Encrypted Visibility Engine Pdf Transport Layer Security Computing

Transport Layer Security Pdf Transport Layer Security Public Key You can use the encrypted visibility engine (eve) to identify client applications and processes using transport layer security (tls) encryption. eve provides more visibility into the encrypted sessions without decryption. Encrypted visibility engine free download as pdf file (.pdf), text file (.txt) or read online for free. the encrypted visibility engine (eve) enhances visibility into tls encrypted sessions without decryption, allowing administrators to identify applications and enforce policies.

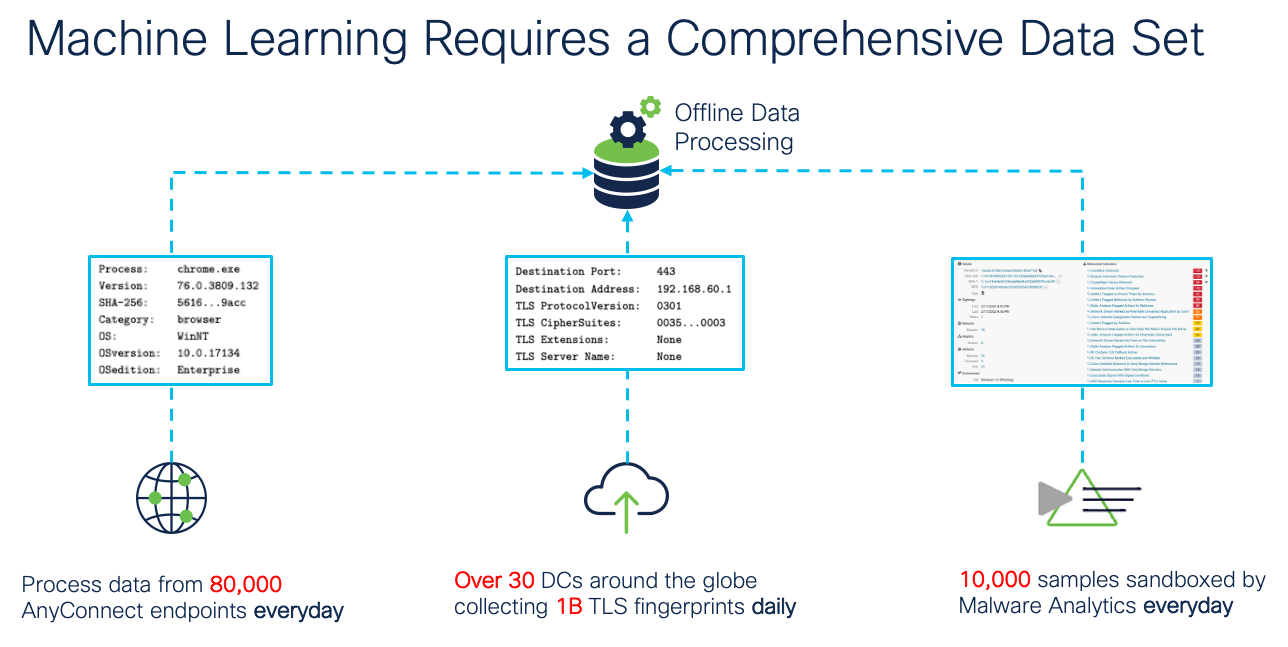
Transport Layer Security Tls A Network Security P Pdf Transport This session will explain decryption logic on the cisco secure firewall in detail, along with examples and demonstrations. we will also look at how to gain visibility into secured traffic without decryption using the machine learning empowered encrypted visibility engine. Encrypted visibility engine (eve) is a feature of the cisco secure firewall that improves encrypted traffic inspection without requiring decryption. encrypted visibility engine (eve) uses transport layer security (tls) encryption to identify client apps and processes. For solutions that achieve visibility through analysis of encrypted data, projects would focus on demonstrating the capabilities and limitations of these emerging tools with respect to each of the four scenarios. This article introduces a complete frame work for building secure and practical network middleboxes, called eve, which enables visibility over encrypted traffic.

Implementation Of Secure Communication With Modbus And Transport Layer For solutions that achieve visibility through analysis of encrypted data, projects would focus on demonstrating the capabilities and limitations of these emerging tools with respect to each of the four scenarios. This article introduces a complete frame work for building secure and practical network middleboxes, called eve, which enables visibility over encrypted traffic. The arrival of tls 1.3 ech challenges all known approaches to visibility into encrypted enterprise and network traffic, and many industry professionals are asking how they will be able to carry out essential network operations when tls 1.3 ech becomes the encryption standard. Through the use of distributed authentication, access control, encryption, and monitoring, organizations can mitigate risks and protect sensitive data in the cloud. Get total asset visibility for every it and security decision. lansweeper delivers ai native asset visibility and context teams trust to act with confidence. The transport mode is the regular mode for packets to travel from a source to its destination in a network — except for the fact that the two endpoints must carry out the security checks on the packets on the basis of the information contained in the authentication header.

Encrypted Visibility Engine Pdf Transport Layer Security Computing The arrival of tls 1.3 ech challenges all known approaches to visibility into encrypted enterprise and network traffic, and many industry professionals are asking how they will be able to carry out essential network operations when tls 1.3 ech becomes the encryption standard. Through the use of distributed authentication, access control, encryption, and monitoring, organizations can mitigate risks and protect sensitive data in the cloud. Get total asset visibility for every it and security decision. lansweeper delivers ai native asset visibility and context teams trust to act with confidence. The transport mode is the regular mode for packets to travel from a source to its destination in a network — except for the fact that the two endpoints must carry out the security checks on the packets on the basis of the information contained in the authentication header.
Encrypted Visibility Engine Get total asset visibility for every it and security decision. lansweeper delivers ai native asset visibility and context teams trust to act with confidence. The transport mode is the regular mode for packets to travel from a source to its destination in a network — except for the fact that the two endpoints must carry out the security checks on the packets on the basis of the information contained in the authentication header.
Comments are closed.