Dockerfile Secrets

Dockerfile Secrets To consume a secret in a build and make it accessible to the run instruction, use the mount=type=secret flag in the dockerfile. Assuming the latest docker with buildkit enabled, the documentation suggests that the secret option has file and env types. i want to use the env type like this:.
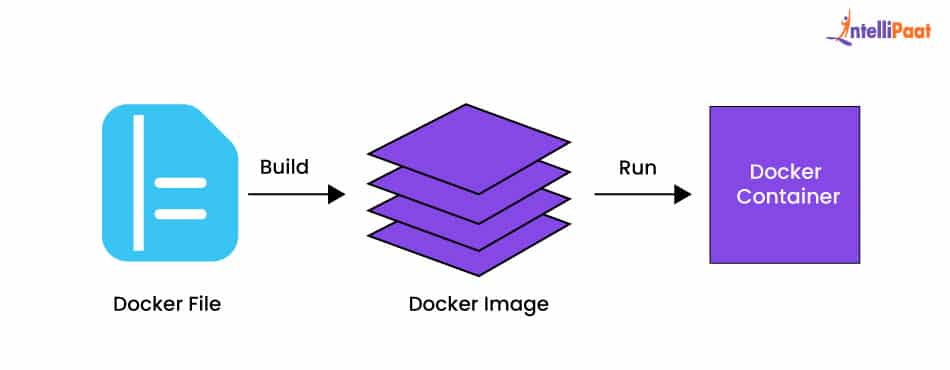
Dockerfile Explained With Example Complete Guide Manage secrets via environment variables and mounts in docker with current best practices for software developers including multi stage builds. But most importantly is to remember to never hard code your docker secrets in plaintext in your dockerfile! following these guidelines ensures that your organization's sensitive information remains safe even when running containerized services. Docker secrets are a secure way to pass sensitive data from files or from the environment into the build process or the running container. this avoids accidentally exposing credentials to the viewer, or copy and paste sensitive information. Instead, we need a secure way to inject secrets into the build process without exposing them. this blog explores how to use docker’s `build arg` to consume environment variables sourced from kubernetes secrets during image builds.
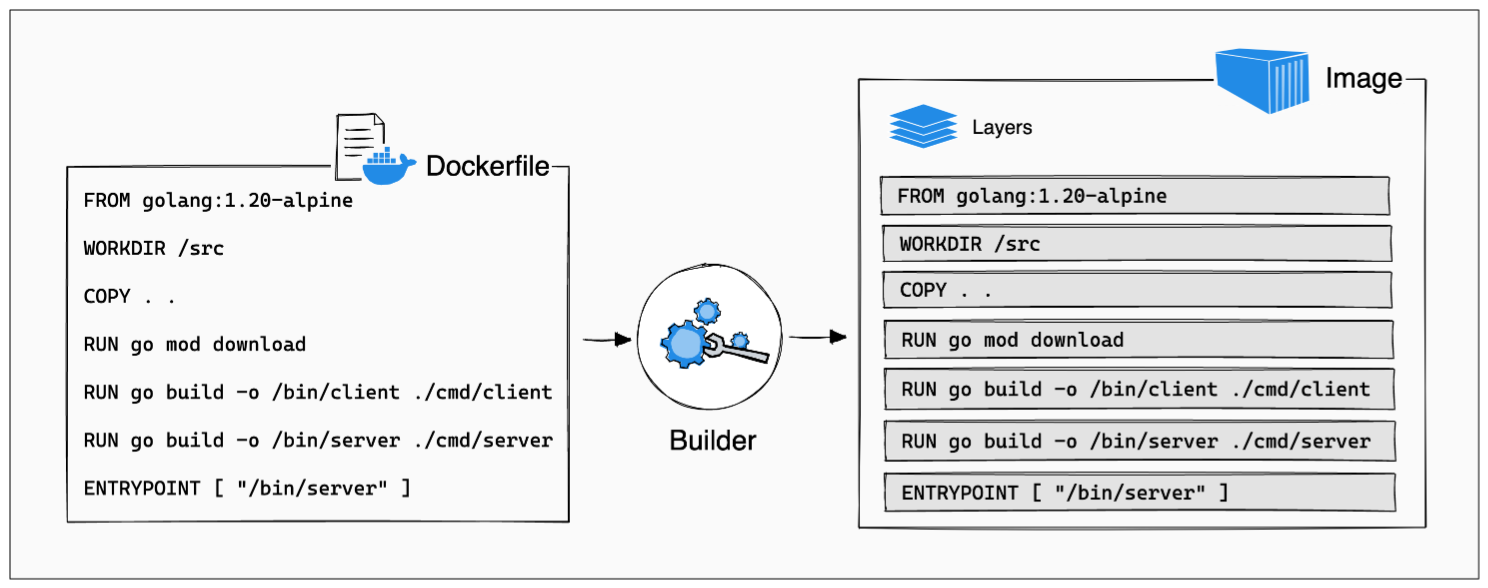
Dockerfile Docker secrets are a secure way to pass sensitive data from files or from the environment into the build process or the running container. this avoids accidentally exposing credentials to the viewer, or copy and paste sensitive information. Instead, we need a secure way to inject secrets into the build process without exposing them. this blog explores how to use docker’s `build arg` to consume environment variables sourced from kubernetes secrets during image builds. Learn how to pass a secret to a docker build from an environment variable to maintain your application's security. Learn how docker secrets work, why they're more secure than environment variables, and best practices for managing secrets across swarm, compose, and ci cd pipelines. In terms of docker swarm services, a secret is a blob of data, such as a password, ssh private key, ssl certificate, or another piece of data that should not be transmitted over a network or stored unencrypted in a dockerfile or in your application's source code. Managing secrets such as api keys, passwords, and certificates in docker is critical for secure applications. hardcoding secrets in images or environment variables can expose sensitive data. this guide explores best practices for handling secrets in docker with practical examples.
Comments are closed.