Encoded Payloads Are Sneaky

Crazy Payloads To Test If None Are Working Pdf By disguising malicious payloads in hex encoded characters, attackers can trick applications into executing harmful scripts, leading to severe consequences such as session hijacking, phishing,. However, attackers can bypass these filters by using various encoding techniques, manipulating html tags, and exploiting event handlers. this repository contains 100 xss payloads that are designed to bypass common xss filters and web application firewalls (wafs).
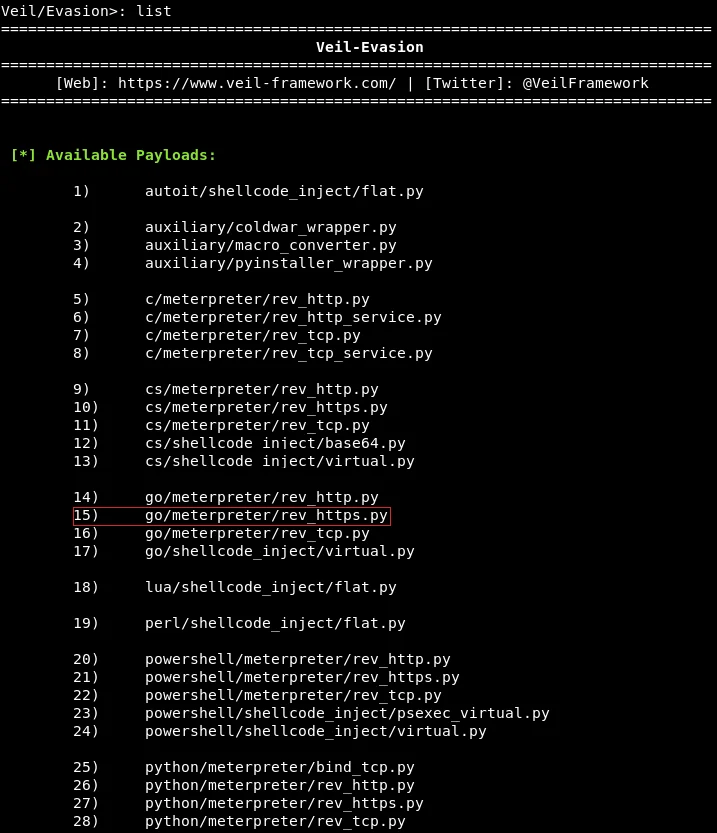
Overview Of Payloads Ethical Hacking Understand the mechanics of a base64 encoded xss payload and how it evades primitive filters. learn to identify and test for this vulnerability in web applications. Attackers use various encoding methods to obscure malicious payloads and bypass xss filters that scan for specific patterns. encoding techniques exploit how browsers interpret character representations, allowing scripts to execute despite being altered from their original form. Cross site scripting (xss) is a type of security vulnerability typically found in web applications. it allows attackers to inject malicious scripts into web pages viewed by other users. there are three main types of xss attacks: stored xss, reflected xss, and dom based xss. Encoding and obfuscation one of the most effective ways to bypass filters is encoding or obfuscating the payloads. encoding characters like <, >, and " into their html or url encoded equivalents can evade filters that look for these special characters.
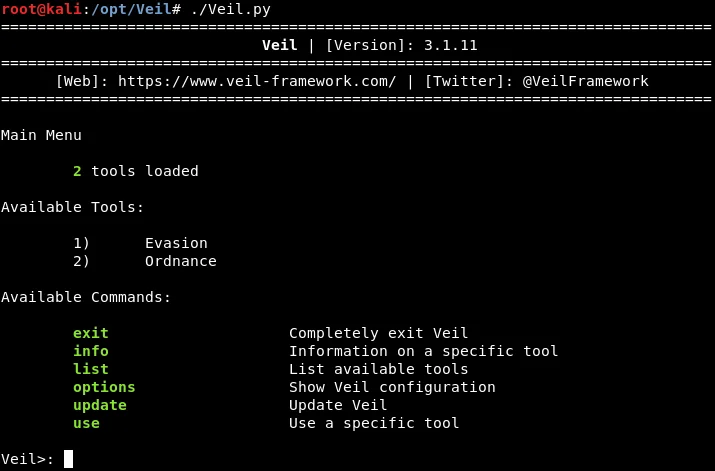
Overview Of Payloads Ethical Hacking Cross site scripting (xss) is a type of security vulnerability typically found in web applications. it allows attackers to inject malicious scripts into web pages viewed by other users. there are three main types of xss attacks: stored xss, reflected xss, and dom based xss. Encoding and obfuscation one of the most effective ways to bypass filters is encoding or obfuscating the payloads. encoding characters like <, >, and " into their html or url encoded equivalents can evade filters that look for these special characters. Explore advanced cybersecurity payload encoding techniques to enhance attack stealth, protect against detection, and improve penetration testing strategies. #cybersecurity #linux #hacker. Attackers use various encoding and obfuscation techniques to bypass security controls implemented in web applications. these methods aim to hide malicious payloads to avoid detection by. Adversaries may embed payloads within other files to conceal malicious content from defenses. otherwise seemingly benign files (such as scripts and executables) may be abused to carry and obfuscate malicious payloads and content.
Comments are closed.