Dylan Talk Buffer Overflow Bugs
Ivanti Patches Two Critical Buffer Overflow Bugs In Avalanche Emm Pa If the program fails to write backspace characters back to the pipe, it will reset the buffer size, but the pointer used to write to the buffer will not be reset properly. to get a more detailed understanding of this, let’s look at the commit that fixed this bug. How to debug buffer overflows. you’ll learn how to use tools like gdb, lldb, and memory maps to find memory corruption. how to prevent buffer overflows. we’ll cover some best practices like input validation, safe memory handling, and defensive programming.
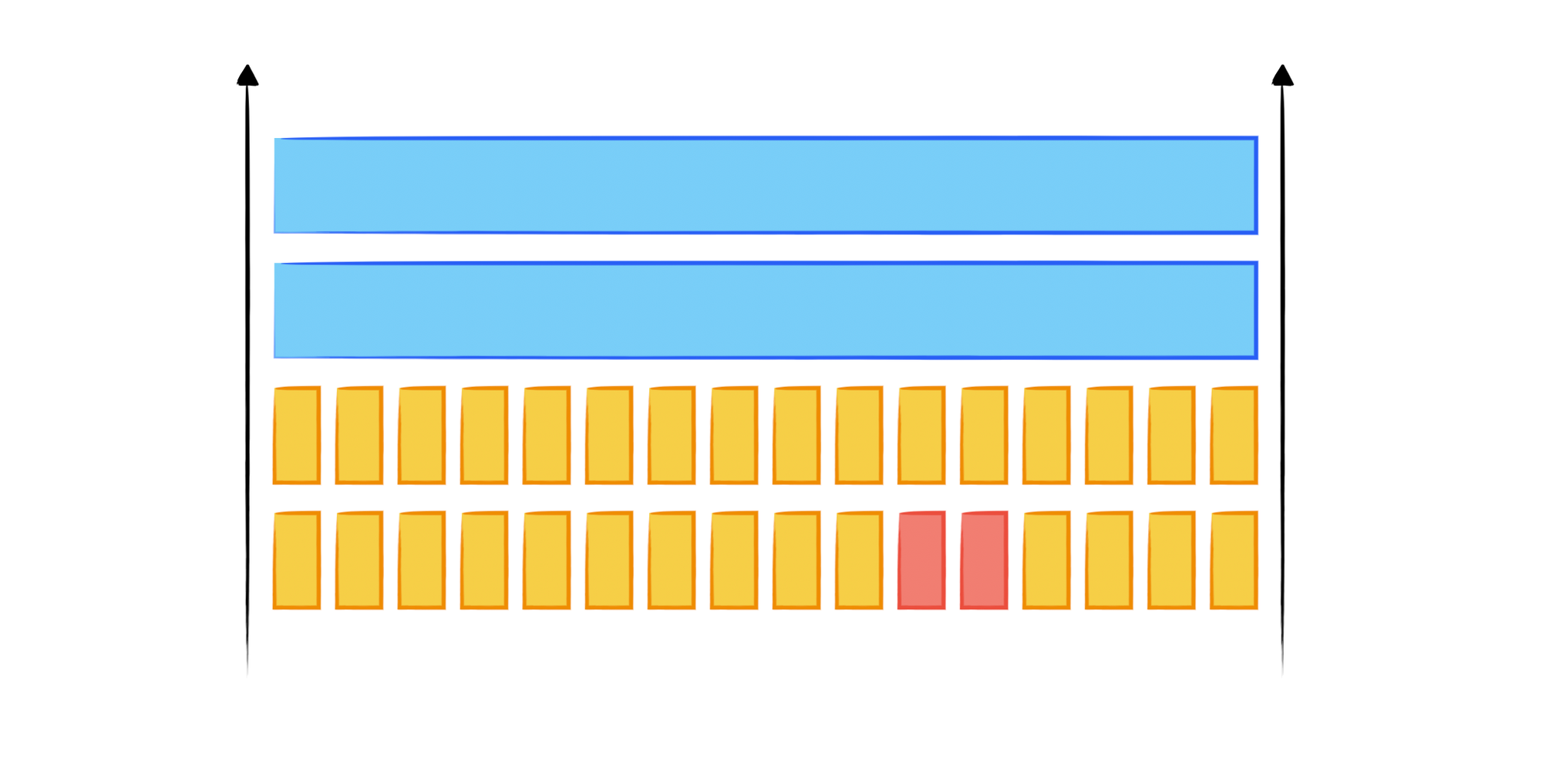
Buffer Overflow Attack From The Ground Up Iii Canary When a buffer is loaded with more data than it is able to hold, buffer overrun takes place. lack of appropriate verification results in a critical vulnerability or bug that lets data be. Learn how to detect, prevent, and fix buffer overflows, one of the most dangerous vulnerabilities in c c software security. read all about here!. Learn how to detect, prevent, and mitigate buffer overflow attacks. get best practices and tips for handling buffer overflow risks in your security program. A buffer is a temporary area for data storage. when more data (than was originally allocated to be stored) gets placed by a program or system process, the extra data overflows. it causes some of that data to leak out into other buffers, which can corrupt or overwrite whatever data they were holding.
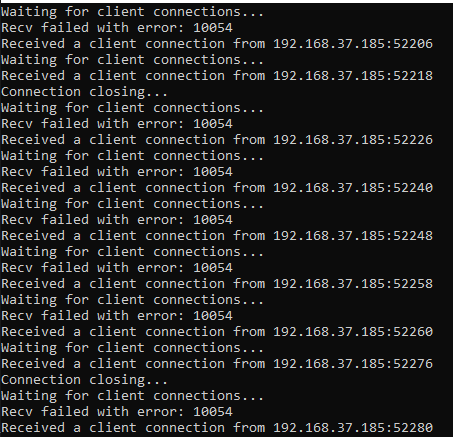
Buffer Overflow Steps Spiking Fuzzing Learn how to detect, prevent, and mitigate buffer overflow attacks. get best practices and tips for handling buffer overflow risks in your security program. A buffer is a temporary area for data storage. when more data (than was originally allocated to be stored) gets placed by a program or system process, the extra data overflows. it causes some of that data to leak out into other buffers, which can corrupt or overwrite whatever data they were holding. In this comprehensive guide, we will dig into exactly how buffer overflows occur, how attackers leverage them to catastrophically hijack systems, and the battle tested techniques to lock these bugs down for good. Buffer overflow is a software coding error that enables hackers to exploit vulnerabilities, steal data, and gain unauthorized access to corporate systems. discover what is a buffer overflow attack and how fortinet can mitigate and prevent overflow attacks. Forallsecure threat research (fastr): discovering a buffer overflow in glibc 5 312 followers 8 posts. Buffer overflow is probably the best known form of software security vulnerability. most software developers know what a buffer overflow vulnerability is, but buffer overflow attacks against both legacy and newly developed applications are still quite common.

Buffer Overflow An In Depth Survey Of Bypassing Buffer Overflow In this comprehensive guide, we will dig into exactly how buffer overflows occur, how attackers leverage them to catastrophically hijack systems, and the battle tested techniques to lock these bugs down for good. Buffer overflow is a software coding error that enables hackers to exploit vulnerabilities, steal data, and gain unauthorized access to corporate systems. discover what is a buffer overflow attack and how fortinet can mitigate and prevent overflow attacks. Forallsecure threat research (fastr): discovering a buffer overflow in glibc 5 312 followers 8 posts. Buffer overflow is probably the best known form of software security vulnerability. most software developers know what a buffer overflow vulnerability is, but buffer overflow attacks against both legacy and newly developed applications are still quite common.

Buffer Overflow An In Depth Survey Of Bypassing Buffer Overflow Forallsecure threat research (fastr): discovering a buffer overflow in glibc 5 312 followers 8 posts. Buffer overflow is probably the best known form of software security vulnerability. most software developers know what a buffer overflow vulnerability is, but buffer overflow attacks against both legacy and newly developed applications are still quite common.
Comments are closed.