Digital Access Component Overview

Digital Access Component Overview In digital access, you register applications, folders, files, and urls – everything users need remote access to – as web resources (web enabled applications), tunnel resources (client server applications that are not web enabled) or customized resources. In digital access, you register applications, folders, files, and urls – everything users need remote access to – as web resources (web enabled applications), tunnel resources (client server applications that are not web enabled) or customized resources.

Digital Access Powering Digital Access In The Physical World Sap digital access occurs when humans, devices, or systems, use the digital core indirectly through non sap intermediary software, such as a non sap front end, a custom solution, or any other non sap application. Solution overview and components: review of the sd access solution building blocks (fabric overlay underlay, control plane, data plane, policy plane, management plane, and more). This guide explains the five core components, how they interact at the door, and what to consider when building or upgrading a secure, reliable access control setup. This document describes sap's digital access license model for indirect access to sap s 4hana and ecc systems. it outlines 9 types of documents that are counted for licensing, including sales orders, purchase orders, invoices, and manufacturing documents.

Digital Access Powering Digital Access In The Physical World This guide explains the five core components, how they interact at the door, and what to consider when building or upgrading a secure, reliable access control setup. This document describes sap's digital access license model for indirect access to sap s 4hana and ecc systems. it outlines 9 types of documents that are counted for licensing, including sales orders, purchase orders, invoices, and manufacturing documents. Learn more about electronic access control (eac) with our guide. discover different types of eac systems & their benefits to improve security measures. After going through this lesson, learners would gain knowledge about the major components of a digital library, including digital library collection, its organization and making it accessible through search, browse and navigation interfaces. Learn the essential components of access control systems for effective security. from readers to software, know what's crucial for your setup. Cyberark follows a layered architecturewhere each component plays a specific role: 🏛 vault— the secure core where all privileged credentials are encrypted and stored. 🌐 pvwa (privileged web.

System Overview Universal Access Panel Component Interconnection Learn more about electronic access control (eac) with our guide. discover different types of eac systems & their benefits to improve security measures. After going through this lesson, learners would gain knowledge about the major components of a digital library, including digital library collection, its organization and making it accessible through search, browse and navigation interfaces. Learn the essential components of access control systems for effective security. from readers to software, know what's crucial for your setup. Cyberark follows a layered architecturewhere each component plays a specific role: 🏛 vault— the secure core where all privileged credentials are encrypted and stored. 🌐 pvwa (privileged web.
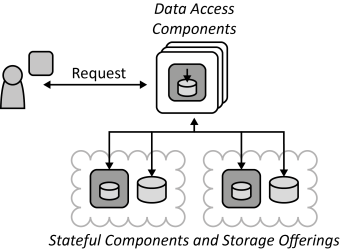
Data Access Component Cloud Computing Patterns Learn the essential components of access control systems for effective security. from readers to software, know what's crucial for your setup. Cyberark follows a layered architecturewhere each component plays a specific role: 🏛 vault— the secure core where all privileged credentials are encrypted and stored. 🌐 pvwa (privileged web.
Comments are closed.