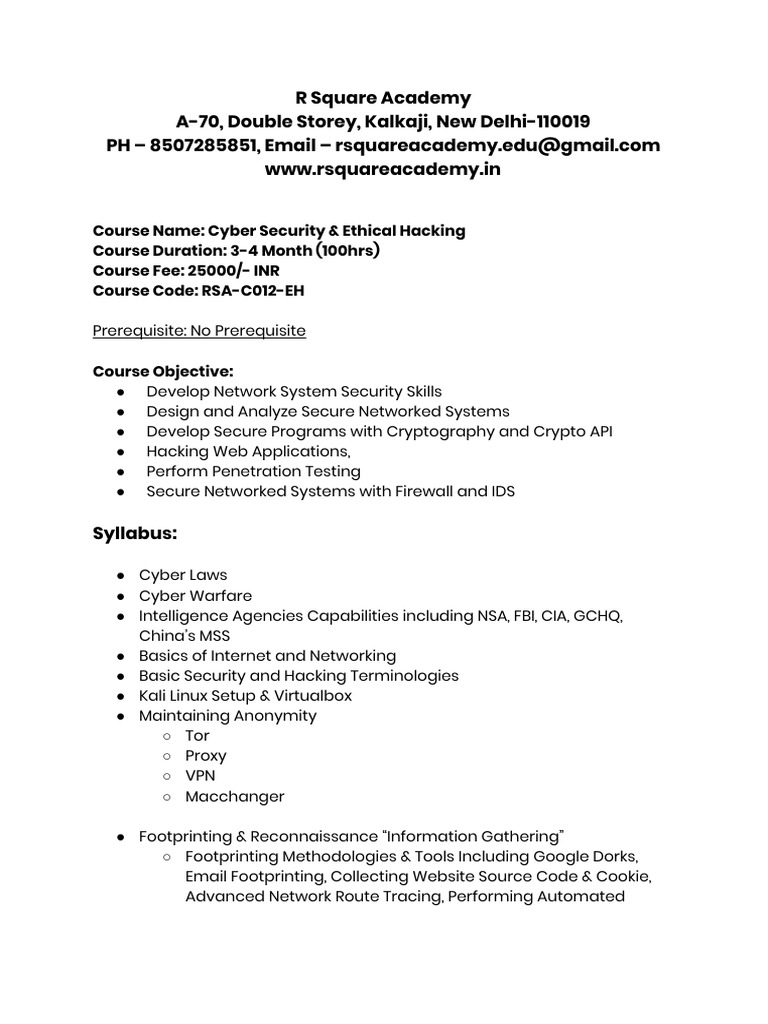
Ethical Hacking Syllabus By Aadish Jain 1 Pdf Wi Fi Security Hacker Capture a web page as it appears now for use as a trusted citation in the future. Kali linux a comprehensive step by step beginner's guide to learn the basics of cybersecurity and ethical computer hacking, including wireless penetration testing tools to secure your network by jason kno.pdf. Central to ethical hacking is the cia triad—confidentiality, integrity, and availability—which outlines the core objectives of information security. effective security management integrates these principles through structured frameworks such as iso 27001 and nist. Module 1 intro to ethical hacking information security overview information security threats and attack vectors hacking concepts ethical hacking concepts information security controls penetration testing concepts information security laws and standards.

Complete Ethical Hacking Bug Bounty Course Pdf Guides Expert Training Central to ethical hacking is the cia triad—confidentiality, integrity, and availability—which outlines the core objectives of information security. effective security management integrates these principles through structured frameworks such as iso 27001 and nist. Module 1 intro to ethical hacking information security overview information security threats and attack vectors hacking concepts ethical hacking concepts information security controls penetration testing concepts information security laws and standards. If you learn ethical hacking, your chances of securing a career in cyber security will increase, an industry which will be recruiting 3.5 million unfilled cybersecurity jobs globally by 2022. Hacking fundamentals, web security vulnerabilities, attack methodologies, and advanced exploitation technique! the curriculum progresses from basic web security concepts to advanced topics like logical vulnerabilities. In this ebook, we’ll help ease those concerns by separating the ethical hacking myths from the truths. read on to learn more about what ethical hacking is and how crowdsourced security can benefit companies of all industries in today’s digital work environment. Introduction to ethical hacking. 1.10 what is hacking? 1.11 who is a hacker? 1.14 what is ethical hacking? 2.1 what is footprinting? 4. enumeration. 4.1 what is enumeration? 6. system hacking. 6.29 what is steganography? 7.5 what is a trojan? 9. social engineering social engineering concepts. 9.1 what is social engineering? 16.

Master Ethical Hacking Bug Bounty Oscp 2 0 From Scratch Royalboss If you learn ethical hacking, your chances of securing a career in cyber security will increase, an industry which will be recruiting 3.5 million unfilled cybersecurity jobs globally by 2022. Hacking fundamentals, web security vulnerabilities, attack methodologies, and advanced exploitation technique! the curriculum progresses from basic web security concepts to advanced topics like logical vulnerabilities. In this ebook, we’ll help ease those concerns by separating the ethical hacking myths from the truths. read on to learn more about what ethical hacking is and how crowdsourced security can benefit companies of all industries in today’s digital work environment. Introduction to ethical hacking. 1.10 what is hacking? 1.11 who is a hacker? 1.14 what is ethical hacking? 2.1 what is footprinting? 4. enumeration. 4.1 what is enumeration? 6. system hacking. 6.29 what is steganography? 7.5 what is a trojan? 9. social engineering social engineering concepts. 9.1 what is social engineering? 16.
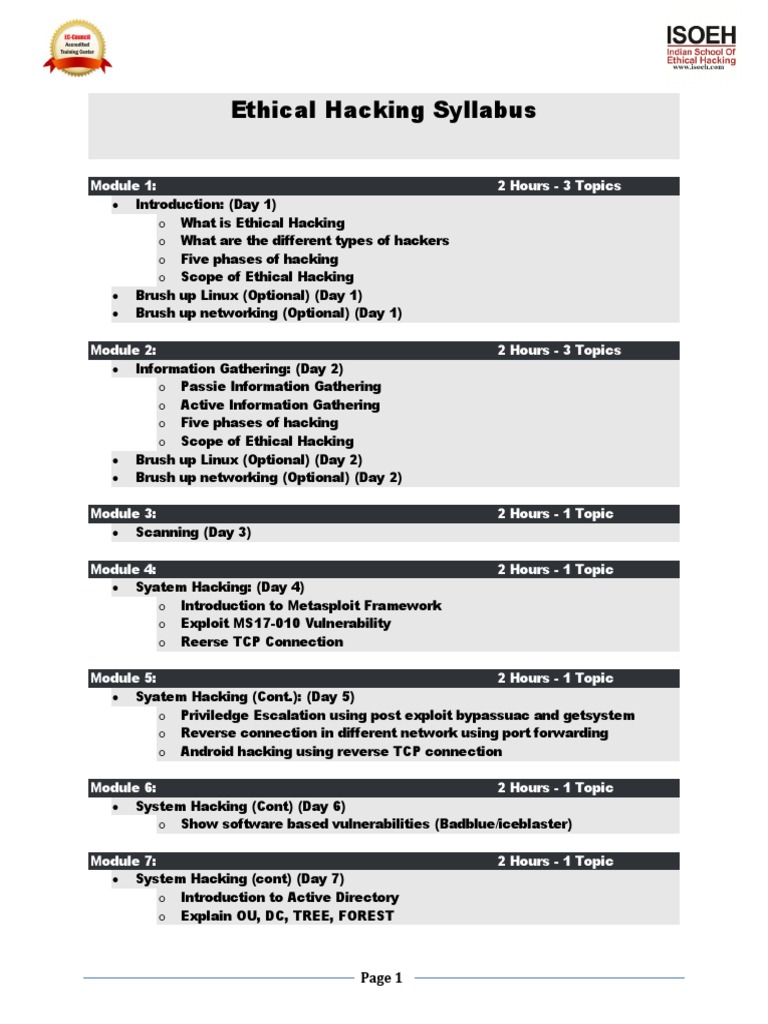
Ethical Hacking Syllabus Pdf Security Hacker Cryptography In this ebook, we’ll help ease those concerns by separating the ethical hacking myths from the truths. read on to learn more about what ethical hacking is and how crowdsourced security can benefit companies of all industries in today’s digital work environment. Introduction to ethical hacking. 1.10 what is hacking? 1.11 who is a hacker? 1.14 what is ethical hacking? 2.1 what is footprinting? 4. enumeration. 4.1 what is enumeration? 6. system hacking. 6.29 what is steganography? 7.5 what is a trojan? 9. social engineering social engineering concepts. 9.1 what is social engineering? 16.

Bug Bounty Decoded Unraveling The Mysteries Of Ethical Hacking Rewards
Comments are closed.