Dynamic Malware Assessment Flow Chart Infographics Pdf

Dynamic Malware Analysis Using Cuckoo Sandbox Download Free Pdf Showcasing this set of slides titled dynamic malware assessment flow chart infographics pdf. the topics addressed in these templates are live operating system, volatile memory forensics, slide channel analysis. all the content presented in this ppt design is completely editable. It describes how dynamic analysis is used when static analysis reaches limitations. it outlines risks of dynamic analysis and how sandboxes can be used to safely analyze malware.

Dynamic Malware Assessment Flow Chart Infographics Pdf It is a graphical representation of the execution flow of a program, which can be used to identify abnormal patterns and malicious behavior in the program. in cybersecurity, cfg analysis has become a critical static analysis technique for malware detection. Malicious software or malware continues to pose a major security concern in this digital age as computer users, corporations, and governments witness an exponential growth in malware attacks. Why analyze malware? •to assess damage •to discover indicators of compromise •to determine sophistication level of an intruder •to identify a vulnerability •to catch the “bad guy”® •to answer questions…. This slide illustrates malware analysis flowchart which companies employ to learn from past attack and create more secure infrastructure for future. the elements covered in this slide are live operating system, volatile memory forensics and slide channel analysis.
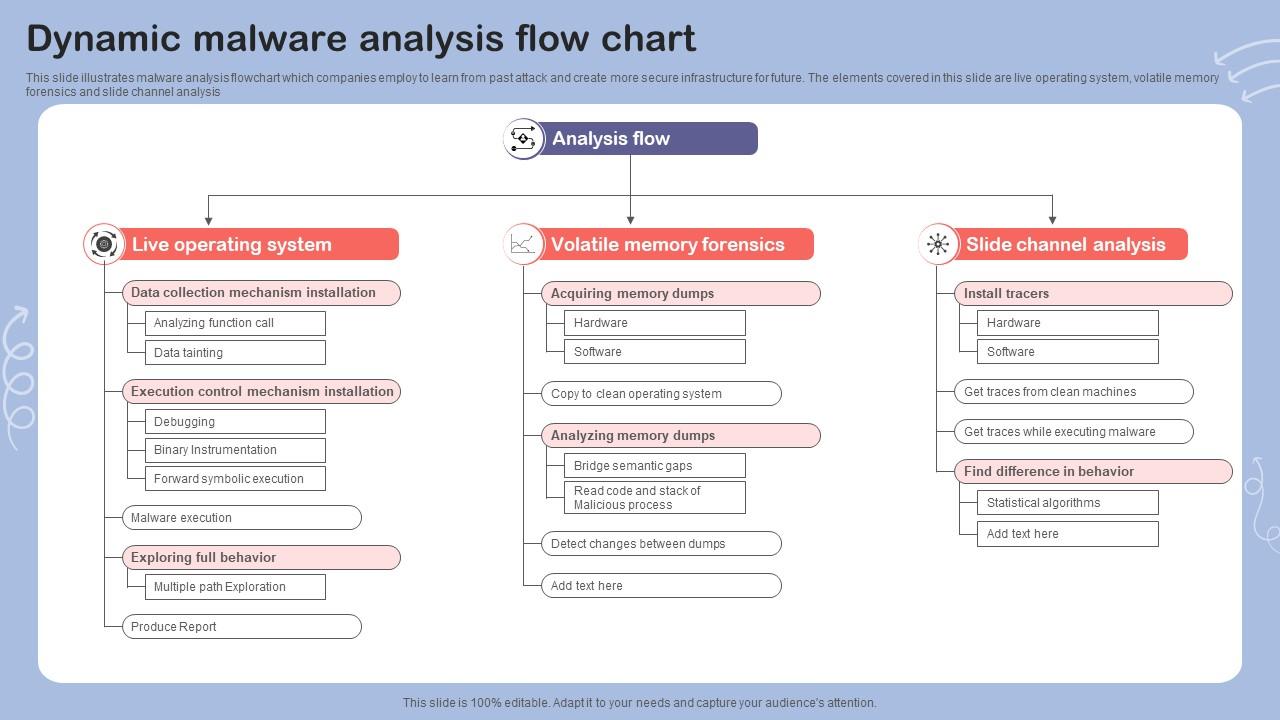
Dynamic Malware Analysis Flow Chart Ppt Sample Why analyze malware? •to assess damage •to discover indicators of compromise •to determine sophistication level of an intruder •to identify a vulnerability •to catch the “bad guy”® •to answer questions…. This slide illustrates malware analysis flowchart which companies employ to learn from past attack and create more secure infrastructure for future. the elements covered in this slide are live operating system, volatile memory forensics and slide channel analysis. Based on the generic data flow model, windows system entities and the mapping of windows api calls to events, we can now present specific malware detection heuristics that make use of (quantitative) data flows and data flow prop erties. It provides step by step guidance in all workflow phases on how to develop malware analysis capabilities within csirts. this document also lists supporting resources that can further assist in understanding how malware analysis procedures can be carried out efficiently. This article explores dynamic malware analysis, its key techniques, sandboxing methods, memory forensics, threat intelligence generation, and tools that security professionals use to counteract malware threats and strengthen cybersecurity defenses. This document provides an overview of basic dynamic malware analysis techniques. it explains that dynamic analysis examines how malware behaves when executed by monitoring changes to the system, unusual processes, network traffic, and other behaviors.
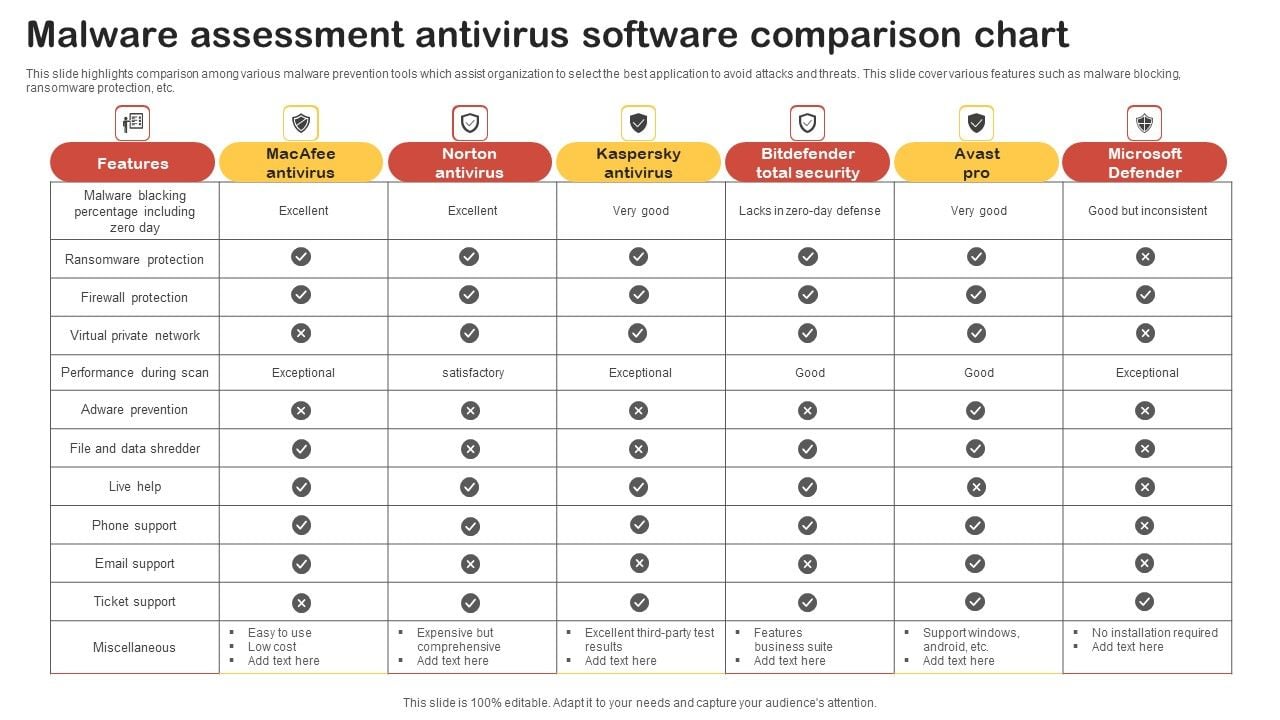
Malware Assessment Antivirus Software Comparison Chart Template Pdf Based on the generic data flow model, windows system entities and the mapping of windows api calls to events, we can now present specific malware detection heuristics that make use of (quantitative) data flows and data flow prop erties. It provides step by step guidance in all workflow phases on how to develop malware analysis capabilities within csirts. this document also lists supporting resources that can further assist in understanding how malware analysis procedures can be carried out efficiently. This article explores dynamic malware analysis, its key techniques, sandboxing methods, memory forensics, threat intelligence generation, and tools that security professionals use to counteract malware threats and strengthen cybersecurity defenses. This document provides an overview of basic dynamic malware analysis techniques. it explains that dynamic analysis examines how malware behaves when executed by monitoring changes to the system, unusual processes, network traffic, and other behaviors.
Comments are closed.