Enable Api Code Scanning Discovery

Continuous Api Scanning Why Developers Care F5 solutions can detect and protect apis during the full api develoment lifecycle which includes also to learn api endpoints and further information to e.g. build the schema from the source code the developers create and maintain on the code repository. Use the rest api to retrieve and update code scanning alerts from a repository.
Api Scanning Hostedscan Tech Docs Use traceable code scanning to uncover shadow and zombie apis in your repositories. connect private or open source repos, trigger scans from the ui or cli, and explore detailed openapi specifications in yaml or json. In this article, we’ll explore the ins and outs of api discovery, including the business impact of api security failures and effective strategies to make api discovery easy, continuous, and contextual. F5 solutions can detect and protect apis during the full api develoment lifecycle which includes also to learn api endpoints and further information to e.g. build the schema from the source code the developers create and maintain on the code repository. This document provides instructions on configuring api discovery on the f5® distributed cloud services platform. this core capability is essential for dynamically identifying and monitoring your application's api endpoints.
Api Scanning Hostedscan Tech Docs F5 solutions can detect and protect apis during the full api develoment lifecycle which includes also to learn api endpoints and further information to e.g. build the schema from the source code the developers create and maintain on the code repository. This document provides instructions on configuring api discovery on the f5® distributed cloud services platform. this core capability is essential for dynamically identifying and monitoring your application's api endpoints. If you skipped the lab2 “enable code scanning discovery, edit your load balancer again, go to api protection and enable api discovery (keep the default settings). Using the instructions provided in this document, you can enable the api endpoint markup for your application, inspect the discovered api endpoints, and monitor the related pdfs in distributed cloud service mesh. One effective architecture for api discovery involves deploying distributed cloud inline with the traffic flow. this approach not only provides visibility into the apis within your environment but also simplifies the implementation of robust security controls around these apis. In this section, we will protect the same modern application with f5 distributed cloud, but we will enable the dynamic protection where secops apply the api discovery and validation.
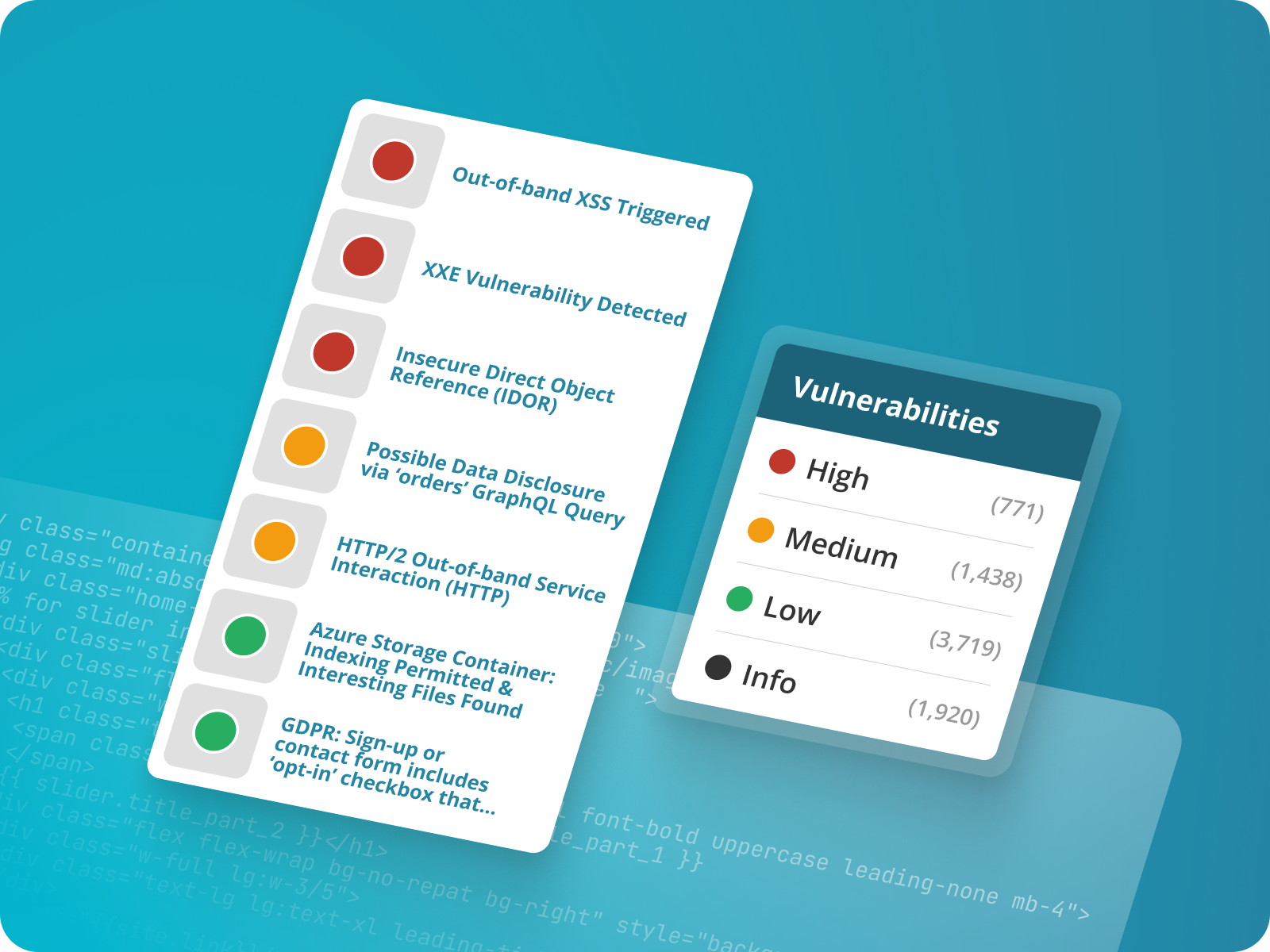
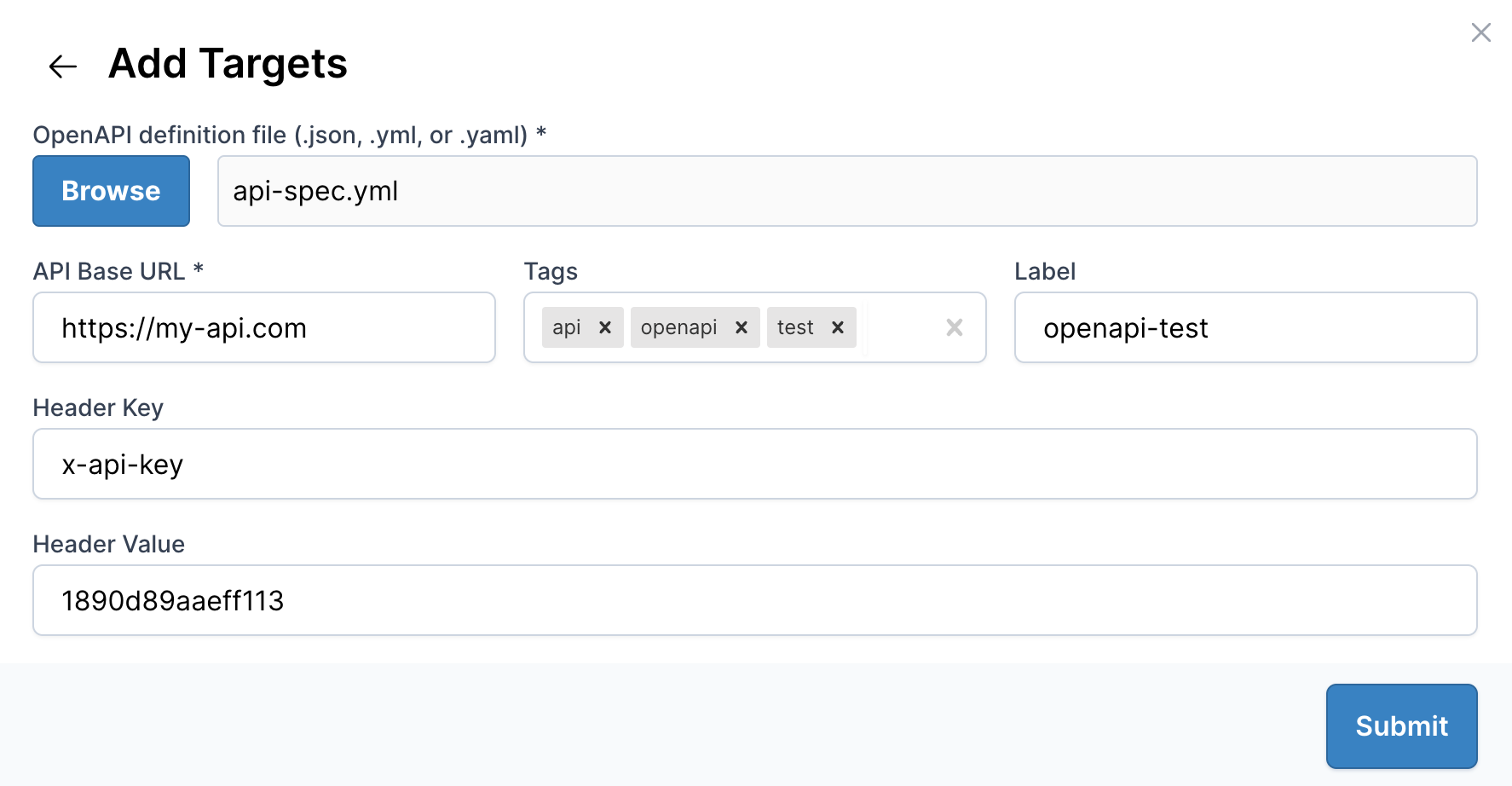
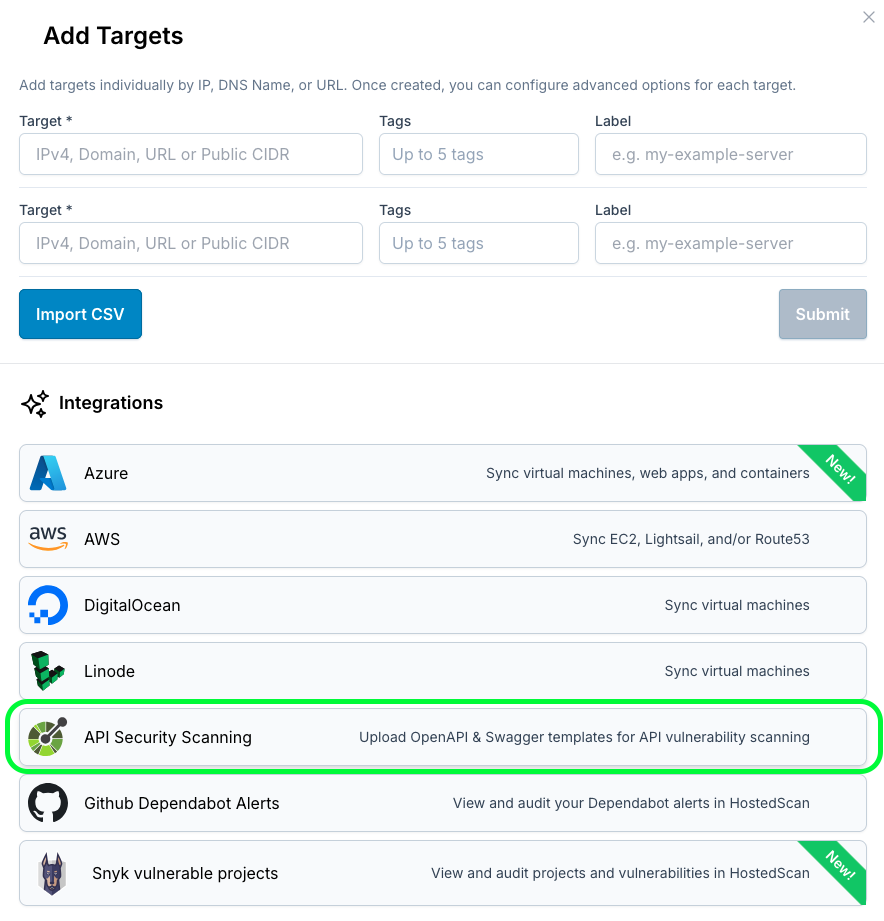
Api Security Scanning If you skipped the lab2 “enable code scanning discovery, edit your load balancer again, go to api protection and enable api discovery (keep the default settings). Using the instructions provided in this document, you can enable the api endpoint markup for your application, inspect the discovered api endpoints, and monitor the related pdfs in distributed cloud service mesh. One effective architecture for api discovery involves deploying distributed cloud inline with the traffic flow. this approach not only provides visibility into the apis within your environment but also simplifies the implementation of robust security controls around these apis. In this section, we will protect the same modern application with f5 distributed cloud, but we will enable the dynamic protection where secops apply the api discovery and validation.
Comments are closed.