Encrypted Traffic Inspection Lightboard Series

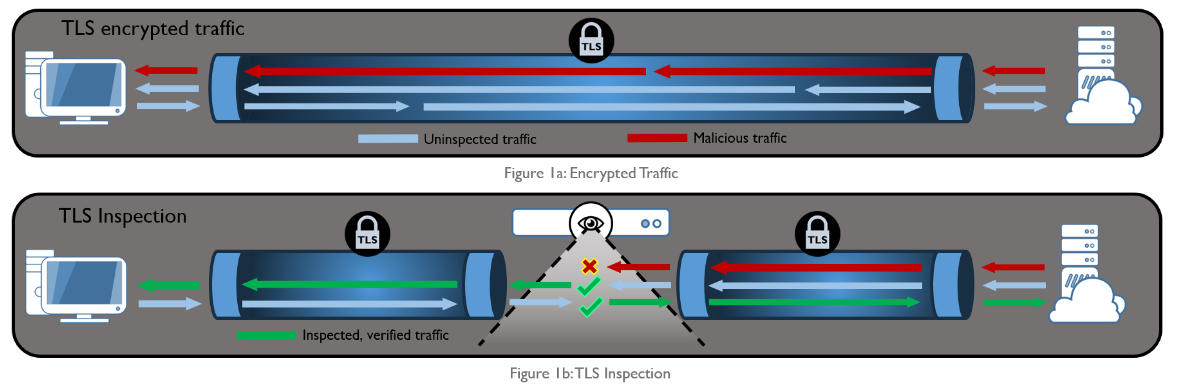
Encrypted Traffic Inspection Learn how cyber criminals are breaching your defenses, what they do once inside and what you can do about it. When you connect the cisco firepower threat defense into the f5 ssl orchestrator you get a very powerful inspection solution for encrypted traffic. check out the video to learn more!.

Encrypted Traffic Inspection Learn how cyber criminals are breaching your defenses, what they do once inside and what you can do about it. Array’s asf series can integrate with the encrypted traffic inspection solution to provide high performance application layer visibility and protection for inbound traffic. Specialty experts restores full traffic visibility without sacrificing speed or privacy. our encrypted traffic inspection (eti) solution delivers high throughput, low latency decryption to empower your entire security stack. Now that the majority of web traffic is encrypted with forward secret ciphers, how do you monitor your incoming web traffic for threats? david holmes light boards the ultimate ssl visibility architecture for inline inspection.
Encrypted Traffic Insights Specialty experts restores full traffic visibility without sacrificing speed or privacy. our encrypted traffic inspection (eti) solution delivers high throughput, low latency decryption to empower your entire security stack. Now that the majority of web traffic is encrypted with forward secret ciphers, how do you monitor your incoming web traffic for threats? david holmes light boards the ultimate ssl visibility architecture for inline inspection. This blog covers the best practices for enabling encrypted traffic inspection after an initial zscaler internet access deployment. we’ll also look at the insights traffic inspection provides so you can further tune your inspection policies for maximum effectiveness. Learn how cybersecurity and networking solution vendors can use enea qosmos next gen dpi for visibility into encrypted and evasive traffic. Learn how encrypted traffic insights detects threats inside encrypted traffic by analyzing connection metadata and applying ai ml models without decrypting the payload, preserving privacy and performance while enabling real time security. | hpe asia pac. In this #gigamon lightboard series, chris borales discusses encrypted traffic inspection and why it’s critical for a mature security posture. ow.ly hknm1041mcf learn how cyber.

Encrypted Traffic Inspection Lags As Malware Rises A10 Networks This blog covers the best practices for enabling encrypted traffic inspection after an initial zscaler internet access deployment. we’ll also look at the insights traffic inspection provides so you can further tune your inspection policies for maximum effectiveness. Learn how cybersecurity and networking solution vendors can use enea qosmos next gen dpi for visibility into encrypted and evasive traffic. Learn how encrypted traffic insights detects threats inside encrypted traffic by analyzing connection metadata and applying ai ml models without decrypting the payload, preserving privacy and performance while enabling real time security. | hpe asia pac. In this #gigamon lightboard series, chris borales discusses encrypted traffic inspection and why it’s critical for a mature security posture. ow.ly hknm1041mcf learn how cyber.
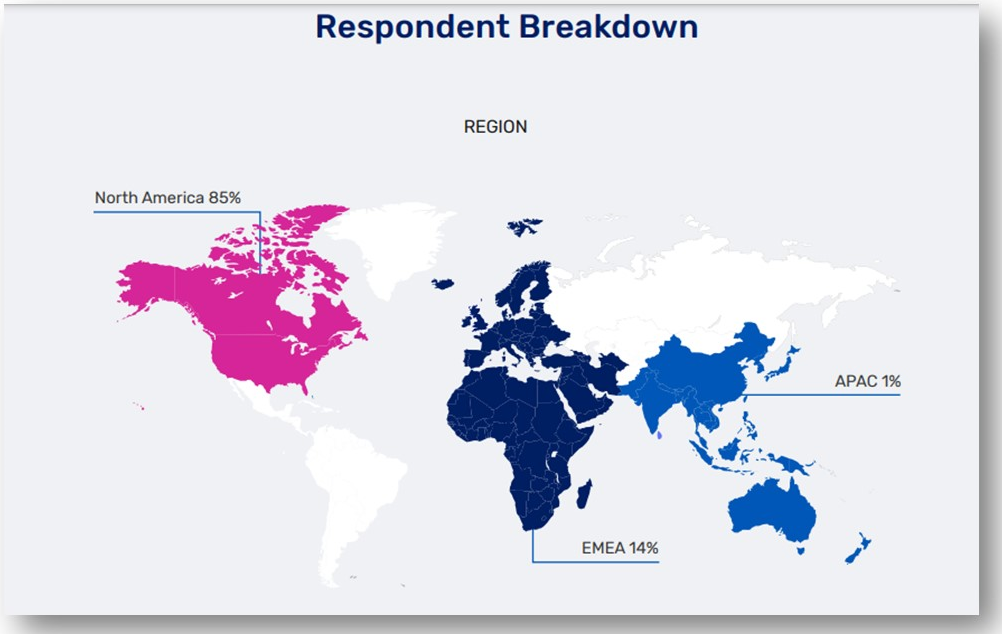
Encrypted Traffic Inspection For Cyber Security Survey Report Learn how encrypted traffic insights detects threats inside encrypted traffic by analyzing connection metadata and applying ai ml models without decrypting the payload, preserving privacy and performance while enabling real time security. | hpe asia pac. In this #gigamon lightboard series, chris borales discusses encrypted traffic inspection and why it’s critical for a mature security posture. ow.ly hknm1041mcf learn how cyber.
Nsa Publishes Advisory Addressing Encrypted Traffic Inspection Risks
Comments are closed.