Ethical Hacking %f0%9f%91%a8%f0%9f%8f%bb%f0%9f%92%bb %e2%98%a0%ef%b8%8f How To Install Phoneinfoga Osint Tool

Phoneinfoga Information Gathering Osint Tool For Phone Numbers Ethical hacking is the authorized practice of testing computer systems, networks, and applications to identify security weaknesses. it helps organizations fix vulnerabilities before malicious hackers can exploit them. Practice ethical hacking and penetration testing on 170 hands on cybersecurity labs. join 9,000 security professionals mastering real world exploits. new challenges weekly start free today!.

Phoneinfoga Information Gathering Osint Tool For Phone Numbers Ethical hacker indonesia adalah komunitas untuk menyediakan wadah bagi seluruh ethical hacker di indonesia untuk berdiskusi dan berperan aktif untuk membantu masyarakat luas. Understand the 4 step reconnaissance workflow, ethical guidelines, and why osint is crucial for security testing. perfect foundation for the practical lessons ahead. Master ethical hacking and penetration testing skills to advance your cybersecurity career. learn reconnaissance, osint, password attacks, and vulnerability management through hands on projects guided by expert instructors. How will this course improve my ethical hacking skills? you'll learn to discover security weaknesses, run penetration tests, and fight against cyber attacks using a blend of theoretical information and hands on lab exercises.
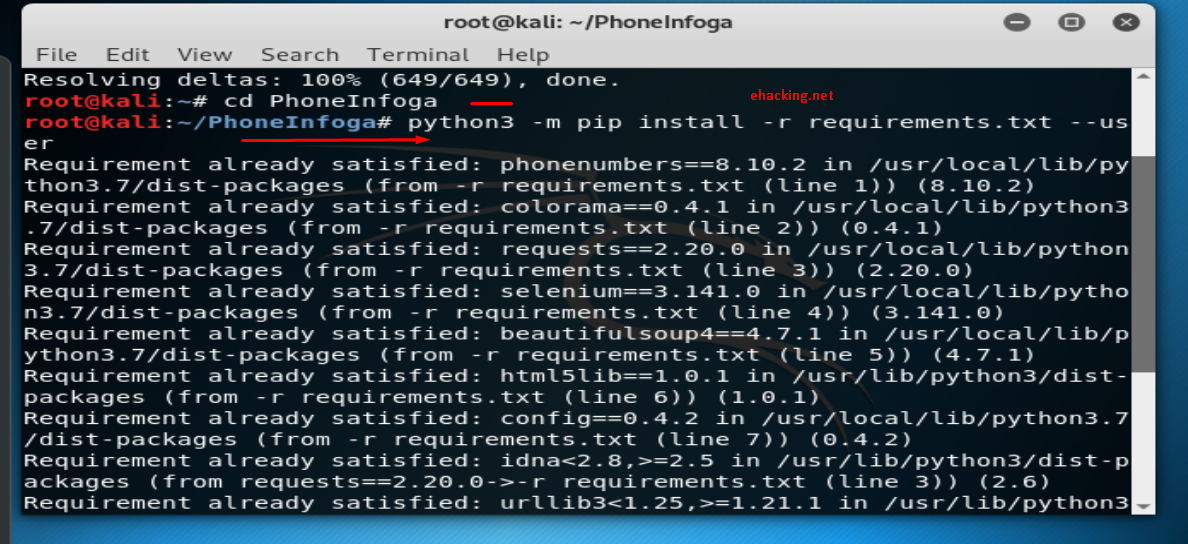
Phoneinfoga Advanced Osint Tool For Phone Number Master ethical hacking and penetration testing skills to advance your cybersecurity career. learn reconnaissance, osint, password attacks, and vulnerability management through hands on projects guided by expert instructors. How will this course improve my ethical hacking skills? you'll learn to discover security weaknesses, run penetration tests, and fight against cyber attacks using a blend of theoretical information and hands on lab exercises. In this article, we will look at the best free online ethical hacking resources for anybody considering an ethical hacking career. from education and tools to podcasts and other videos, there is no shortage of helpful resources available. Ethical hacking adalah praktik sah yang bertujuan menemukan dan memperbaiki kerentanan sistem sebelum dimanfaatkan oleh peretas jahat. dengan metode yang terstruktur, ethical hacking membantu perusahaan melindungi data sensitif dan meningkatkan keamanan sistem secara keseluruhan. Ethical hacking, also called penetration testing or white hat hacking, involves the identification and evaluation of weaknesses in computer systems, networks, and applications. The first known event of hacking had taken place in 1960 at mit and at the same time, the term "hacker" was originated. in this tutorial, we will take you through the various concepts of ethical hacking and explain how you can use them in a real time environment.
Phoneinfoga Phone Number Osint Part 2 Zsecurity In this article, we will look at the best free online ethical hacking resources for anybody considering an ethical hacking career. from education and tools to podcasts and other videos, there is no shortage of helpful resources available. Ethical hacking adalah praktik sah yang bertujuan menemukan dan memperbaiki kerentanan sistem sebelum dimanfaatkan oleh peretas jahat. dengan metode yang terstruktur, ethical hacking membantu perusahaan melindungi data sensitif dan meningkatkan keamanan sistem secara keseluruhan. Ethical hacking, also called penetration testing or white hat hacking, involves the identification and evaluation of weaknesses in computer systems, networks, and applications. The first known event of hacking had taken place in 1960 at mit and at the same time, the term "hacker" was originated. in this tutorial, we will take you through the various concepts of ethical hacking and explain how you can use them in a real time environment.

Phoneinfoga Information Gathering Y Osint Para Números Telefónicos Ethical hacking, also called penetration testing or white hat hacking, involves the identification and evaluation of weaknesses in computer systems, networks, and applications. The first known event of hacking had taken place in 1960 at mit and at the same time, the term "hacker" was originated. in this tutorial, we will take you through the various concepts of ethical hacking and explain how you can use them in a real time environment.
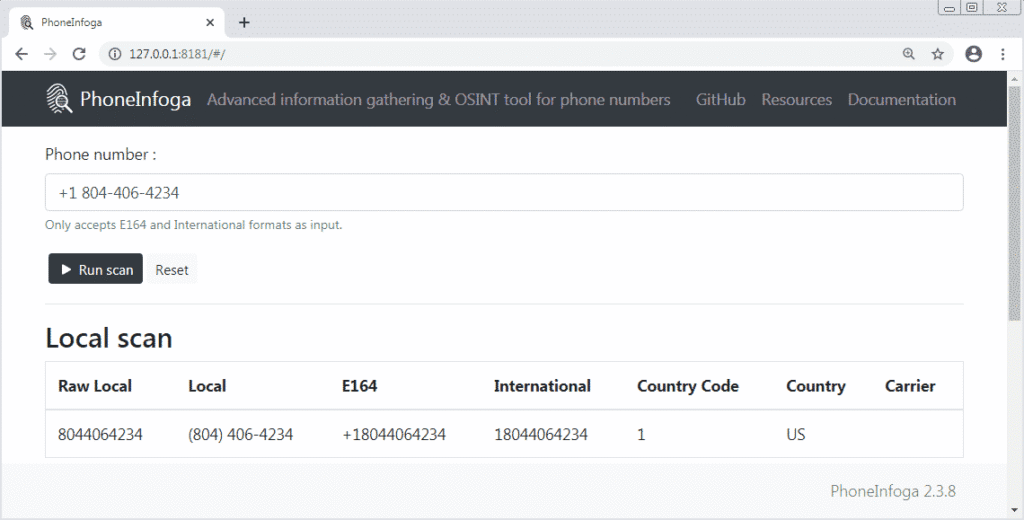
Phoneinfoga Osint Information Gathering Framework For Phone Numbers
Comments are closed.