Enable Private Connectivity Using Aws Privatelink Databricks
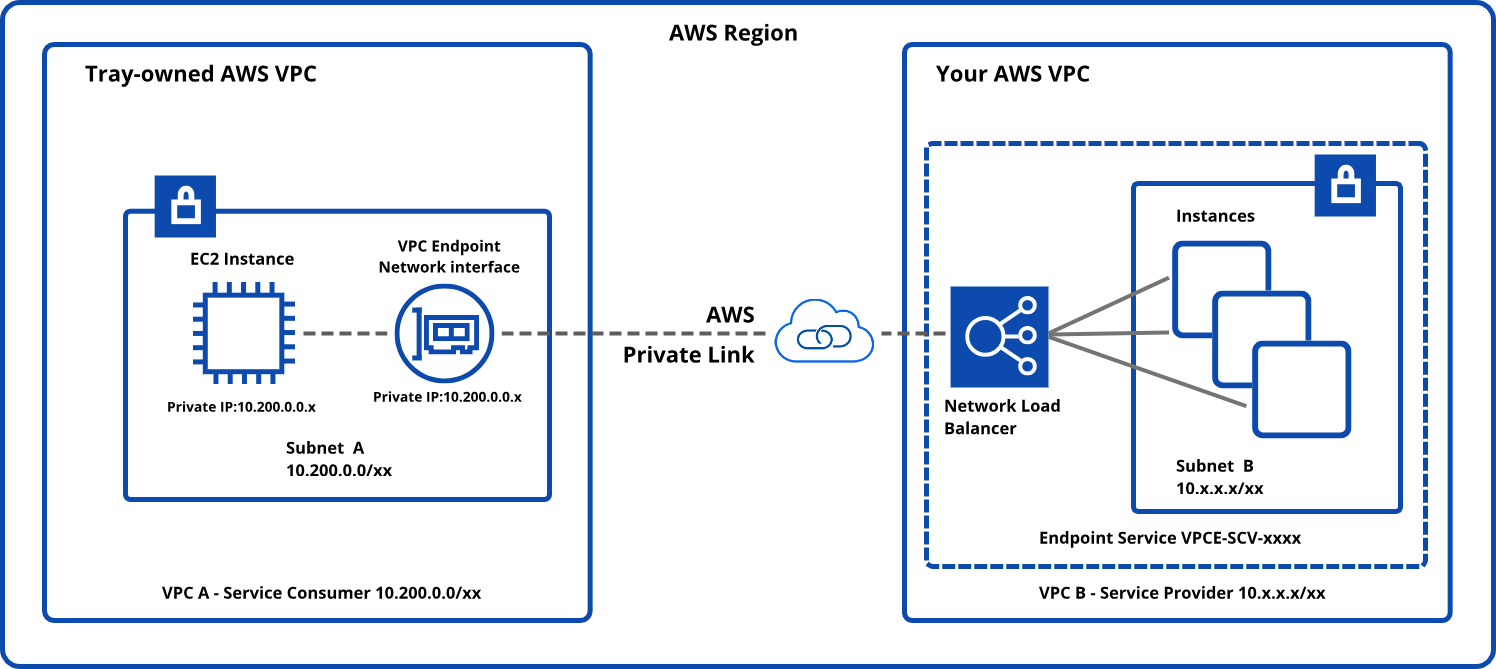
Aws Privatelink Aws Connectivity Tray Ai Documentation This page covers configuration steps for inbound private connectivity between users and their databricks workspaces. to enhance the security of your workspace's serverless implementation, you must use inbound private connectivity. The following steps walk you through the setup of a databricks aws privatelink endpoint in the dbt multi tenant environment. private connection endpoints can't connect across cloud providers (aws, azure, and gcp).

Aws Privatelink Amazon Virtual Private Cloud Connectivity Options This front end privatelink connection allows users to connect to the databricks web application, rest api, and databricks connect api over a vpc interface endpoint. for details about aws privatelink in databricks and the network flow in a typical implementation, explore the databricks documentation . Databricks privatelink support enables private connectivity between users and their databricks workspaces and between clusters on the data plane and core services on the control plane within the databricks workspace infrastructure. Databricks privatelink support enables private connectivity between users and their databricks workspaces and between clusters on the data plane and core services on the control plane within the databricks workspace infrastructure. In this blog, we are going to show how to leverage route 53 inbound endpoints to enable dns name resolution of workspaces with privatelink enabled for the front end interface.

Leveraging Singlestoredb Cloud Private Connectivity Using Aws Databricks privatelink support enables private connectivity between users and their databricks workspaces and between clusters on the data plane and core services on the control plane within the databricks workspace infrastructure. In this blog, we are going to show how to leverage route 53 inbound endpoints to enable dns name resolution of workspaces with privatelink enabled for the front end interface. This document provides a step by step guide for configuring aws privatelink for databricks, ensuring secure connectivity with chaos genius to access the databricks warehouse for querying the metadata. They enable instances within the vpc to communicate with these services using aws privatelink network as if they were within the same network, without exposing them to the public internet. You can configure aws privatelink for databricks, rds postgres, redshift, and snowflake. only warehouses located in regions us east 1, us east 2, us west 2, or eu west 1 are eligible. This page provides configuration steps to enable classic compute plane (back end) private connectivity for aws private link. to enable inbound private connectivity to databricks, see configure inbound privatelink.
Comments are closed.