Developing A Security Strategy Document

Creating A Company Culture For Security Design Document Pdf An effective security strategy is comprehensive and dynamic, with the elasticity to respond to any type of security threat. developing a security strategy is a detailed process that involves initial assessment, planning, implementation and constant monitoring. Developing a security strategy free download as pdf file (.pdf), text file (.txt) or read online for free. the document discusses developing an effective security strategy for an organization.

Developing A Security Strategy Pdf Strategic Management Computer To help governments in this endeavour, a consortium of partner organisations jointly developed and published the first guide to developing a national cybersecurity strategy (ncs) in 2018 . Learn how to build a cybersecurity strategy and plan that helps organizations prevent and respond to threats effectively. Our security & risk team can help you with identifying and categorising risk, setting goals and objectives, assessing technology and security controls, identifying and implementing appropriate frameworks and policies, and all aspects of security strategy development and implementation. Chapter 1 explains what a cybersecurity strategy document is, why it is necessary, and how it relates to policy or operations manuals. clear examples are provided, including the names of tools like splunk, crowdstrike, and nessus, along with concrete steps you can implement immediately next week.
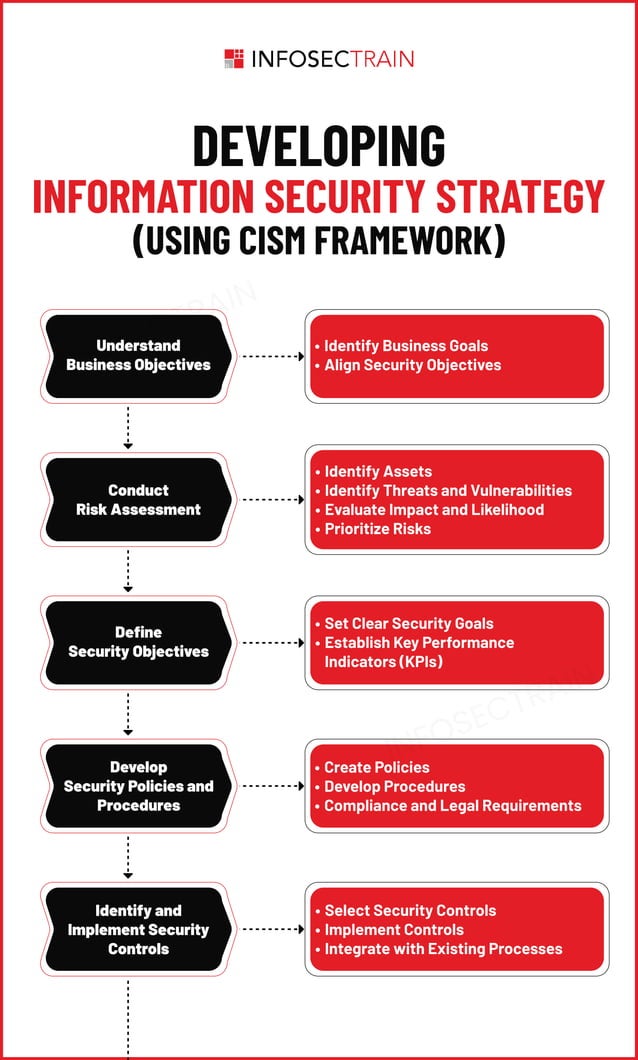
Developing Information Security Strategy Pdf Our security & risk team can help you with identifying and categorising risk, setting goals and objectives, assessing technology and security controls, identifying and implementing appropriate frameworks and policies, and all aspects of security strategy development and implementation. Chapter 1 explains what a cybersecurity strategy document is, why it is necessary, and how it relates to policy or operations manuals. clear examples are provided, including the names of tools like splunk, crowdstrike, and nessus, along with concrete steps you can implement immediately next week. Develop an information security policy an information security policy is a written document that guides the workforce on the proper use of technology and company assets while on the job. In this article, we will explore the key components of an effective security strategy and provide guidance on how organisations can develop and implement one. as technology continues to advance, so do the threats that organisations face. Before building out specific security measures, it’s crucial to understand the foundational requirements that will shape your strategy. this involves identifying applicable industry regulations (like hipaa), legal obligations, and specific business objectives related to security. Summarize the key points and emphasize the importance of ongoing commitment to cybersecurity. a structured template for creating a cybersecurity strategy document.
Developing An Effective Security Strategy City Security Magazine Develop an information security policy an information security policy is a written document that guides the workforce on the proper use of technology and company assets while on the job. In this article, we will explore the key components of an effective security strategy and provide guidance on how organisations can develop and implement one. as technology continues to advance, so do the threats that organisations face. Before building out specific security measures, it’s crucial to understand the foundational requirements that will shape your strategy. this involves identifying applicable industry regulations (like hipaa), legal obligations, and specific business objectives related to security. Summarize the key points and emphasize the importance of ongoing commitment to cybersecurity. a structured template for creating a cybersecurity strategy document.
Comments are closed.