Enable Disable Password Or Key Based Authentication
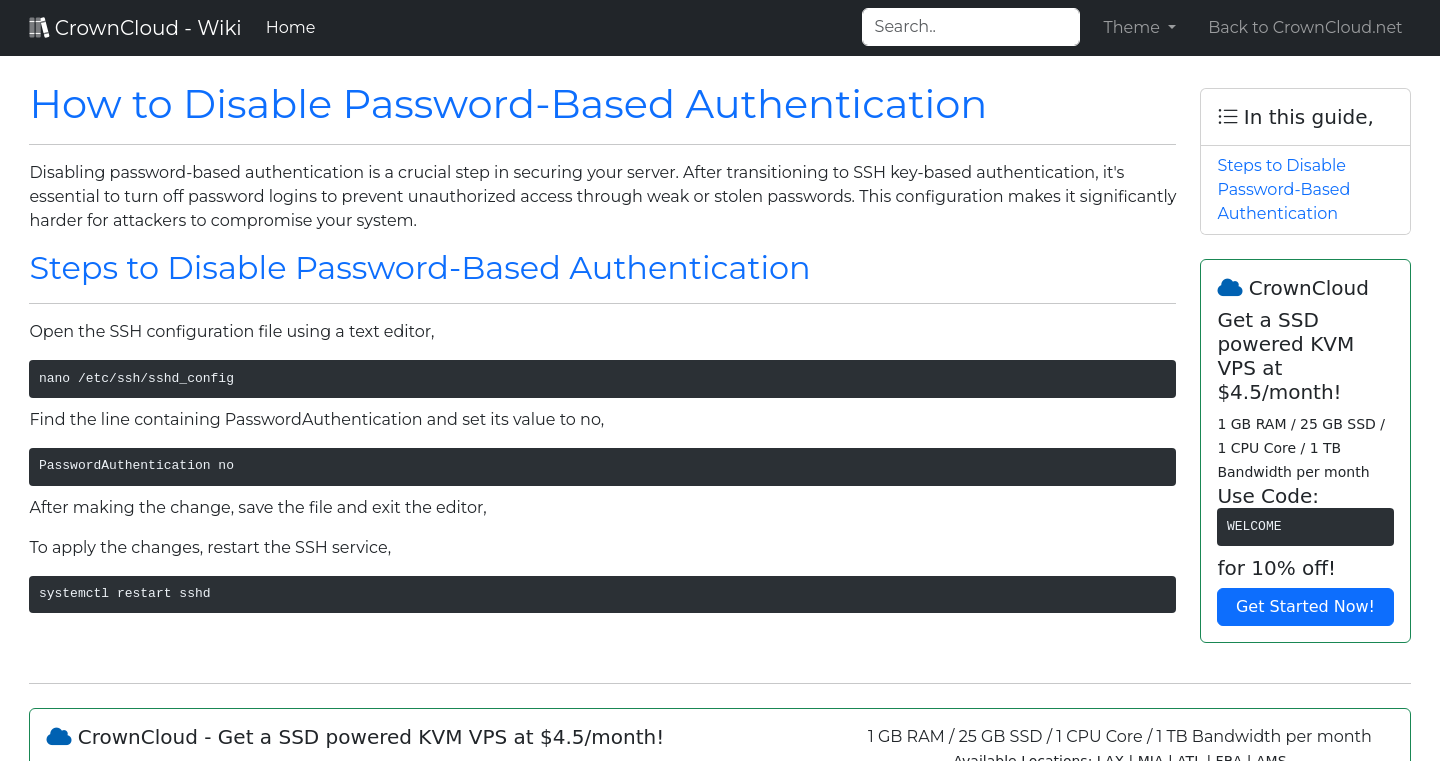
Crowncloud Wiki How To Disable Password Based Authentication Learn how to improve linux ubuntu server security by disabling password based ssh authentication and using ssh keys for secure, encrypted access. safeguard your server against attacks. How to setup ssh key authentication and turn off password login overview: this article outlines how to secure ssh by enabling key based authentication and disabling password login via the sshd configuration file.
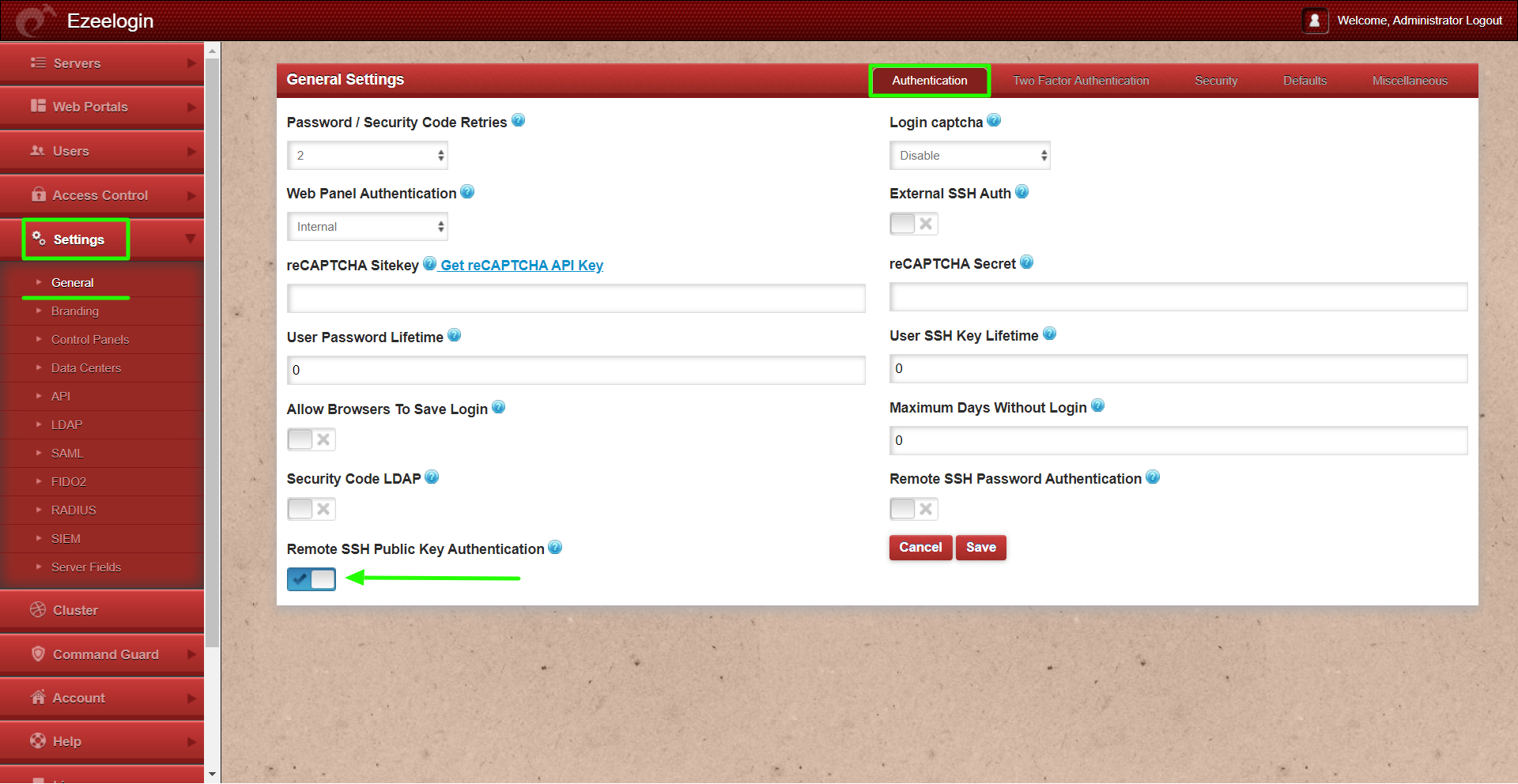
Enable Disable Password Or Key Based Authentication You should now have ssh key based authentication configured and running on your server, allowing you to sign in without providing an account password. from here, there are many directions you can head. This page explains to you how to generate an ssh key and disable password authentication on the linux or unix based system. for demo purposes, i am using a ubuntu linux here, but it should work with other linux distros such as centos rhel fedora debian and so on. Disable ssh password login and switch to key based authentication to block brute force attacks on linux servers. Instead of a password that can be guessed, ssh keys use public key cryptography that is mathematically unfeasible to brute force. this guide walks you through generating keys, deploying them, disabling password authentication, and hardening your ssh configuration for production.
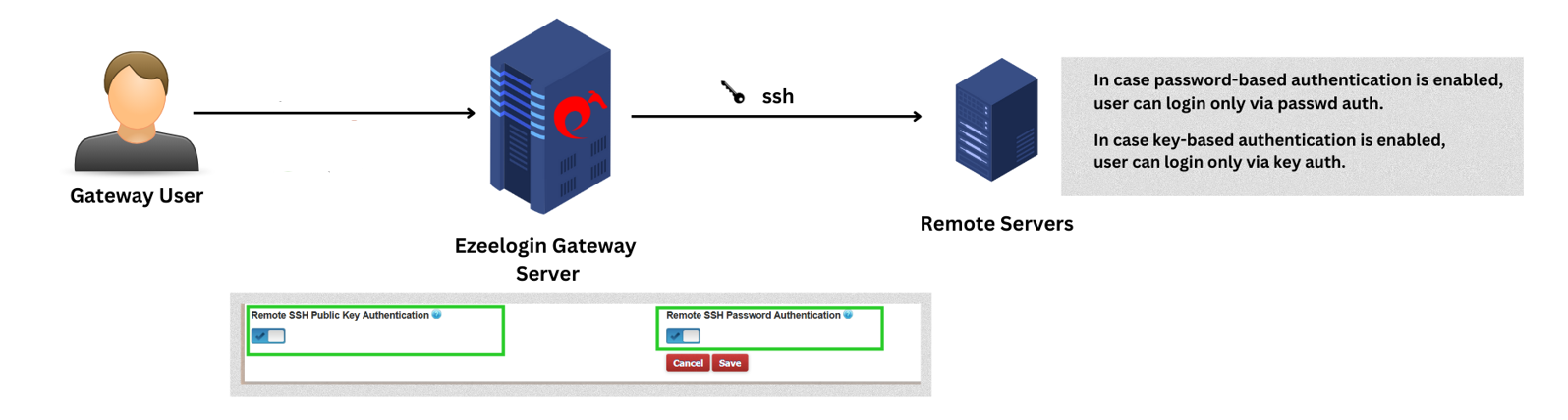
Enable Disable Password Or Key Based Authentication Disable ssh password login and switch to key based authentication to block brute force attacks on linux servers. Instead of a password that can be guessed, ssh keys use public key cryptography that is mathematically unfeasible to brute force. this guide walks you through generating keys, deploying them, disabling password authentication, and hardening your ssh configuration for production. This article delves into the inner workings of ssh key based authentication, explaining its advantages and providing a comprehensive, step by step tutorial on its implementation, ensuring your systems are fortified against unauthorized access. This guide provides a detailed explanation of how to enable or disable ssh password authentication, by modifying the ssh server configuration, as well as how to verify settings, and test access to prevent lockout. Learn how to set up passwordless ssh login using ssh keys. this guide covers generating key pairs, copying public keys, and disabling password authentication. To enhance security, it is recommended to disable ssh password login and allow access only through private key authentication. below are the steps to achieve this on linux and macos.
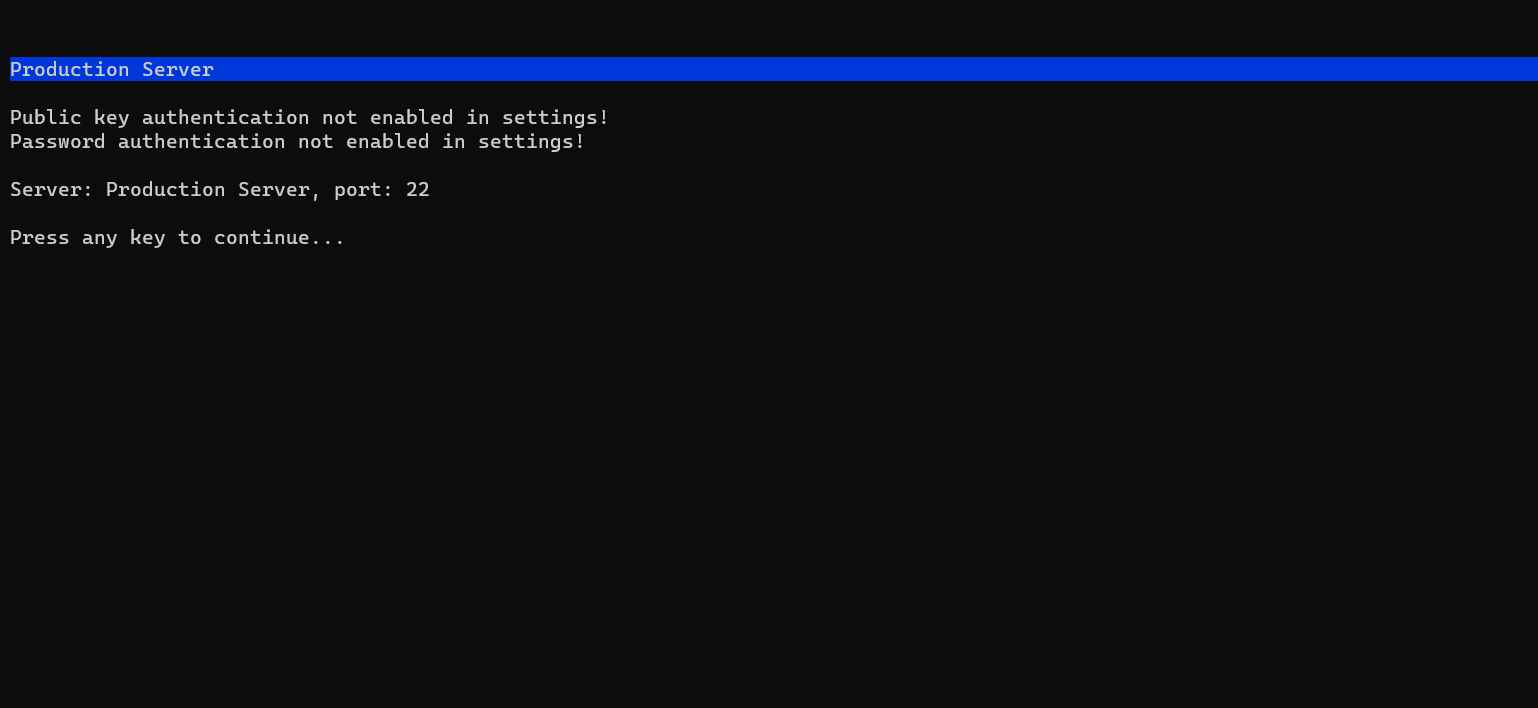
Enable Disable Password Or Key Based Authentication This article delves into the inner workings of ssh key based authentication, explaining its advantages and providing a comprehensive, step by step tutorial on its implementation, ensuring your systems are fortified against unauthorized access. This guide provides a detailed explanation of how to enable or disable ssh password authentication, by modifying the ssh server configuration, as well as how to verify settings, and test access to prevent lockout. Learn how to set up passwordless ssh login using ssh keys. this guide covers generating key pairs, copying public keys, and disabling password authentication. To enhance security, it is recommended to disable ssh password login and allow access only through private key authentication. below are the steps to achieve this on linux and macos.

How To Enable Ssh Key Based Authentication Passwordless Ssh Learn how to set up passwordless ssh login using ssh keys. this guide covers generating key pairs, copying public keys, and disabling password authentication. To enhance security, it is recommended to disable ssh password login and allow access only through private key authentication. below are the steps to achieve this on linux and macos.

Key Based Authentication Using Cryptographic Access Controls Garantir
Comments are closed.