Effective Threat Modeling Practices Identifying And Mitigating
Threat Modeling Framework Threat Modeling This comprehensive guide delves deep into the intricacies of threat modeling, exploring various frameworks, methodologies, tools, and best practices to equip security professionals and. This comprehensive guide delves deep into the intricacies of threat modeling, exploring various frameworks, methodologies, tools, and best practices to equip security professionals and organizations with the knowledge to enhance their security posture effectively.

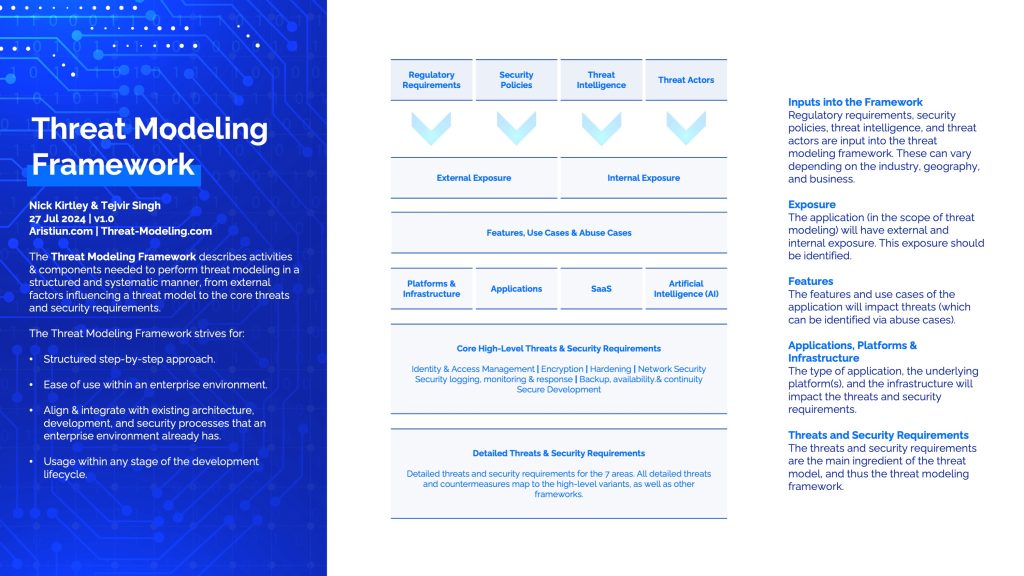
Premium Ai Image Mitigating Risks With Threat Modeling Inspired by these commonalities and guided by the four key questions of threat modeling discussed above, this cheatsheet will break the threat modeling down into four basic steps: application decomposition, threat identification and ranking, mitigations, and review and validation. By following these threats modeling best practices and going through the key stages of scope definition, asset identification, threat identification, vulnerability analysis, and risk prioritization and mitigation, you can significantly enhance your organization’s security defenses. You'll learn how to use leading threat modeling tools, identify and prioritize potential threats, and integrate these practices into the software development life cycle to detect risks. Threat modeling guides the requirements specification and early design choices to make a system robust against attacks and weaknesses. threat modeling can help software developers and cybersecurity professionals know what types of defenses, mitigation strategies, and controls to put in place.

Premium Photo Identifying And Mitigating Threats With Modeling You'll learn how to use leading threat modeling tools, identify and prioritize potential threats, and integrate these practices into the software development life cycle to detect risks. Threat modeling guides the requirements specification and early design choices to make a system robust against attacks and weaknesses. threat modeling can help software developers and cybersecurity professionals know what types of defenses, mitigation strategies, and controls to put in place. Learn how to identify and mitigate security threats with threat modeling. explore stride, pasta, attack trees, and best practices for securing applications. In this article, you’ll learn how to choose the right threat modeling methodology for your context, how to integrate threat modeling into your ci cd pipeline so it becomes a living practice rather than a one time ritual, and how to avoid the pitfalls that cause most threat modeling programs to stall. Threat modeling represents one of the most powerful yet underutilized practices in cybersecurity. as systems become increasingly complex and interconnected, the ability to systematically identify, categorize, and mitigate potential security threats before they materialize becomes essential. These organizations find and fix vulnerabilities before attackers exploit them. this guide covers the threat modeling techniques that nist, cisa, enisa, and other authoritative bodies have validated through extensive real world applications.
Comments are closed.