Encrypted Traffic Malware Detection Twiml Pptx

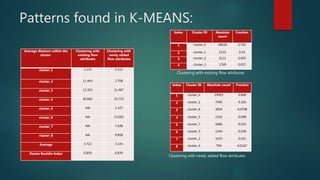
Encrypted Traffic Malware Detection Twiml Pptx Open questions remain around optimal techniques for determining cluster numbers, data standardization methods, and whether supervised learning could provide better results. download as a pptx, pdf or view online for free. Thus, machine learning based approaches have become an important direction for encrypted malicious traffic detection. in this paper, we formulate a universal framework of machine learning based encrypted malicious traffic detection techniques and provided a systematic review.
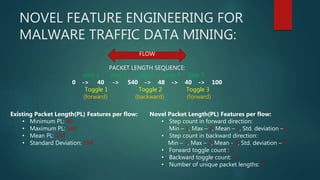
Encrypted Traffic Malware Detection Twiml Pptx We propose using a residual network to classify encrypted network traffic by treating statistical data from packet headers as images. residual networks solve gradient vanishing problems and allow for deeper neural networks that are better at classifying complex data. On the physical testbed, we replay 92 kinds of malicious traffic, including 48 attacks with encrypted malicious traffic: traditional brute attacks (e.g., amplification attacks). In an era where cyber threats continually evolve, the detection of malware within encrypted network traffic remains a formidable challenge. this study presents. Filter out all non encrypted traffic sessions in the mixed traffic dataset. (this ensures that there are no non encrypted traffic sessions at the session level that will affect the encrypted traffic analysis.).
Encrypted Traffic Malware Detection Twiml Pptx In an era where cyber threats continually evolve, the detection of malware within encrypted network traffic remains a formidable challenge. this study presents. Filter out all non encrypted traffic sessions in the mixed traffic dataset. (this ensures that there are no non encrypted traffic sessions at the session level that will affect the encrypted traffic analysis.). Advantages of ml in encrypted traffic detection machine learning algorithms can analyze vast amounts of data in real time, adapting to new threats as they emerge. their ability to handle both protocol agnostic and protocol specific features makes them versatile, ensuring robust. By utilizing advanced algorithms and data analysis, the goal is to improve detection accuracy, minimize false positives, and enhance cybersecurity by identifying and mitigating known malware signatures efficiently. In this paper, we propose wt net, a machine learning based approach for android malware detection, which first characterizes android application traffic as a grayscale graph and transforms the traffic detection problem into an image classification problem. As a countermeasure, many malware detection methods are proposed to identify malicious behaviours based on traffic characteristics. however, the emerging encryption and evasion techniques pose substantial barriers to the full exploitation of network information.

Encrypted Traffic Malware Detection Twiml Pptx Advantages of ml in encrypted traffic detection machine learning algorithms can analyze vast amounts of data in real time, adapting to new threats as they emerge. their ability to handle both protocol agnostic and protocol specific features makes them versatile, ensuring robust. By utilizing advanced algorithms and data analysis, the goal is to improve detection accuracy, minimize false positives, and enhance cybersecurity by identifying and mitigating known malware signatures efficiently. In this paper, we propose wt net, a machine learning based approach for android malware detection, which first characterizes android application traffic as a grayscale graph and transforms the traffic detection problem into an image classification problem. As a countermeasure, many malware detection methods are proposed to identify malicious behaviours based on traffic characteristics. however, the emerging encryption and evasion techniques pose substantial barriers to the full exploitation of network information.
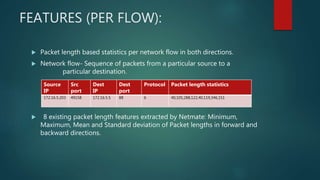
Encrypted Traffic Malware Detection Twiml Pptx In this paper, we propose wt net, a machine learning based approach for android malware detection, which first characterizes android application traffic as a grayscale graph and transforms the traffic detection problem into an image classification problem. As a countermeasure, many malware detection methods are proposed to identify malicious behaviours based on traffic characteristics. however, the emerging encryption and evasion techniques pose substantial barriers to the full exploitation of network information.
Encrypted Traffic Malware Detection Twiml Pptx
Comments are closed.