Encrypted Data Patterns Pdf Standardized Tests Tests

Cryptography Tests Pdf Public Key Cryptography Cryptography This document contains many sections with repeating patterns of symbols. it appears to be providing some type of coded information across many pages but the exact meaning is unclear from the text alone. This publication provides the basic design and configuration of the aesavs. it includes the specifications for the three categories of tests that make up the aesavs, i.e., the known answer test (kat), the multi block message test (mmt), and the monte carlo test (mct).
How To Test Encrypted Data Newsoftwares Net Blog In this paper, we propose new provably correct, secure, and relatively e cient (compared to similar existing schemes) public and private key based constructions that allow arbitrary pattern matching over encrypted data while protecting both the data to be analyzed and the patterns to be matched. This document contains the parameters used in the production of the iec61174 test data for encrypted encs (iec61174 ed3, annex j) and the test scripts that accompany the test data. This paper compares existing statistical tests on a large, standardized dataset and shows that current approaches consistently fail to distinguish encrypted and compressed data on both. In this paper, we propose new provably correct, secure, and relatively efficient (compared to similar existing schemes) public and private key based constructions that allow arbitrary pattern matching over encrypted data while protecting both the data to be analyzed and the patterns to be matched.

Data Encryption Standard Pdf Cryptanalysis Encryption This paper compares existing statistical tests on a large, standardized dataset and shows that current approaches consistently fail to distinguish encrypted and compressed data on both. In this paper, we propose new provably correct, secure, and relatively efficient (compared to similar existing schemes) public and private key based constructions that allow arbitrary pattern matching over encrypted data while protecting both the data to be analyzed and the patterns to be matched. While it is a straightforward operation when performed on plaintext data, it becomes a challenging task when the privacy of both the analyzed data and the analysis patterns must be preserved. Pattern matching is essential in applications such as deep packet inspection (dpi), searching on genomic data, or analyzing medical data. a simple task to do on plaintext data, pattern matching is much harder to do when the privacy of the data must be preserved. Our book provides the reader with a deep understanding of how modern cryp tographic schemes work. we introduce the necessary mathematical concepts in a way that is accessible for every reader with a minimum background in college level calculus. The p25 committees are working on standards for link layer encryption, which would allow encryption of the associated signaling so that unit ids and other data regarding encrypted communications would be protected from monitoring.
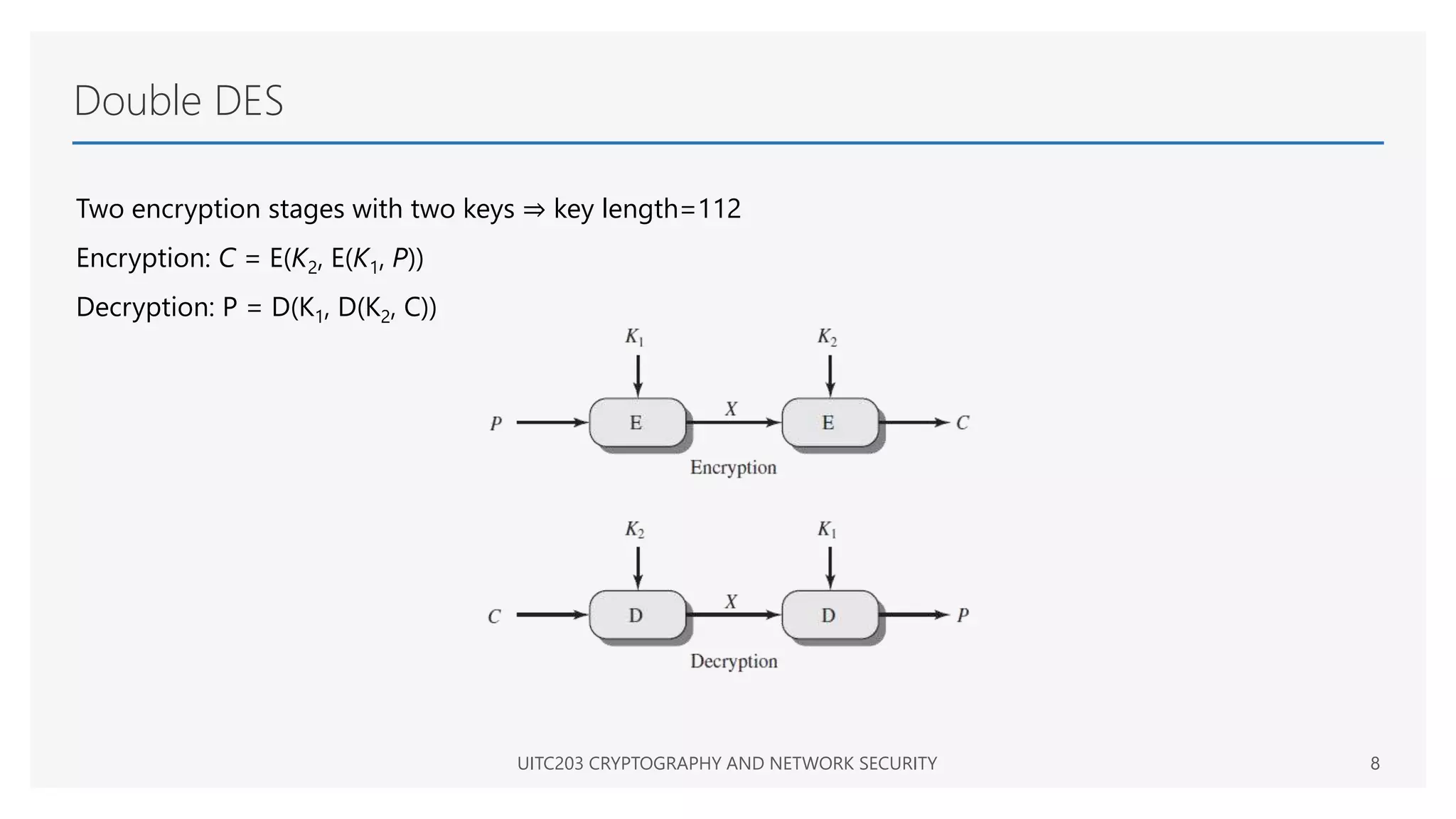
Data Encryption Standard Pptx While it is a straightforward operation when performed on plaintext data, it becomes a challenging task when the privacy of both the analyzed data and the analysis patterns must be preserved. Pattern matching is essential in applications such as deep packet inspection (dpi), searching on genomic data, or analyzing medical data. a simple task to do on plaintext data, pattern matching is much harder to do when the privacy of the data must be preserved. Our book provides the reader with a deep understanding of how modern cryp tographic schemes work. we introduce the necessary mathematical concepts in a way that is accessible for every reader with a minimum background in college level calculus. The p25 committees are working on standards for link layer encryption, which would allow encryption of the associated signaling so that unit ids and other data regarding encrypted communications would be protected from monitoring.

Data Encryption Standards Pdf Cryptography Key Cryptography Our book provides the reader with a deep understanding of how modern cryp tographic schemes work. we introduce the necessary mathematical concepts in a way that is accessible for every reader with a minimum background in college level calculus. The p25 committees are working on standards for link layer encryption, which would allow encryption of the associated signaling so that unit ids and other data regarding encrypted communications would be protected from monitoring.
How To Test Encrypted Data Newsoftwares Net Blog
Comments are closed.