Dynamic Malware Analysis Tools Workflow Amadey Malware
Amadey Malware Analysis Amr Ashraf 🚀 build real confidence analyzing malware. Amadey is a modular windows malware sold as malware as a service since 2018 that functions as both a botnet client and a flexible loader, allowing low skill operators to deploy stealers, cryptominers, and rats via phishing, malvertising, and trojanized installers.
Amadey Malware Analysis Amr Ashraf In this walkthrough, i’ll be covering a cyberdefenders lab focused on endpoint forensics. an after hours edr alert flagged suspicious activity on a windows workstation, revealing signs of the. In any.run, users can safely detonate amadey samples and analyze it dynamically in a fully interactive cloud sandbox. our service automatically collects and displays the execution data in user friendly formats, such as this process graph. This blog enables security analysts, blue teamers and splunk customers to identify amadey trojan stealer malware by helping the community discover amadey tactics, techniques and procedures that are being used by several threat actors and adversaries. Amadey is a botnet that appeared around october 2018 and is being sold for about $500 on russian speaking hacking forums. it periodically sends information about the system and installed av software to its c2 server and polls to receive orders from it.
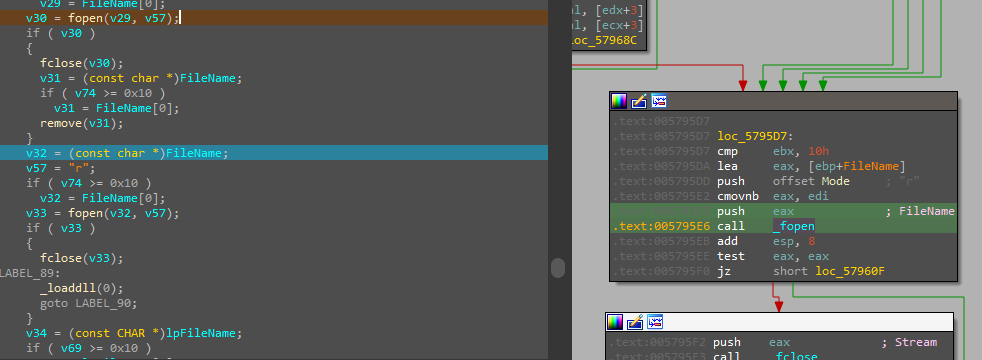
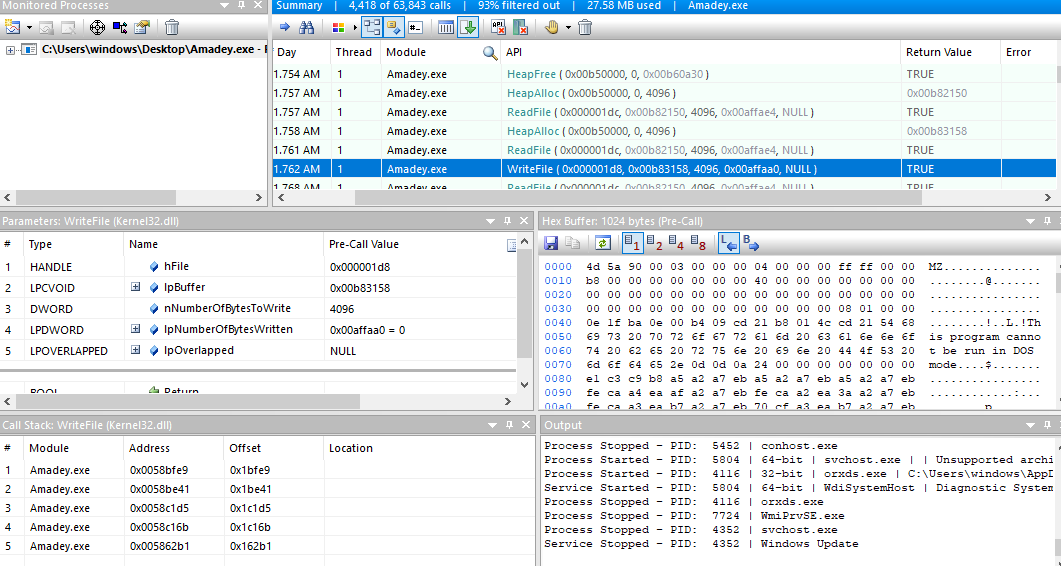
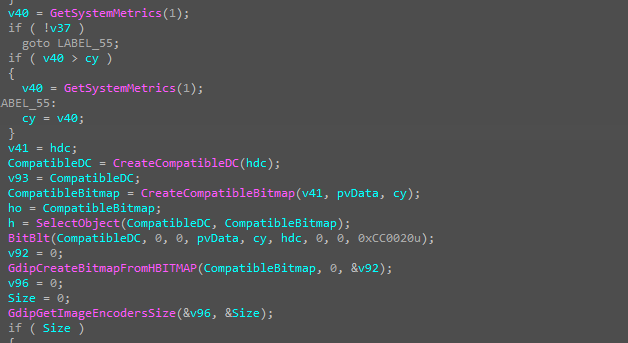
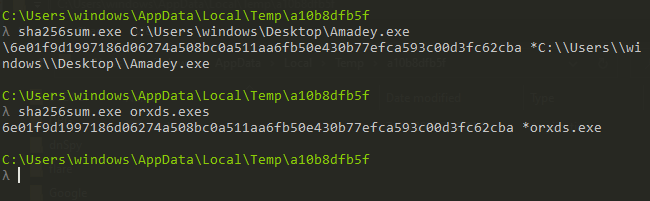
Amadey Malware Analysis Amr Ashraf This blog enables security analysts, blue teamers and splunk customers to identify amadey trojan stealer malware by helping the community discover amadey tactics, techniques and procedures that are being used by several threat actors and adversaries. Amadey is a botnet that appeared around october 2018 and is being sold for about $500 on russian speaking hacking forums. it periodically sends information about the system and installed av software to its c2 server and polls to receive orders from it. Starting with the api monitor tool which has a lot of features in tracing api calls and execution, i will run the sample and just take a look at the system state related to the malware. I have recently been doing cyber defenders labs in their blue yard cyber range to get more reps in from a dfir perspective. this week we are going to create a walkthrough for the amadey malware endpoint forensics lab. What actually happens when malware runs? that’s the question i answer in my latest video, where i analyze an amadey (information stealer) malware sample using dynamic analysis tools. The flagged malware align with the amadey trojan stealer. your job is to analyze the presented memory dump and create a detailed report for actions taken by the malware.
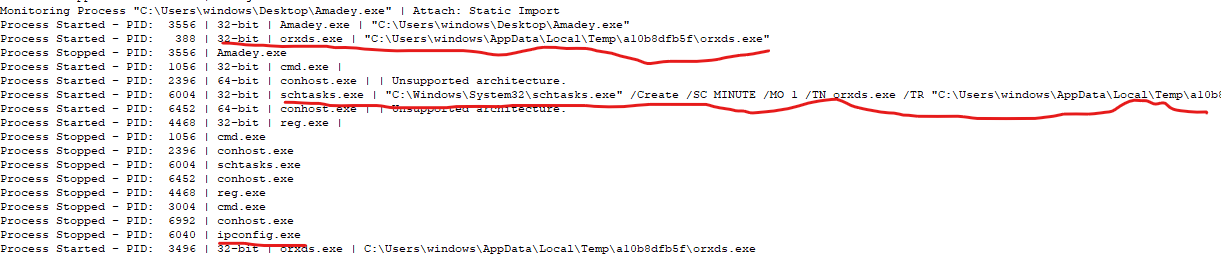
Amadey Malware Analysis Amr Ashraf Starting with the api monitor tool which has a lot of features in tracing api calls and execution, i will run the sample and just take a look at the system state related to the malware. I have recently been doing cyber defenders labs in their blue yard cyber range to get more reps in from a dfir perspective. this week we are going to create a walkthrough for the amadey malware endpoint forensics lab. What actually happens when malware runs? that’s the question i answer in my latest video, where i analyze an amadey (information stealer) malware sample using dynamic analysis tools. The flagged malware align with the amadey trojan stealer. your job is to analyze the presented memory dump and create a detailed report for actions taken by the malware.
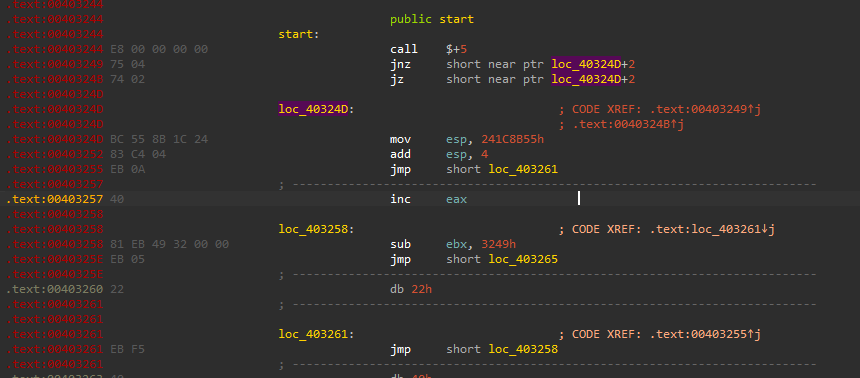
Amadey Malware Analysis Amr Ashraf What actually happens when malware runs? that’s the question i answer in my latest video, where i analyze an amadey (information stealer) malware sample using dynamic analysis tools. The flagged malware align with the amadey trojan stealer. your job is to analyze the presented memory dump and create a detailed report for actions taken by the malware.
Amadey Malware Analysis Amr Ashraf
Comments are closed.