Difference Between Authentication And Authorisation By Pallavi Yesane

What The Difference Between Authorisation And Authentication Access to a system is protected by both authentication and authorization. if the attempt is authenticated but not authorized, the system will deny access to the system. Authentication and authorization are key security steps that ensure only the right users access a system and can perform permitted actions. authentication verifies who you are, and authorization determines what you can do.

Topics #newblogpost #authentication #authorization #systemsecurity difference between authentication and authorization? authentication means confirming your own…. Authentication and authorization both are two distinct concepts and serve different purposes. both terms comes into picture at time of system security and gaining access to the system. …. This tutorial compares authentication and authorization and lists the main differences between them. learning these differences will help you in managing the network more confidently. Authentication verifies identity; authorization defines access rights this question is part of this quiz : authentication & authorization in next.js.
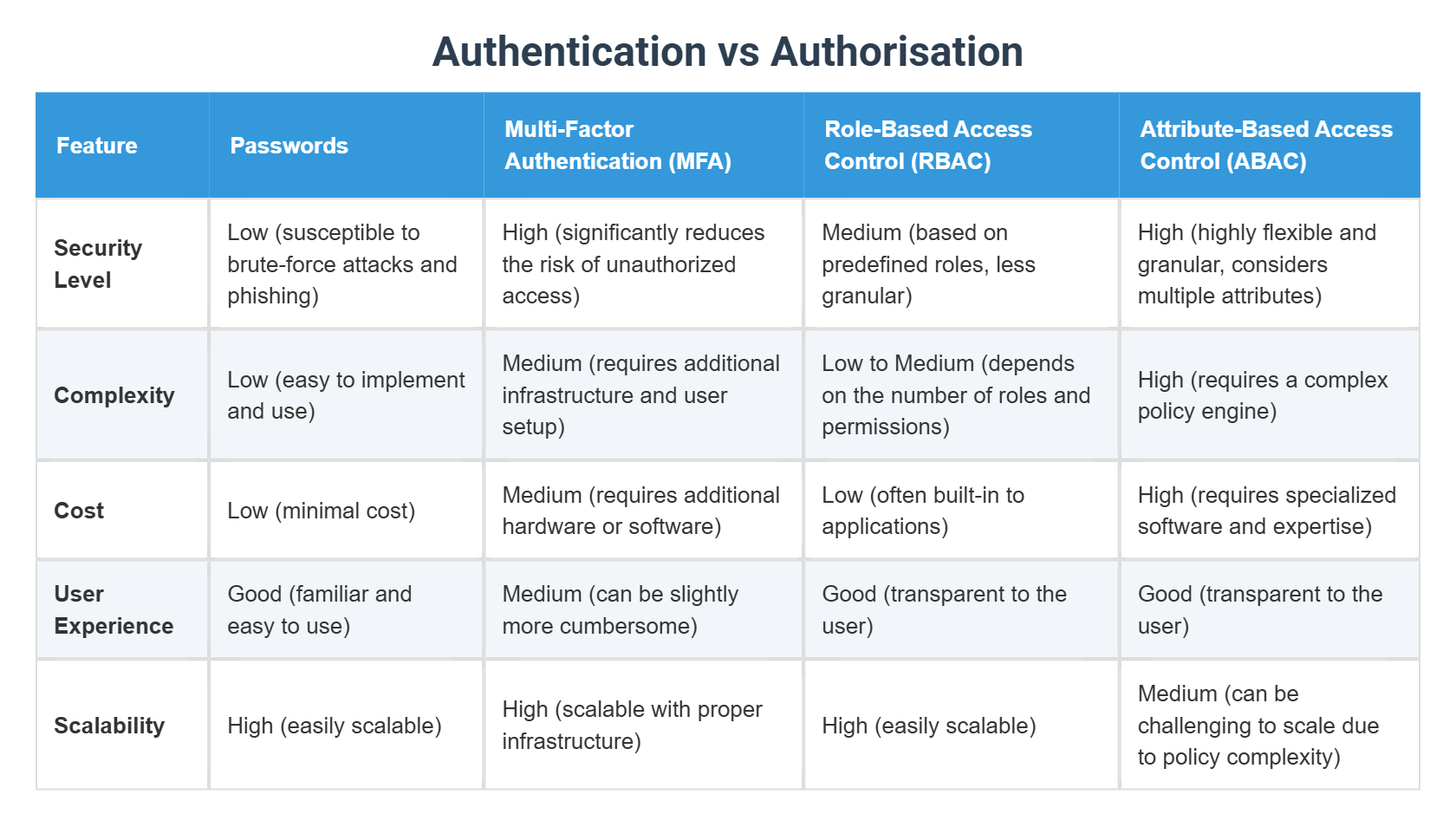
Authentication Vs Authorisation This tutorial compares authentication and authorization and lists the main differences between them. learning these differences will help you in managing the network more confidently. Authentication verifies identity; authorization defines access rights this question is part of this quiz : authentication & authorization in next.js. Explore the differences between authentication and authorization. while often used interchangeably, authentication and authorization represent fundamentally different functions. in this article, we compare and contrast the two to show how they protect applications in complementary ways. In this blog, we will break down the differences between these protocols, explore common security risks, discuss real world attacks, and provide security professionals with valuable insights for penetration testing and securing authentication systems. This article explores the differences, mechanisms, and best practices for implementing authentication and authorization in system design, highlighting their importance in modern distributed systems. Authentication ensures that users are who they claim to be, while authorization ensures they can only access what they’re permitted to see or do. understanding these concepts and implementing them correctly is fundamental to identity and access management.
Difference Between Authentication And Authorisation By Pallavi Yesane Explore the differences between authentication and authorization. while often used interchangeably, authentication and authorization represent fundamentally different functions. in this article, we compare and contrast the two to show how they protect applications in complementary ways. In this blog, we will break down the differences between these protocols, explore common security risks, discuss real world attacks, and provide security professionals with valuable insights for penetration testing and securing authentication systems. This article explores the differences, mechanisms, and best practices for implementing authentication and authorization in system design, highlighting their importance in modern distributed systems. Authentication ensures that users are who they claim to be, while authorization ensures they can only access what they’re permitted to see or do. understanding these concepts and implementing them correctly is fundamental to identity and access management.

The Difference Between Authentication And Authorization This article explores the differences, mechanisms, and best practices for implementing authentication and authorization in system design, highlighting their importance in modern distributed systems. Authentication ensures that users are who they claim to be, while authorization ensures they can only access what they’re permitted to see or do. understanding these concepts and implementing them correctly is fundamental to identity and access management.
Comments are closed.