Dockerexploit Docker Remote Api Scanner And Exploit

Docker Vulnerabilities And Security Risks Soos Docker api pentesting techniques for identifying, exploiting docker services, enumeration, attack vectors and post exploitation insights. We will conduct a detailed analysis of the attack flow, describing how attackers exploit vulnerable docker remote api servers. by looking over recent incidents, we will emphasize the importance of securing the docker remote api server and the potential consequences of this exploitation.

Exploitation Of Docker Remote Api Servers Has Reached A Critical Level Recent incidents highlight the severity of exploiting docker remote api servers. in one notable case, an unidentified threat actor deployed a cryptocurrency miner using the described method. In june 2025, trend micro’s threat intelligence team reported malware exploiting unsecured docker apis on port 2375 to spin up an alpine container, bind mount the host filesystem, and execute a base64 encoded downloader via tor. This repository contains a docker remote api scanner and exploit tool designed for educational and research purposes. it enables users to perform security assessments and experiments related to docker container environments. This repository contains a docker remote api scanner and exploit tool designed for educational and research purposes. it enables users to perform security assessments and experiments related to docker container environments.
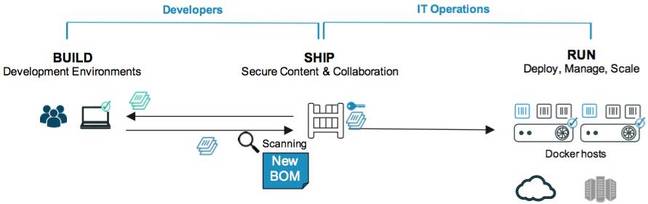
Docker Lets Security Bug Sniffer Dogs Off The Leash At Container Images This repository contains a docker remote api scanner and exploit tool designed for educational and research purposes. it enables users to perform security assessments and experiments related to docker container environments. This repository contains a docker remote api scanner and exploit tool designed for educational and research purposes. it enables users to perform security assessments and experiments related to docker container environments. Docker remote api scanner and exploit this repository contains a docker remote api scanner and exploit tool designed for educational and research purposes. it enables users to perform security assessments and experiments related to. A newly discovered cyberattack combines two powerful tools — docker remote api and the tor anonymity network — to silently infiltrate containerized environments and mine cryptocurrency. Docker remote api scanner and exploit. contribute to justakazh dockerexploit development by creating an account on github. This repository contains a docker remote api scanner and exploit tool designed for educational and research purposes. it enables users to perform security assessments and experiments related to docker container environments.

Cybercriminals Exploiting Docker Api Servers For Srbminer Crypto Mining Docker remote api scanner and exploit this repository contains a docker remote api scanner and exploit tool designed for educational and research purposes. it enables users to perform security assessments and experiments related to. A newly discovered cyberattack combines two powerful tools — docker remote api and the tor anonymity network — to silently infiltrate containerized environments and mine cryptocurrency. Docker remote api scanner and exploit. contribute to justakazh dockerexploit development by creating an account on github. This repository contains a docker remote api scanner and exploit tool designed for educational and research purposes. it enables users to perform security assessments and experiments related to docker container environments.

Scan Reports Many Vulnerabilities In Official Images On Docker Hub Docker remote api scanner and exploit. contribute to justakazh dockerexploit development by creating an account on github. This repository contains a docker remote api scanner and exploit tool designed for educational and research purposes. it enables users to perform security assessments and experiments related to docker container environments.
Comments are closed.