Dps Final Pdf Internet Protocols Public Key Cryptography

Unit 3 Public Key Cryptography Pdf Public Key Cryptography It includes short answer questions and practical problems, such as rsa encryption and hash functions, with detailed solutions provided. the exam assesses understanding of key concepts and practical applications in cryptography. Reduce protection of information to protection of authenticity of public keys • no need to keep public keys secret, but must be sure that alice’s public key is really her true public key.

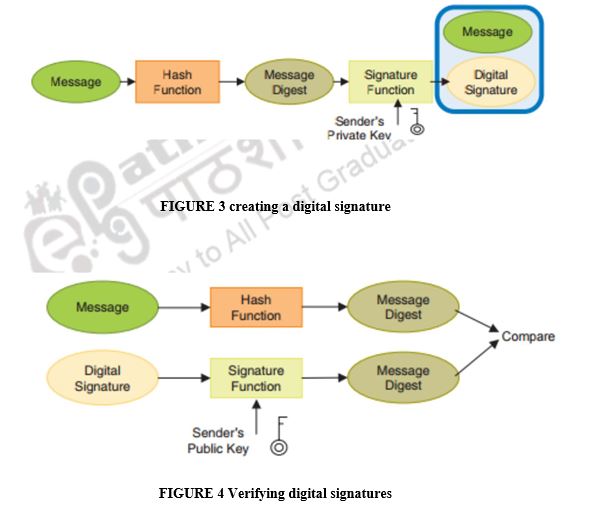
Pdf Protocols For Public Key Cryptography Digital signatures are based on public key techniques. signature generation ≡ decryption (uses private key), and signature verification ≡ encryption (uses public key). This chapter presents the key algorithms and protocols used in cryptography. However, public key encryption has proved indispensable for key management, for distributing the keys needed for the more traditional symmetric key encryption decryption of the content, for digital signature applications, etc. Elgamal encryption transforms diffie hellman key agreement into a public key encryption scheme by using the public secret information of the recipient as a long term key pair and the public secret information of the sender as a one time key pair.
Public Key Cryptography Cryptography And Network However, public key encryption has proved indispensable for key management, for distributing the keys needed for the more traditional symmetric key encryption decryption of the content, for digital signature applications, etc. Elgamal encryption transforms diffie hellman key agreement into a public key encryption scheme by using the public secret information of the recipient as a long term key pair and the public secret information of the sender as a one time key pair. The established key can then be used to encrypt subsequent communication using a symmetric key cipher “new directions in cryptography” by whitfield diffie and martin hellman, 1976. Each receiver possesses a unique decryption key, generally referred to as his private key. receiver needs to publish an encryption key, referred to as his public key. some assurance of the authenticity of a public key is needed in this scheme to avoid spoofing by adversary as the receiver. Public key cryptography is a method of secure communication that uses a pair of keys, a public key, which anyone can use to encrypt messages or verify signatures, and a private key, which is kept secret and used to decrypt messages or sign documents. Public key cryptography pkc solves the classical “key distribution problem”: – if there is no secure channel, how can a & b share the key securely?.
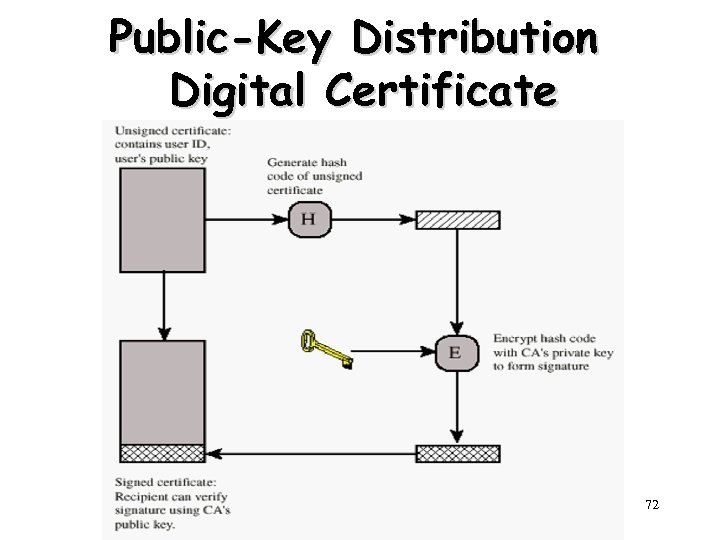
Chapter 3 Public Key Cryptography And Message Authentication 1 The established key can then be used to encrypt subsequent communication using a symmetric key cipher “new directions in cryptography” by whitfield diffie and martin hellman, 1976. Each receiver possesses a unique decryption key, generally referred to as his private key. receiver needs to publish an encryption key, referred to as his public key. some assurance of the authenticity of a public key is needed in this scheme to avoid spoofing by adversary as the receiver. Public key cryptography is a method of secure communication that uses a pair of keys, a public key, which anyone can use to encrypt messages or verify signatures, and a private key, which is kept secret and used to decrypt messages or sign documents. Public key cryptography pkc solves the classical “key distribution problem”: – if there is no secure channel, how can a & b share the key securely?.
Comments are closed.