Ensure Zero Trust Success With These 3 Factors

Ensure Zero Trust Success With These 3 Factors We used the delphi method to identify csfs for implementing zero trust by conducting three rounds of opinion gathering and reaching a consensus with a panel of cybersecurity experts. Implementing zero trust requires shifting from perimeter based defenses to a more granular security approach. it focuses on minimizing attack surfaces by segmenting networks, tightly controlling user and device access, and continuously monitoring activity.
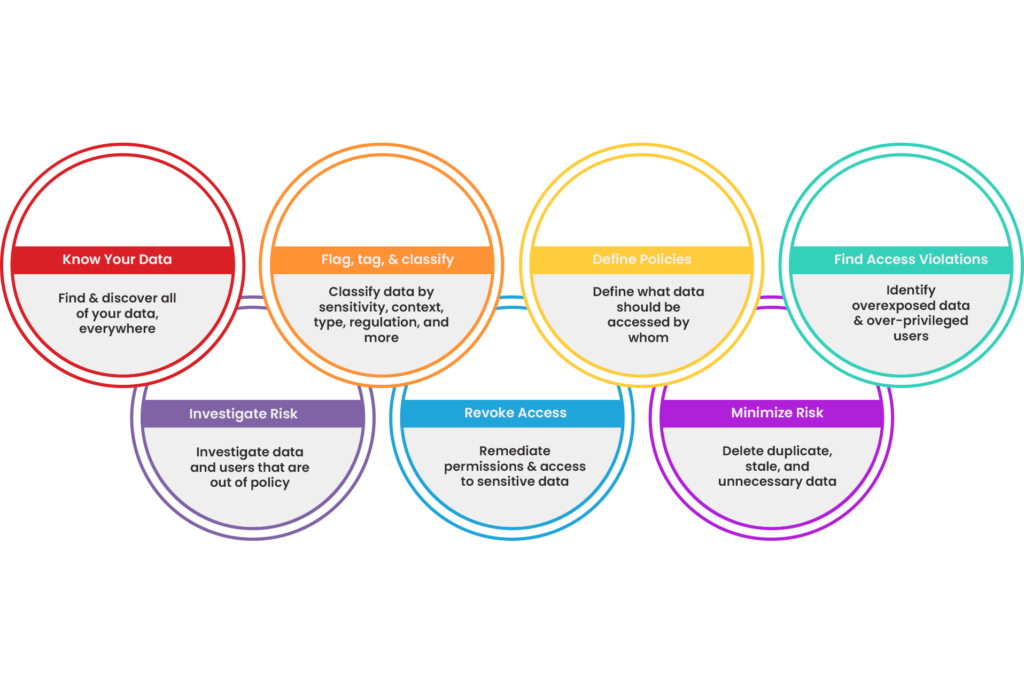
Enable Zero Trust Bigid By rethinking how it can be achieved and incorporated within existing systems, infrastructure, work styles and anticipated future changes, you can greatly improve zero trust’s potential for. Key guides for implementing zero trust in your company, and how to avoid common mistakes. Discover how zero trust architecture empowers cisos to enhance security without complexity, focusing on visibility, orchestration, and proactive threat management. Simplify zero trust implementation with this detailed guide. learn the policies, compliance, and monitoring strategies to implement zero trust security.

The 3 Zero Trust Principles And Why They Matter Discover how zero trust architecture empowers cisos to enhance security without complexity, focusing on visibility, orchestration, and proactive threat management. Simplify zero trust implementation with this detailed guide. learn the policies, compliance, and monitoring strategies to implement zero trust security. Research indicates that efficient zero trust implementation requires strong organizational awareness of security concerns, a strong security strategy, and technical readiness to deploy appropriate tools and procedures. Begin by articulating a compelling vision that ties zero trust to business outcomes such as agility, compliance, and customer trust. engage executives and board members early, translating technical concepts into language that resonates with business objectives. Discover how to implement a comprehensive zero trust security model in your organization. learn the core principles, implementation strategies, and best practices for modern cybersecurity. Learn how to get started with deploying microsoft’s zero trust pillars with step by step guidance on securing identity, data, applications, infrastructure, and networks. the zero trust framework is widely regarded as a key security model and a commonly referenced standard in modern cybersecurity.
How To Smash Your Zero Trust Success Metrics Research indicates that efficient zero trust implementation requires strong organizational awareness of security concerns, a strong security strategy, and technical readiness to deploy appropriate tools and procedures. Begin by articulating a compelling vision that ties zero trust to business outcomes such as agility, compliance, and customer trust. engage executives and board members early, translating technical concepts into language that resonates with business objectives. Discover how to implement a comprehensive zero trust security model in your organization. learn the core principles, implementation strategies, and best practices for modern cybersecurity. Learn how to get started with deploying microsoft’s zero trust pillars with step by step guidance on securing identity, data, applications, infrastructure, and networks. the zero trust framework is widely regarded as a key security model and a commonly referenced standard in modern cybersecurity.
Comments are closed.