Ep02 Creating The Threat Model Diagram
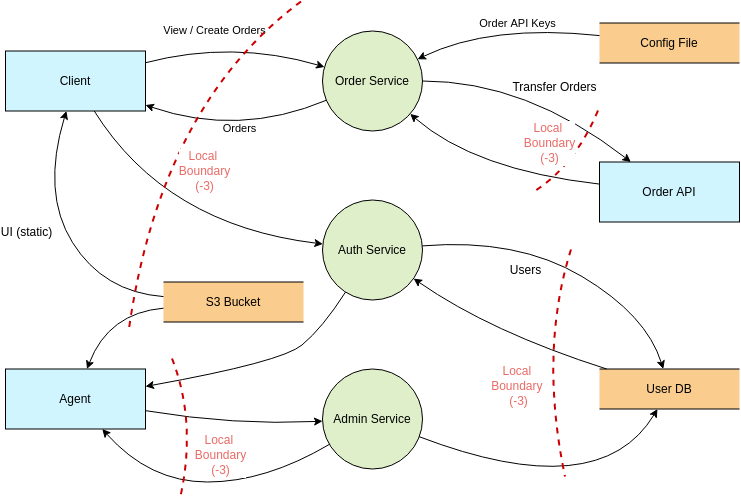
Threat Modeling Threat Model Diagram Template This video covers the basics of threat modeling, introduces the stride methodology, and provides a step by step guide to using the microsoft threat modeling tool. These models can be considered as reference template to show how we can construct threat modeling document. each of the labeled entities in the figures below are accompanied by meta information which describe the threats, recommended mitigations, and the associated security principle or goal.
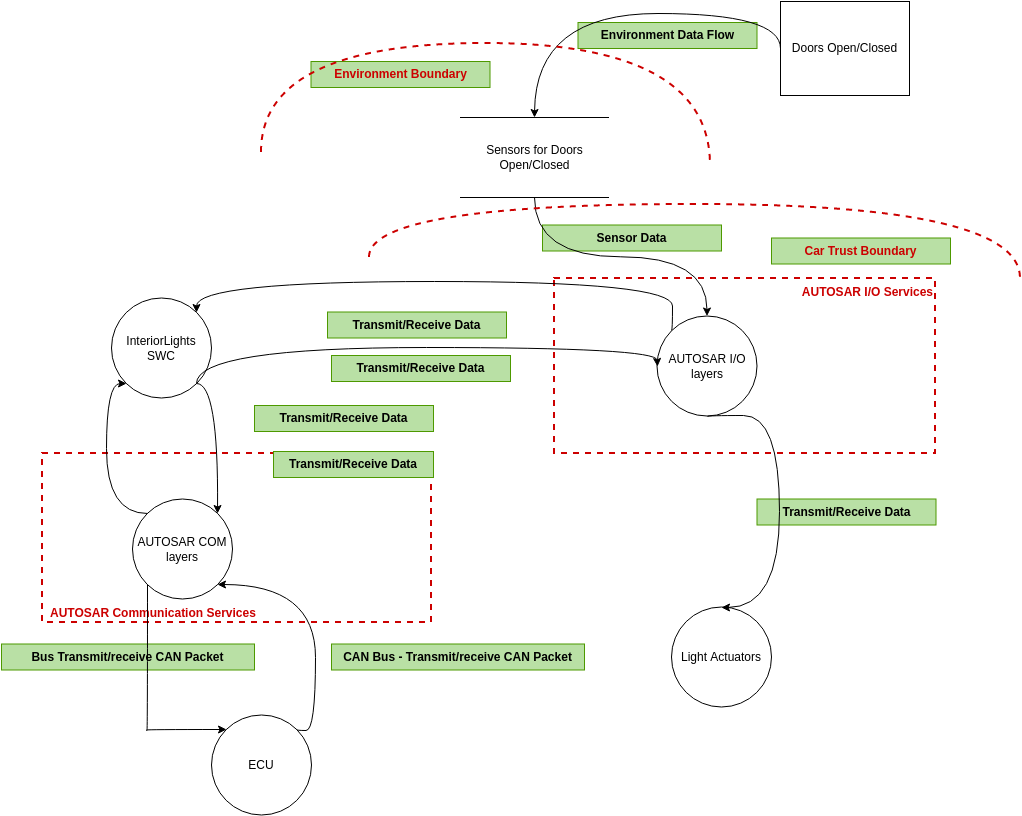
Threat Modeling Threat Model Diagram Template Data flow diagrams are graphical representations of your system and should specify each element, their interactions, and helpful context. Making threat modeling a core component of your sdlc can help increase product security. the threat modeling process can be decomposed into four high level steps. frequently, each step is documented as it is carried out. the resulting document is the threat model for the application. Threat modelling is a structured method to identify, analyze, and mitigate potential threats in systems, applications, or organizations. it helps teams uncover vulnerabilities early and build security into the design before attackers exploit weaknesses. A steb by step guide to creating a structured and repeatable threat model to identify threats and mitigate them against valuable assets in a system.

Threat Model Diagram Elements Download Scientific Diagram Threat modelling is a structured method to identify, analyze, and mitigate potential threats in systems, applications, or organizations. it helps teams uncover vulnerabilities early and build security into the design before attackers exploit weaknesses. A steb by step guide to creating a structured and repeatable threat model to identify threats and mitigate them against valuable assets in a system. In this task, we explore the mitre att&ck framework, a valuable resource for understanding cyber threats. it breaks down adversary tactics and techniques and offers insights into their methods. The threat modeling tool of vp online is a web based threat modeling tool, with a drag and drop interface to effortlessly create threat models. it comes with all the standard elements you need to create threat model for various platforms. You can learn from those models, use them a base to start your own, or contribute to and expand some of the models. thus making this a collaborative cookbook of threat models. Below is a comprehensive breakdown of each step to guide your threat modeling efforts. understanding the system’s components, boundaries, and data flows is foundational to threat modeling. start by creating a high level architecture diagram, often a data flow diagram (dfd). this includes:.

How To Create A Threat Model Offensive 360 O360 In this task, we explore the mitre att&ck framework, a valuable resource for understanding cyber threats. it breaks down adversary tactics and techniques and offers insights into their methods. The threat modeling tool of vp online is a web based threat modeling tool, with a drag and drop interface to effortlessly create threat models. it comes with all the standard elements you need to create threat model for various platforms. You can learn from those models, use them a base to start your own, or contribute to and expand some of the models. thus making this a collaborative cookbook of threat models. Below is a comprehensive breakdown of each step to guide your threat modeling efforts. understanding the system’s components, boundaries, and data flows is foundational to threat modeling. start by creating a high level architecture diagram, often a data flow diagram (dfd). this includes:.
Comments are closed.