Do This Now To Secure Your Google Authenticator

Google Authenticator Now Backs Up Otps So You Re Not Sol When Your 2fa Browse the different types of passwordless authentication tools we offer that are designed to help you sign in quickly and securely across devices. You can save your codes safely in your google account with google authenticator. this helps protect you from being locked out of your account when you change devices.
How To Use Google Authenticator With A Pc Whether you’re securing your email, social media, or cloud storage, google authenticator adds an essential extra layer of protection. setting up and using google authenticator is surprisingly easy, and it’s compatible with a wide range of services like google, facebook, dropbox, and more. A complete guide on how to use google authenticator on smartphones and pcs to improve account security through two step authentication. Learn how to back up your google authenticator codes so you don't find yourself in a situation where you lose your phone and thereby lose access to all your accounts. If you can still access your old authenticator (or have printed or screen captured your qr code), recovering your accounts is simple. this wikihow article will show you how to restore google authenticator onto a new phone or tablet.

How Secure Is Google Authenticator Robots Net Learn how to back up your google authenticator codes so you don't find yourself in a situation where you lose your phone and thereby lose access to all your accounts. If you can still access your old authenticator (or have printed or screen captured your qr code), recovering your accounts is simple. this wikihow article will show you how to restore google authenticator onto a new phone or tablet. We are excited to announce an update to google authenticator, across both ios and android, which adds the ability to safely backup your one time codes (also known as one time passwords or otps) to your google account. An update to google authenticator this week finally enabled backups for your two factor authentication codes. but the feature comes with a security risk. In this article, we'll explore what 2fa is and how you can leverage google authenticator, a popular and free authenticator app, to bolster the security of your online accounts. By understanding the strengths and weaknesses of google authenticator, and by following the recommended best practices, users can significantly enhance the security of their online accounts.

How Secure Is Google Authenticator Robots Net We are excited to announce an update to google authenticator, across both ios and android, which adds the ability to safely backup your one time codes (also known as one time passwords or otps) to your google account. An update to google authenticator this week finally enabled backups for your two factor authentication codes. but the feature comes with a security risk. In this article, we'll explore what 2fa is and how you can leverage google authenticator, a popular and free authenticator app, to bolster the security of your online accounts. By understanding the strengths and weaknesses of google authenticator, and by following the recommended best practices, users can significantly enhance the security of their online accounts.
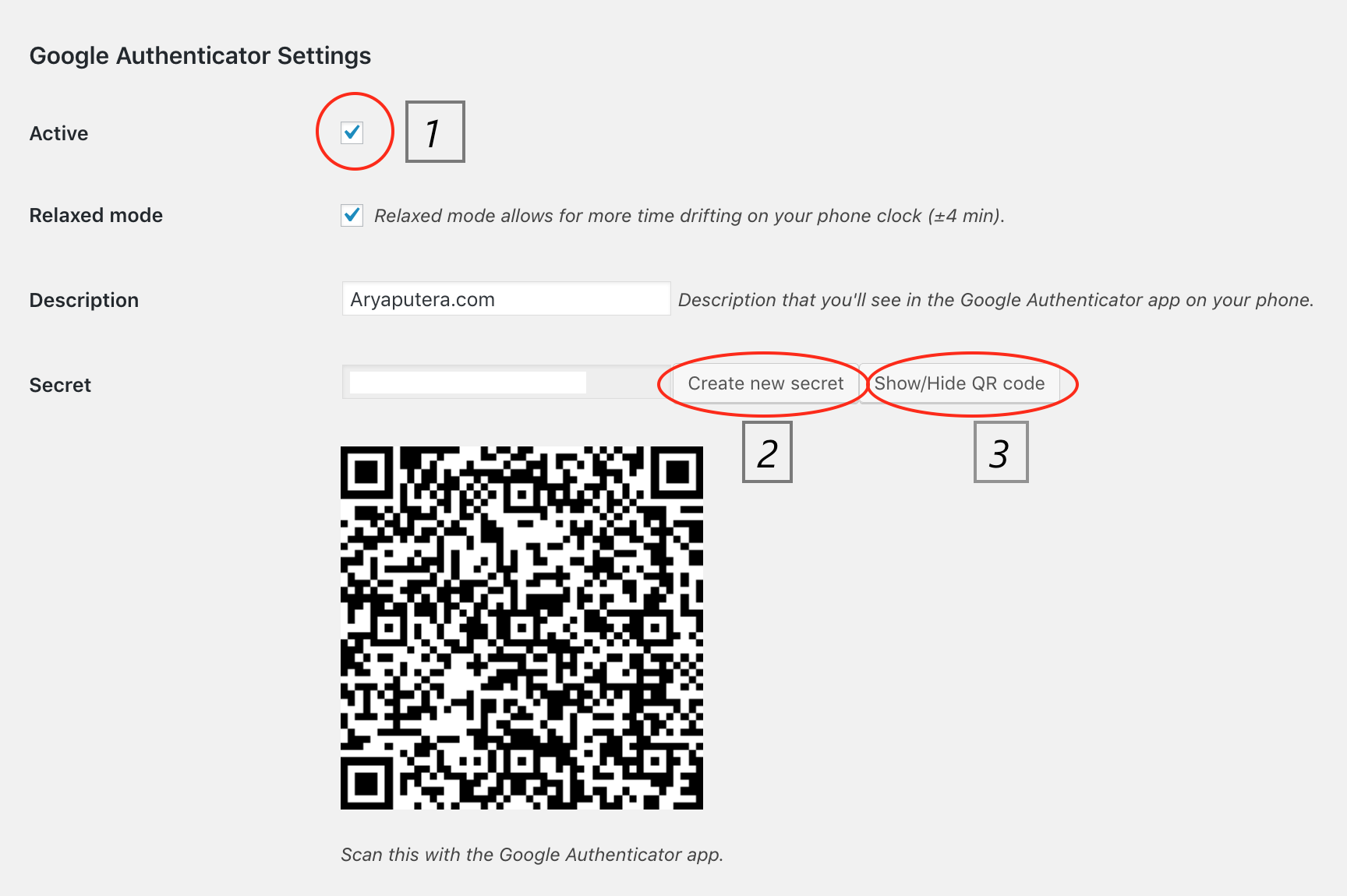
Setup Google Authenticator In this article, we'll explore what 2fa is and how you can leverage google authenticator, a popular and free authenticator app, to bolster the security of your online accounts. By understanding the strengths and weaknesses of google authenticator, and by following the recommended best practices, users can significantly enhance the security of their online accounts.
Comments are closed.