E1590600e3be9980c931de8f51fbfe164266499d Png

File 16 Png Wiki Join our upcoming webinar on november 6th at 17:00 pm cest and 11:00 am edt where we'll show you how to transform raw intelligence into a dynamic, actionable defense strategy. we’ll start with a real world scenario from google threat intelligence. Verdict whether the website was considered malicious at the time of the scan, based on malicious content detection. no classification means there was not enough signal to determine a verdict. understand the security, performance, technology, and network details of a url with a publicly shareable report.

File Pix0004 Png Myriad Uncover it is a malware configuration extractor that can analyze files statically. Convert and preview data uri images instantly. paste encoded strings or drag and drop images to generate data uris. perfect for developers working with base64 encoded images, featuring live preview and format cleanup. Enter a file's sha256 to search talos' current file reputation system. the disposition search will return a file's reputation, file name, weighted reputation score (if available), and detection information, in addition to alternate detection names used by other vendors. Meet url decode and encode, a simple online tool that does exactly what it says: decodes from url encoding as well as encodes into it quickly and easily. url encode your data without hassles or decode it into a human readable format.
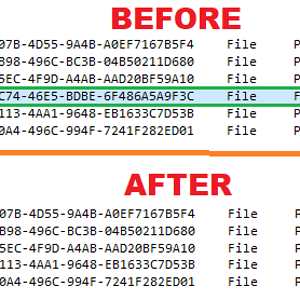
0cf2d3adace5a41f323a2630812a247a4c051efc Png Pkbiosfix Enter a file's sha256 to search talos' current file reputation system. the disposition search will return a file's reputation, file name, weighted reputation score (if available), and detection information, in addition to alternate detection names used by other vendors. Meet url decode and encode, a simple online tool that does exactly what it says: decodes from url encoding as well as encodes into it quickly and easily. url encode your data without hassles or decode it into a human readable format. Github cryakl ransomware database: for educational purposes only, samples of ransomware wiper trojans including screenshots ransom notes. Go to parent directory. Simply enter the mac address or oui, and you’ll instantly see the vendor’s name, address, and country. in addition, we provide historical data on mac prefixes, so you can track any changes to vendor names or addresses over time. File locker is a ransomware type virus based on hidden tear. immediately after infiltration, file locker encrypts most stored data using the aes encryption algorithm and appends filenames with the ".locked " extension (e.g., " sample " is renamed to " sample .locked "). from this point, compromised data becomes unusable.
E1f0fdfa8f41055982e60f29b936ca96 Youtube Github cryakl ransomware database: for educational purposes only, samples of ransomware wiper trojans including screenshots ransom notes. Go to parent directory. Simply enter the mac address or oui, and you’ll instantly see the vendor’s name, address, and country. in addition, we provide historical data on mac prefixes, so you can track any changes to vendor names or addresses over time. File locker is a ransomware type virus based on hidden tear. immediately after infiltration, file locker encrypts most stored data using the aes encryption algorithm and appends filenames with the ".locked " extension (e.g., " sample " is renamed to " sample .locked "). from this point, compromised data becomes unusable.
Comments are closed.