Diffie Hellman Pdf Public Key Cryptography Key Cryptography

Diffie Hellman Key Exchange Pdf Pdf Cryptography Public Key We will study primarily the diffie hellman public key dis tribution system, the rsa public key cryptosystem, sys tem, elgamal’s digital signature system, and the digital signature standard (dss), which is a variation of elgam al’s system. We examine two approaches challenges and expect the encrypted responses in an attempt to this problem, called public key cryptosystems and public key to determine authentication key in use, thus mounting a chosen distribution systems, respectively.

Diffie Hellman Key Exchange Algorithm For Key Generation Pdf Anytime alice or bob send a message, eve has to intercept it, decrypt it using the right key, re encrypt it under the other key, and finally let the altered ciphertext pass through to its destination. 1. the diffie hellman key exchange method allows two parties to establish a secret key over an insecure channel to encrypt subsequent communications. 2. it works by having each party generate a public and private key based on pre agreed values like a prime number. they then exchange the public keys to derive a common secret key only known to. Diffie hellman key exchange – example: graphic keys over a public channel. it enables two parties to establish a shared secret key, which can then be used for secure communication via symmetric encryption, even if an eavesd opper is listening to the exchange. below is a d ep of diffie hellman key ex. From the presentation on rsa cryptography in lecture 12, you saw that public key cryptography, at least when using the rsa algorithm, is not suitable for the encryption of the actual message content.
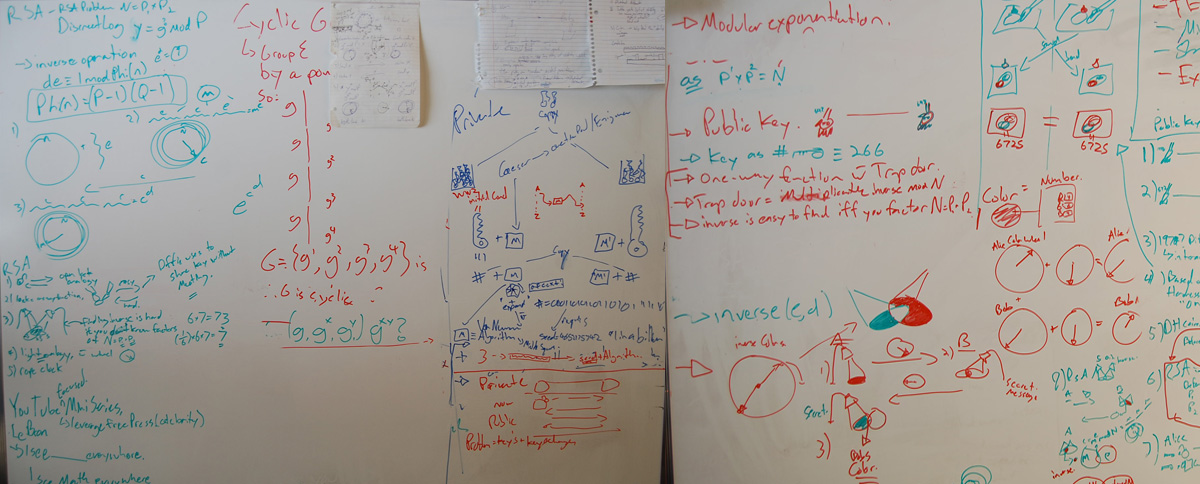
Public Key Cryptography Diffie Hellman Key Exchange Brit Cruise Diffie hellman key exchange – example: graphic keys over a public channel. it enables two parties to establish a shared secret key, which can then be used for secure communication via symmetric encryption, even if an eavesd opper is listening to the exchange. below is a d ep of diffie hellman key ex. From the presentation on rsa cryptography in lecture 12, you saw that public key cryptography, at least when using the rsa algorithm, is not suitable for the encryption of the actual message content. New directions in cryptography (die hellman 1976) asymmetry can be used to achieve secure key exchange over a public channel in the presence of eavesdroppers. introduction of the notion of public key cryptography. The diffie hellman key agreement protocol (1976) was the first practical method for establishing a shared secret over an unsecured communication channel. the point is to agree on a key that two parties can use for a symmetric encryption, in such a way that an eavesdropper cannot obtain the key. Ks problem : tion abo. y (no s. 0 . i ↑ o . y o ↑ 1. key exchang. o 1 = k ot. quodp = g [2 3. large p odulus la. discrete. odulus la. discrete. ure discr. om ga and gb. not discrete. ll p. It was precisely this work that started the revolution and in the second paragraph of the paper we can see why: in it, diffie and hellman point out the need to address the main disadvantages of public key cryptography:.
Comments are closed.