Erp Security Framework Protect Your Sensitive Data
Erp Security Framework Protect Your Sensitive Data Our team is dedicated to assisting you in configuring a robust erp security framework tailored to your business needs. whether you’re seeking guidance on user roles, encryption protocols, compliance requirements, or incident response planning, we’re here to provide the expertise and support you need. Assuring security within an erp system requires sophisticated strategies, controls, and measures to protect against unauthorized access and cyber threats. these tactics involve safeguarding data integrity, ensuring system availability, and maintaining confidentiality across all erp software modules.

Erp Security Framework Protect Your Sensitive Data Comprehensive guide to securing your erp systems and maintaining compliance with industry regulations while protecting sensitive business data from evolving cybersecurity threats. In this detailed guide, we explore best practices that organizations must implement to protect sensitive erp data, and how structured platforms like erpbynet support secure enterprise environments. Dynamics 365 provides an efficient role based security framework to ensure data confidentiality at all levels with well defined security roles and access controls. The proposed smaf provides organizations with an evidence based methodology for erp security evaluation, addressing a critical gap in both academic literature and practitioner guidance.

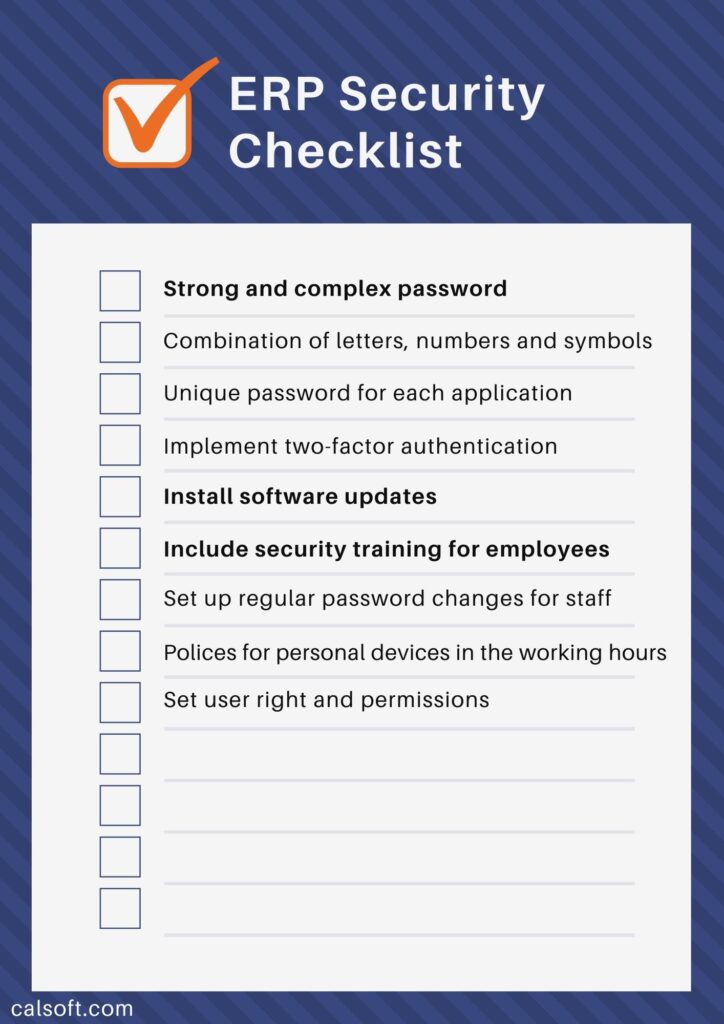
Erp Security Protecting Your Sensitive Business Data Optisys Dynamics 365 provides an efficient role based security framework to ensure data confidentiality at all levels with well defined security roles and access controls. The proposed smaf provides organizations with an evidence based methodology for erp security evaluation, addressing a critical gap in both academic literature and practitioner guidance. Protect your business with these ec council recommendations for securing erp software systems. this blog discusses the best erp cybersecurity practices for organizations. To assist you in creating a robust erp security strategy, we've compiled 12 top notch best practices to shield your erp data. by incorporating these best practices, you can strengthen your erp security and guarantee the highest level of protection for your data assets. Get a clear, actionable system risk assessment guide for pharma. learn the five essential steps to protect your data, supply chain, and compliance. This comprehensive article explores the multifaceted aspects of erp security, focusing on advanced access control mechanisms, data protection strategies, and compliance requirements.

3 Security Features To Protect Your Erp Data Protect your business with these ec council recommendations for securing erp software systems. this blog discusses the best erp cybersecurity practices for organizations. To assist you in creating a robust erp security strategy, we've compiled 12 top notch best practices to shield your erp data. by incorporating these best practices, you can strengthen your erp security and guarantee the highest level of protection for your data assets. Get a clear, actionable system risk assessment guide for pharma. learn the five essential steps to protect your data, supply chain, and compliance. This comprehensive article explores the multifaceted aspects of erp security, focusing on advanced access control mechanisms, data protection strategies, and compliance requirements.
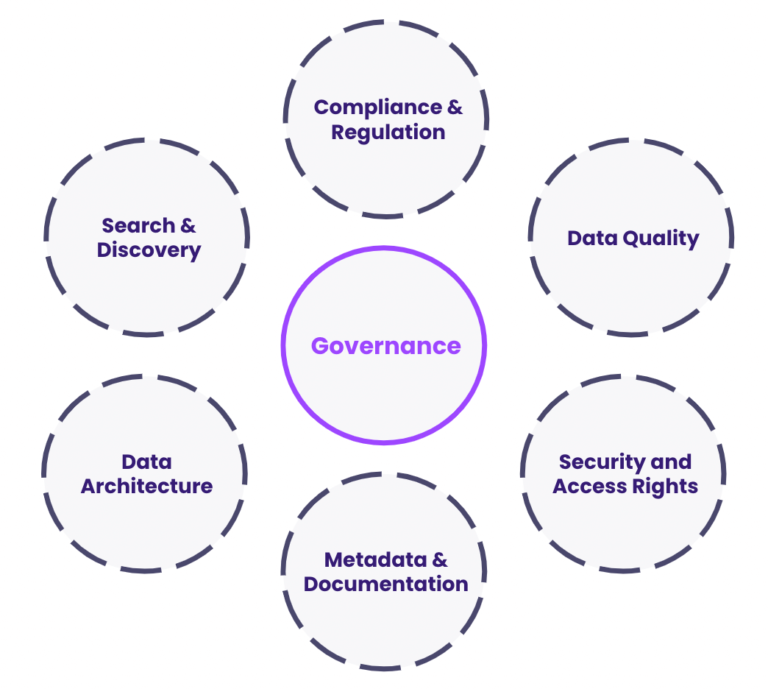
Data Security And Compliance In Erp Protecting Sensitive Information Get a clear, actionable system risk assessment guide for pharma. learn the five essential steps to protect your data, supply chain, and compliance. This comprehensive article explores the multifaceted aspects of erp security, focusing on advanced access control mechanisms, data protection strategies, and compliance requirements.

Safeguarding Your Sensitive Data Cybersecurity Best Practices For Erp
Comments are closed.