End User Activity Devices
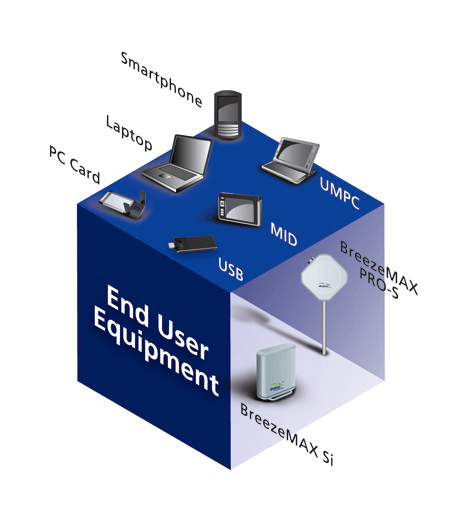
Product Image Alvarion End User Devices Its end user monitoring tool monitors performance across devices, browsers, and third party services, collecting information on failures, crashes, and network traffic. These solutions track and analyze users’ behavior, enabling organizations to detect and respond to suspicious activities, maintain compliance, and optimize business processes and workflows. this guide will explore the top 10 user activity monitoring software solutions available in the market today.

End User Authorization Integrations Zoom Developer Docs In this article, we’ll compare the top user activity monitoring solutions for business available today. we will explore their notable features, integrations, activity tracking abilities, and their overall efficiency based on our own internal expert research. An end user device is any hardware that individuals within your organization use to perform their tasks. these devices are the tools that employees interact with directly, whether they are in the office, working remotely, or on the move. An endpoint detection and response (edr) solution is a security tool that continuously monitors endpoints—like computers, servers, and mobile devices—for suspicious activity. Sometimes called endpoint monitoring, device performance monitoring involves collecting data from various user devices, including computers, on premises servers and mobile devices.

End User Devices An endpoint detection and response (edr) solution is a security tool that continuously monitors endpoints—like computers, servers, and mobile devices—for suspicious activity. Sometimes called endpoint monitoring, device performance monitoring involves collecting data from various user devices, including computers, on premises servers and mobile devices. The platform provides an end user monitoring component that tracks key metrics across devices, browsers and third party services to capture data about errors, crashes, network requests and other events. Endpoint monitoring is keeping track of and auditing the health, status, risks, and activity of endpoint devices. it is an ongoing process that systematically manages endpoints to keep them safe, secure, and performing optimally. User activity monitoring plays an important role in network security and bandwidth management. monitoring and tracking end user behavior on devices, networks, and other company owned it resources help identify internal threats in a network. User activity monitoring tools offer real time tracking of user actions across networks and devices. these solutions help organizations safeguard data and ensure compliance by identifying unusual or unauthorized activity.

End User Devices The platform provides an end user monitoring component that tracks key metrics across devices, browsers and third party services to capture data about errors, crashes, network requests and other events. Endpoint monitoring is keeping track of and auditing the health, status, risks, and activity of endpoint devices. it is an ongoing process that systematically manages endpoints to keep them safe, secure, and performing optimally. User activity monitoring plays an important role in network security and bandwidth management. monitoring and tracking end user behavior on devices, networks, and other company owned it resources help identify internal threats in a network. User activity monitoring tools offer real time tracking of user actions across networks and devices. these solutions help organizations safeguard data and ensure compliance by identifying unusual or unauthorized activity.
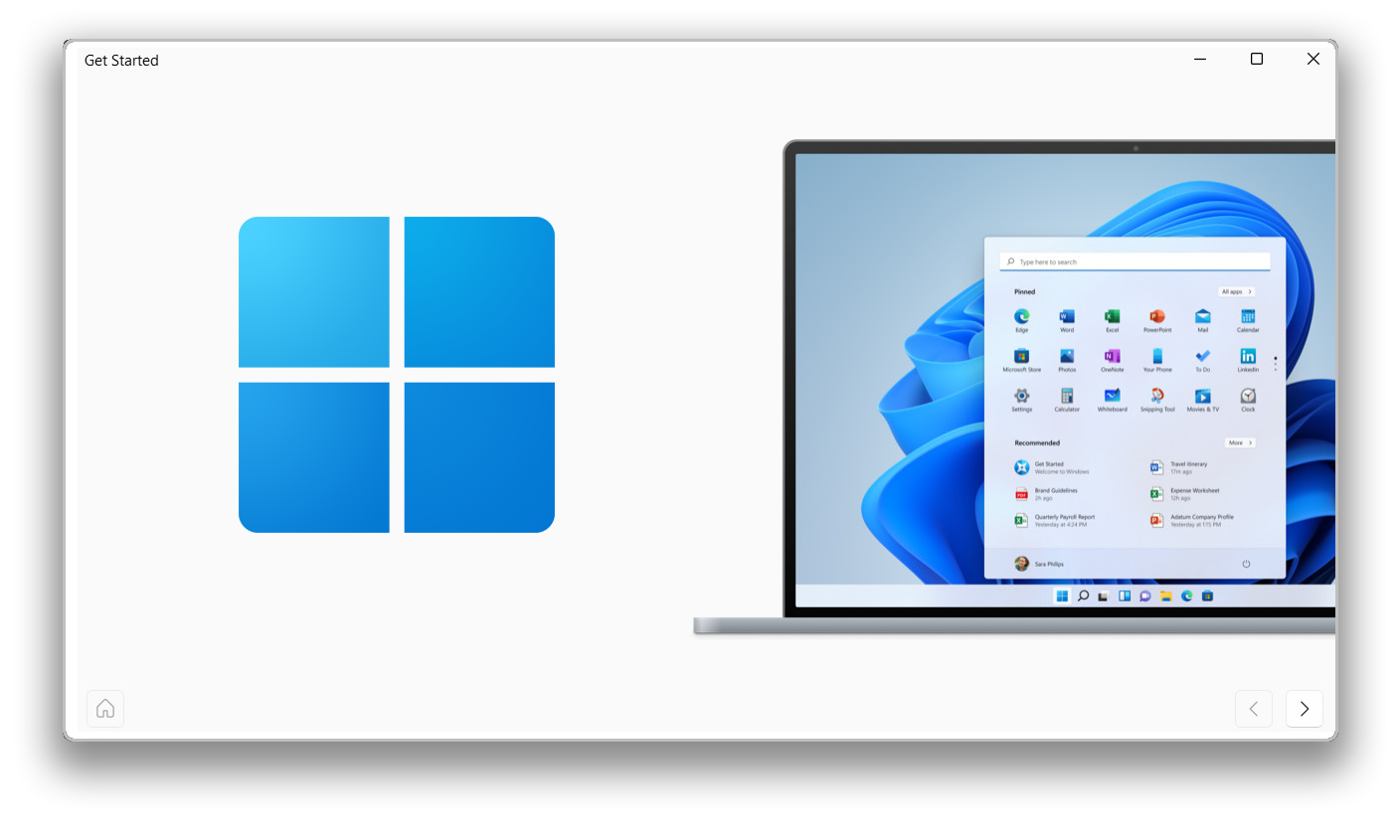
End User Devices User activity monitoring plays an important role in network security and bandwidth management. monitoring and tracking end user behavior on devices, networks, and other company owned it resources help identify internal threats in a network. User activity monitoring tools offer real time tracking of user actions across networks and devices. these solutions help organizations safeguard data and ensure compliance by identifying unusual or unauthorized activity.
Comments are closed.