Encryption Using Lester Hill Cipher Algorithm Pdf
Hill Cipher Encryption Technique Pdf The objective of this paper is to encrypt an text using a technique different from the conventional hill cipher. the hill cipher utilizes matrix manipulations for symmetric encryption, enhancing security through invertible key matrices. Objective of this paper is to overcome the drawback of using a random key matrix in hill cipher algorithm for encryption, where we may not be able to decrypt the encrypted message, if the key matrix is not invertible.

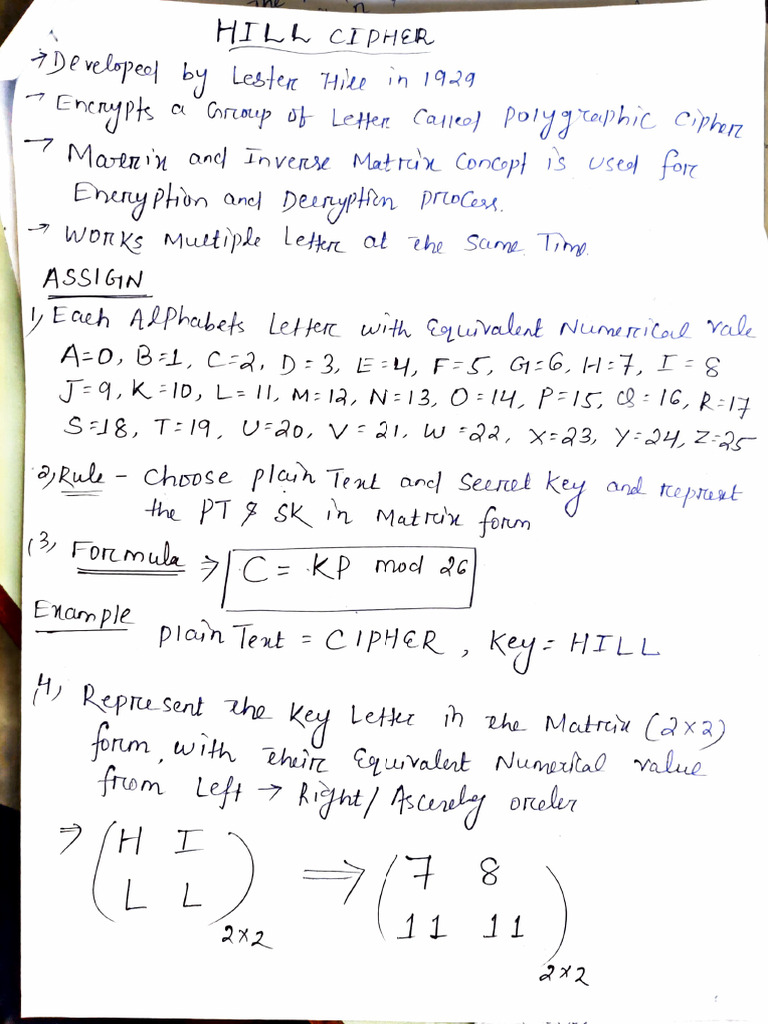
Hill Cipher Pdf Encryption Secure Communication Lester hill of hunter college first introduced his “system” in an article in 1929 published in the american mathematical monthly entitled “cryptology in an algebraic alphabet”. Given the focus of this paper on the hill cipher, which is a symmetric encryption algorithm, the following sections will delve deeper into the principles and applications of symmetric encryption. The purpose of this paper is to illustrate a simple cypher using the application of linear algebra to encrypt and decrypt a message. the main algorithm applied is a version of hill cypher invented in 1929 by lester s. hill at hunter college, new york [3]. Since 1929, many modi cations have been made to the hill cipher in order to improve its security. in this project, we demonstrate how the hill cipher works, implement a 3x3 version of the cipher in matlab, and analyze the cryptographic method.

Pdf Encryption Using Lester Hill Cipher Algorithm The purpose of this paper is to illustrate a simple cypher using the application of linear algebra to encrypt and decrypt a message. the main algorithm applied is a version of hill cypher invented in 1929 by lester s. hill at hunter college, new york [3]. Since 1929, many modi cations have been made to the hill cipher in order to improve its security. in this project, we demonstrate how the hill cipher works, implement a 3x3 version of the cipher in matlab, and analyze the cryptographic method. To encrypt a message using the hill cipher we must first turn our keyword into a key matrix (a 2 × 2 matrix for working with digraphs, a 3 × 3 matrix for working with trigraphs, etc.). To produce cipher text, the method used is to carry out an encryption process based on the hill cipher algorithm. the encryption process is carried out by multiplying the key matrix by the plaintext. In this study, modifications to the hill cipher algorithm were carried out using 2 keywords and 94 ascii characters with the aim of increasing the strength of the hill cipher algorithm. In this lab, matrices are used to encode and decode messages. the ideas are due to lester hill in 1929. hill's patented cipher machine appears in the image below. perhaps the simplest way to encode a message is to simply replace each letter of the alphabet with another letter.

Image Encryption Using Advanced Hill Cipher Algorithm Pdf To encrypt a message using the hill cipher we must first turn our keyword into a key matrix (a 2 × 2 matrix for working with digraphs, a 3 × 3 matrix for working with trigraphs, etc.). To produce cipher text, the method used is to carry out an encryption process based on the hill cipher algorithm. the encryption process is carried out by multiplying the key matrix by the plaintext. In this study, modifications to the hill cipher algorithm were carried out using 2 keywords and 94 ascii characters with the aim of increasing the strength of the hill cipher algorithm. In this lab, matrices are used to encode and decode messages. the ideas are due to lester hill in 1929. hill's patented cipher machine appears in the image below. perhaps the simplest way to encode a message is to simply replace each letter of the alphabet with another letter.

Pdf Parallel Hill Cipher Encryption Algorithm In this study, modifications to the hill cipher algorithm were carried out using 2 keywords and 94 ascii characters with the aim of increasing the strength of the hill cipher algorithm. In this lab, matrices are used to encode and decode messages. the ideas are due to lester hill in 1929. hill's patented cipher machine appears in the image below. perhaps the simplest way to encode a message is to simply replace each letter of the alphabet with another letter.

Advanced Hill Cipher Algorithm For Security Image Pdf Encryption
Comments are closed.