Ethereum Smart Contract Backdoored Using Malicious Constructor

Priftil Ethereum Smart Contract Vulnerability Detection At Main While ethereum smart contracts are immutable by default, it is possible to achieve some degree of mutability by using upgrade patterns. upgrading contracts is necessary in cases where a critical flaw renders your old contract unusable and deploying new logic is the most feasible option. In a blog post published on wednesday, valentić described her discovery of malicious packages on the node package manager (npm) open source repository that abused ethereum smart contracts to facilitate malicious command and control.
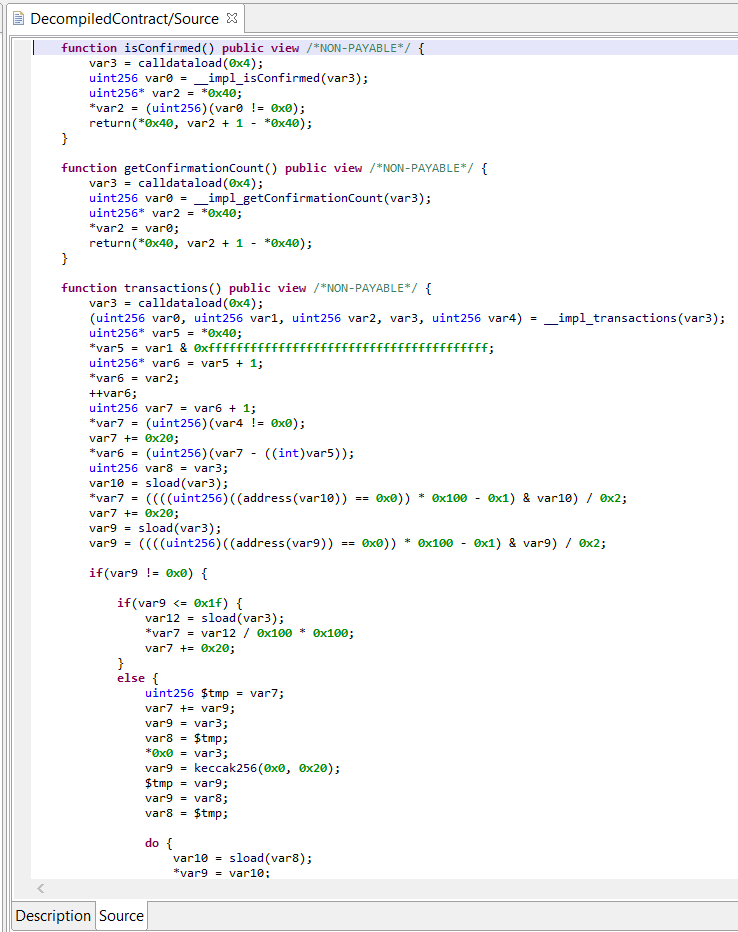
Ethereum Smart Contract Decompiler Jeb In Action In this video we go over how smart contracts written in solidity are deployed, and how the acoraida monica contract was backdoored. more. Jump oriented programming: ethereum smart contract #2 real world ctf 2018 by liveoverflow ethereum smart contract backdoored using malicious constructor by liveoverflow. Attackers behind a recent supply chain attack that involved rogue github repositories and npm packages used smart contracts on the ethereum blockchain to deliver malware payloads. the attacks. In this paper, we present a comprehensive analysis of the vulnerabilities in ethereum smart contracts. our methodology involves downloading the entire ethereum blockchain and identifying smart contracts, which we then scan for vulnerabilities using various tools.
Ethereum Smart Contracts Used To Push Malicious Code On Npm Reversinglabs Attackers behind a recent supply chain attack that involved rogue github repositories and npm packages used smart contracts on the ethereum blockchain to deliver malware payloads. the attacks. In this paper, we present a comprehensive analysis of the vulnerabilities in ethereum smart contracts. our methodology involves downloading the entire ethereum blockchain and identifying smart contracts, which we then scan for vulnerabilities using various tools. Numerous solutions for vulnerability detection have been proposed, but it is still unclear which one is the most effective. this paper presents a systematic literature review that explores vulnerabilities in ethereum smart contracts, focusing on automated detection tools and benchmark evaluation. A malicious campaign targeting developers through npm and github repositories has been uncovered, featuring an unusual method of using ethereum smart contracts to conceal command and control (c2) infrastructure. A new method of loading malware onto compromised devices via smart contracts on the ethereum (eth) blockchain has been identified as part of a larger campaign targeting npm packages and github. Here’s how ethereum smart contracts were abused to further this attack, and a look at the larger campaign to post and promote malicious packages on open source repositories like npm and github.
Comments are closed.