Dit Fft Example Decimation In Time Fast Fourier Transform

Solution Decimation In Time Fast Fourier Transform Dit Fft Studypool The document discusses decimation in time (dit) and decimation in frequency (dif) fast fourier transform (fft) algorithms. dit breaks down an n point sequence into smaller dfts of even and odd indexed samples, recursively computing smaller and smaller dfts until individual points remain. The document describes decimation in time (dit) and decimation in frequency (dif) fast fourier transform (fft) algorithms. it shows flow graphs for an 8 point dit fft that breaks the transform down into successively smaller 4 point dfts, as well as an 8 point dif fft flow graph and 8 point inverse dit fft flow graph.
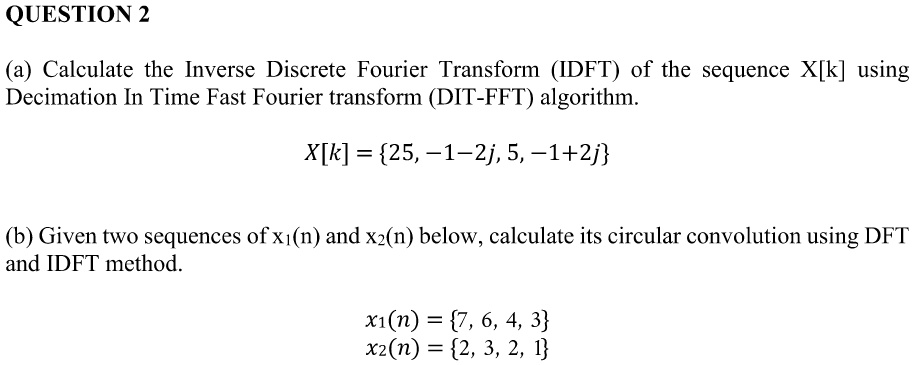
Solved Question 2 A Calculate The Inverse Discrete Fourier Transform In this video, we break down the fast fourier transform (fft), focusing on n point sequence decimation in time (dit) with a detailed example of an 8 point dit fft. Figure 9.11 flowgraph of decimation in time algorithm for n = 8 (oppenheim and schafer, discrete time signal processing, 3rd edition, pearson education, 2010, p. 730). Two basic varieties of cooley tukey fft are decimation in time (dit) and its fourier dual, decimation in frequency (dif). the next section illustrates decimation in time. It is possible to calculate all the fft coefficients {x k} k = 0 m 1 by using the m 2 point decimation in time algorithm. see lab 9 for details.
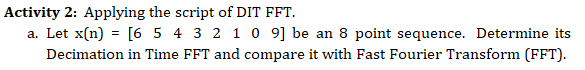
Solved Task A Create And Applying The Decimation In Time Chegg Two basic varieties of cooley tukey fft are decimation in time (dit) and its fourier dual, decimation in frequency (dif). the next section illustrates decimation in time. It is possible to calculate all the fft coefficients {x k} k = 0 m 1 by using the m 2 point decimation in time algorithm. see lab 9 for details. 7.1.2 method of decimation in time (reduced dit fft) in this method, we split the input sequence x(n) into the even indexed x(2m) and x(2m 1), each with n data points. Fast fourier transform algorithms this unit provides computationally e cient algorithms for evaluating the dft. direct computation of dft has large number addition and multiplication operations. the dft has the various applications such as linear ltering, correlation analysis, and spectrum analysis. hence an e. I chose to implement the decimation in time (dit) form of a fft not because i thought it would result in an efficient implementation but rather because the algorithm seemed conceptually simpler. A radix 2 decimation in time (dit) fft is the simplest and most common form of the cooley–tukey algorithm, although highly optimized cooley–tukey implementations typically use other forms of the algorithm as described below.
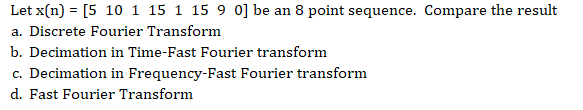
Solved Task A Create And Applying The Decimation In Time Chegg 7.1.2 method of decimation in time (reduced dit fft) in this method, we split the input sequence x(n) into the even indexed x(2m) and x(2m 1), each with n data points. Fast fourier transform algorithms this unit provides computationally e cient algorithms for evaluating the dft. direct computation of dft has large number addition and multiplication operations. the dft has the various applications such as linear ltering, correlation analysis, and spectrum analysis. hence an e. I chose to implement the decimation in time (dit) form of a fft not because i thought it would result in an efficient implementation but rather because the algorithm seemed conceptually simpler. A radix 2 decimation in time (dit) fft is the simplest and most common form of the cooley–tukey algorithm, although highly optimized cooley–tukey implementations typically use other forms of the algorithm as described below.
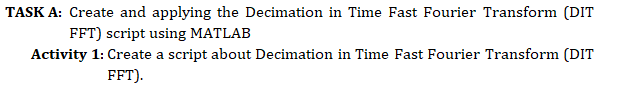
Solved Task A Create And Applying The Decimation In Time Chegg I chose to implement the decimation in time (dit) form of a fft not because i thought it would result in an efficient implementation but rather because the algorithm seemed conceptually simpler. A radix 2 decimation in time (dit) fft is the simplest and most common form of the cooley–tukey algorithm, although highly optimized cooley–tukey implementations typically use other forms of the algorithm as described below.
Comments are closed.