Echo Escape 1 Basic Buffer Overflow Tutorial Ret2win Picoctf 2026
Picoctf 2022 Buffer Overflow 1 In this picoctf 2026 writeup for echo escape 1, we walk through a fundamental 64 bit buffer overflow (ret2win) exploit. This challenge is a classic format string vulnerability exploitation, following the same pattern as picoctf's "echo valley" challenge from 2025. the program has an echo service that reads user input and prints it back using a vulnerable printf(buf) call instead of the safe printf("%s", buf).
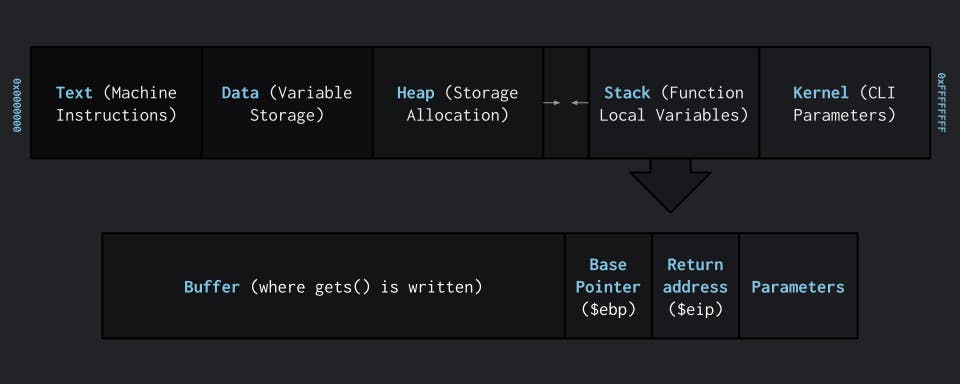
Picoctf 2022 Buffer Overflow 1 Posts buffer overflow and binary exploitation for ctf april 4, 2026 buffer overflow and binary exploitation for ctf a practical guide to binary exploitation techniques in ctf competitions: stack buffer overflows, ret2win, format string attacks, heap exploitation, and aslr pie bypass with picoctf challenge links for each technique. Learn the fundamentals of buffer overflow attacks with a simple ret2win challenge. master stack layout, overflow calculations, and return address hijacking. The echo service uses printf (buf) allowing us to leak addresses and overwrite the return address to redirect execution to print flag (). based on the picoctf "echo valley" pattern from 2025. The python script sends a carefully crafted message that, when processed by the vulnerable function, overflows the buffer and overwrites the return address on the stack with the address of win.
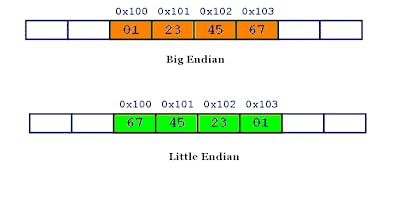
Picoctf 2022 Buffer Overflow Series Enscribe Dev The echo service uses printf (buf) allowing us to leak addresses and overwrite the return address to redirect execution to print flag (). based on the picoctf "echo valley" pattern from 2025. The python script sends a carefully crafted message that, when processed by the vulnerable function, overflows the buffer and overwrites the return address on the stack with the address of win. Ringkasan: program menerima input tanpa batas (gets), buffer lokal terlalu kecil → kita overflow saved eip dan menulis alamat fungsi win() sebagai return address. This post is intended to serve as notes, as well as a basic introduction to newbies. this is the first challenge from ropemporium. it focuses on one of the more simple stack based overflow attacks. Let's start off simple, can you overflow the correct buffer? the program is available here. you can view source here. connect using: nc saturn.picoctf 60079. the program simply asks for an input: please create 'flag.txt' in this directory with your own debugging flag. So, our payload completely overflowed the eip. there will be some function specific padding used that's why the numbers didn't add up. now we need to get the address of the win function.
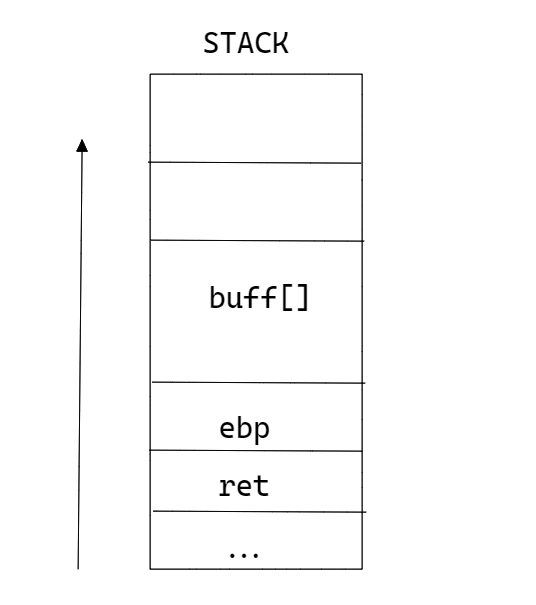
Picoctf 2022 Buffer Overflow 1 Yariss Ringkasan: program menerima input tanpa batas (gets), buffer lokal terlalu kecil → kita overflow saved eip dan menulis alamat fungsi win() sebagai return address. This post is intended to serve as notes, as well as a basic introduction to newbies. this is the first challenge from ropemporium. it focuses on one of the more simple stack based overflow attacks. Let's start off simple, can you overflow the correct buffer? the program is available here. you can view source here. connect using: nc saturn.picoctf 60079. the program simply asks for an input: please create 'flag.txt' in this directory with your own debugging flag. So, our payload completely overflowed the eip. there will be some function specific padding used that's why the numbers didn't add up. now we need to get the address of the win function.
Comments are closed.