Effective Api Scanning Techniques For Modern Security
Effective Api Scanning Techniques For Modern Security Explore various api scanning methods and tools to proactively identify vulnerabilities and enhance your application's security posture. With regulations like gdpr and ccpa imposing strict penalties for data breaches, api security becomes a compliance issue. it is essential for organizations to implement robust api security measures to avoid financial penalties, reputational damage, and legal repercussions.

Api Security Scanning Download the wiz api security best practices cheat sheet and fortify your api infrastructure with proven, advanced techniques tailored for secure, high performance api management. Discover the top 10 api security scanning tools to protect your apis from vulnerabilities. learn how apidog, owasp zap, burp suite, and others can enhance your api security. Learn everything about api security in 2025 key risks, standards, tools, and strategies to secure your apis against modern threats. Popular api security testing methods include vulnerability scanning, fuzz testing, penetration testing, static application security testing (sast), and dynamic application security testing (dast). organizations use apis to connect services and transfer data internally and externally.
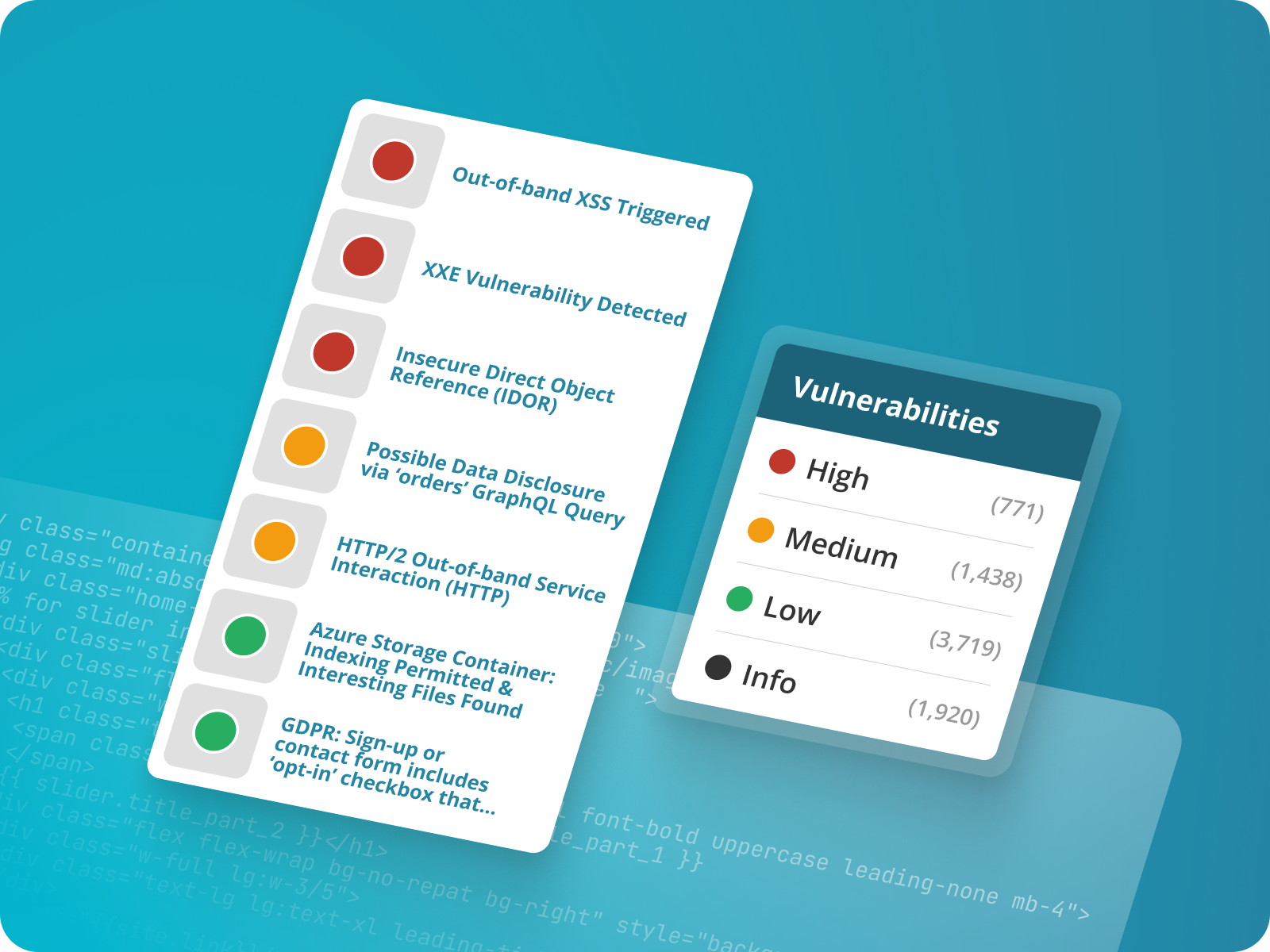
Api Security Scanning Learn everything about api security in 2025 key risks, standards, tools, and strategies to secure your apis against modern threats. Popular api security testing methods include vulnerability scanning, fuzz testing, penetration testing, static application security testing (sast), and dynamic application security testing (dast). organizations use apis to connect services and transfer data internally and externally. Follow these top api security best practices to safeguard your apis from modern threats. learn about encryption, validation, logging, scanning, and more. Discover essential api security testing tools, methodologies, and best practices to protect your apis from breaches and threats for 2025. Step by step api security testing methodology covering owasp api top 10, rest graphql grpc testing techniques, burp suite workflows, and common pitfalls. for developers and pentesters. This guide provides a comprehensive api security checklist covering discovery and classification, core security controls, data protection, endpoint hardening, and continuous testing methodologies that modern application teams need to defend against evolving threats in cloud native environments.
Comments are closed.