Encrypt And Decrypt Data With Rsa Wstutorial
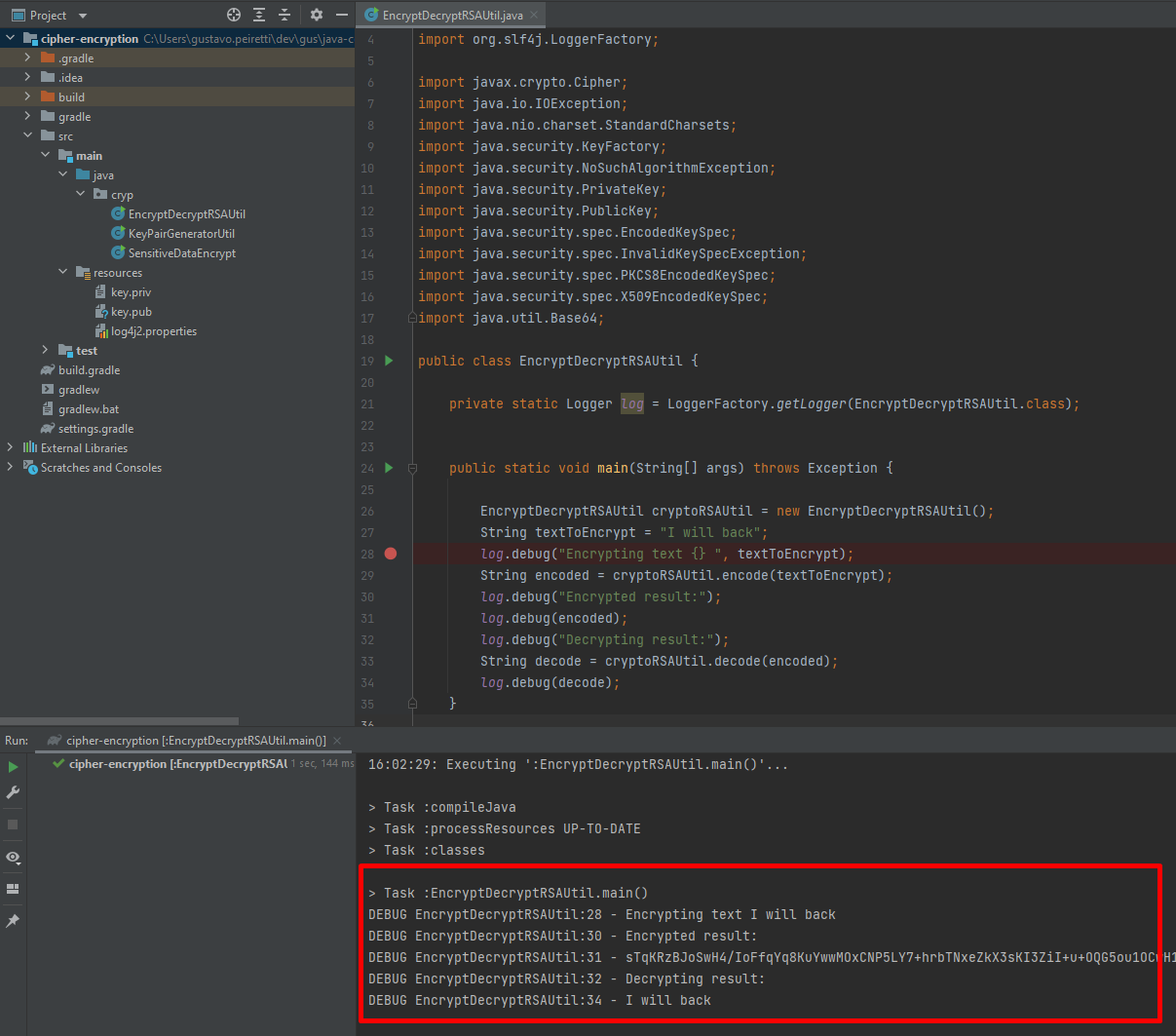
How To Encrypt And Decrypt Using Rsa Keys With Java Home A quik tutorial about how to encrypt and decrypt using rsa public key and private key. Asymmetric key ciphers exercises: rsa encrypt decrypt in this exercise you shall encrypt and decrypt messages using the rsa public key cryptosystem.
Python Rsa Encrypt Decrypt Example Devrescue Now let's demonstrate how the rsa algorithms works by a simple example in python. the below code will generate random rsa key pair, will encrypt a short message and will decrypt it back to its original form, using the rsa oaep padding scheme. Explore rsa encryption techniques, key generation, and security vulnerabilities in this comprehensive lab report on asymmetric encryption methods. Encryption and decryption — you could use public key to encrypt message, and use private key to decrypt message. in this use case, you share public key to your counter party, so, they. Encrypt and decrypt data securely with the rsa encryption tool on anycript. utilize the robust rsa algorithm for asymmetric encryption to safeguard sensitive information. enhance your data privacy and security with our user friendly, client side processing.
Github Blindma1den Rsa Encrypt And Decrypt This Project Creates A Encryption and decryption — you could use public key to encrypt message, and use private key to decrypt message. in this use case, you share public key to your counter party, so, they. Encrypt and decrypt data securely with the rsa encryption tool on anycript. utilize the robust rsa algorithm for asymmetric encryption to safeguard sensitive information. enhance your data privacy and security with our user friendly, client side processing. Free online rsa encryption and decryption tool. generates rsa key pairs (512–4096 bit), encrypt and decrypt using oaep or pkcs#1 padding. Best practices in 2025 🔐 use aes 256 for symmetric encryption (ensure jce unlimited policy is enabled) 🔑 use rsa ecc for key exchange only, not for full data 🧂 always salt and hash passwords (bcrypt argon2) 🔁 use iv (initialization vector) for block ciphers 🔄 rotate encryption keys periodically 🚫 never log or expose raw keys or decrypted data 🧪 always test decryption edge. From online banking and cloud storage to messaging apps and enterprise systems, encryption ensures that sensitive data remains confidential, tamper proof, and secure. Public key cryptography: rsa algorithm is a public key cryptography algorithm, which means that it uses two different keys for encryption and decryption. the public key is used to encrypt the data, while the private key is used to decrypt the data.

How To Encrypt And Decrypt Data Using Rsa In Java Smattme Free online rsa encryption and decryption tool. generates rsa key pairs (512–4096 bit), encrypt and decrypt using oaep or pkcs#1 padding. Best practices in 2025 🔐 use aes 256 for symmetric encryption (ensure jce unlimited policy is enabled) 🔑 use rsa ecc for key exchange only, not for full data 🧂 always salt and hash passwords (bcrypt argon2) 🔁 use iv (initialization vector) for block ciphers 🔄 rotate encryption keys periodically 🚫 never log or expose raw keys or decrypted data 🧪 always test decryption edge. From online banking and cloud storage to messaging apps and enterprise systems, encryption ensures that sensitive data remains confidential, tamper proof, and secure. Public key cryptography: rsa algorithm is a public key cryptography algorithm, which means that it uses two different keys for encryption and decryption. the public key is used to encrypt the data, while the private key is used to decrypt the data.
Comments are closed.