Detection Using Computer File Hash Values

Online File Hash Calculator To Check File Hash Values For Free Learn how file hashing creates unique digital fingerprints to verify file integrity, detect tampering, and identify malicious files in cybersecurity defense. In this short 45–60 second explainer, we break down sha 256 hashing, the avalanche effect, and how antivirus & threat hunting tools (crowdstrike, huntress, windows defender) use hashes for.

Online File Hash Calculator To Check File Hash Values For Free File hashes let analysts quickly check a suspicious file against known malware. hashing (e.g., md5 sha1 sha256) is lightweight, so huge malware collections can be indexed and searched efficiently. Hash values allow investigators to quickly identify duplicate files and eliminate unnecessary data. instead of manually reviewing gigabytes of data, they can simply compare hash values to detect duplicates. Use osforensics to confirm that files have not been corrupted or tampered with by comparing hash values, or identify whether an unknown file belongs to a known set of files. Master file hashing with our comprehensive guide. learn md5, sha 1, sha 256 algorithms, verify file integrity, and secure file validation best practices.
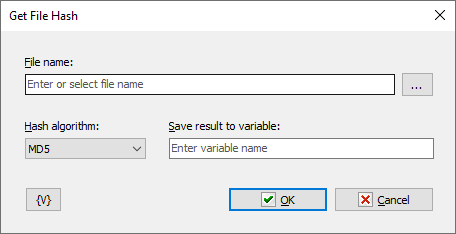
Actions Files And Folders Get File Hash Use osforensics to confirm that files have not been corrupted or tampered with by comparing hash values, or identify whether an unknown file belongs to a known set of files. Master file hashing with our comprehensive guide. learn md5, sha 1, sha 256 algorithms, verify file integrity, and secure file validation best practices. Be able to write a simple python script that generates and compares hashes to detect changes in files, which can be used as a basic technique for malware detection. When you create forensic images or handle critical files, generating hash values (like md5, sha 1, or sha 256) is essential. these hashes act as digital fingerprints, allowing you to verify that files remain unchanged during transfers or storage. Verify file integrity instantly with our free online file hash checker. upload any file to compute md5, sha 1, sha 256, and sha 512 hashes—then compare with original or expected checksums. perfect for ensuring downloaded files are intact, validating software authenticity, or detecting corruption. all processing happens locally in your browser for privacy. In cybersecurity, these hash values serve as digital fingerprints for files, enabling rapid identification of malware samples, verification of file integrity, and detection of unauthorized modifications.
Hash Value In Computer Forensics Dna Of Digital Evidence Be able to write a simple python script that generates and compares hashes to detect changes in files, which can be used as a basic technique for malware detection. When you create forensic images or handle critical files, generating hash values (like md5, sha 1, or sha 256) is essential. these hashes act as digital fingerprints, allowing you to verify that files remain unchanged during transfers or storage. Verify file integrity instantly with our free online file hash checker. upload any file to compute md5, sha 1, sha 256, and sha 512 hashes—then compare with original or expected checksums. perfect for ensuring downloaded files are intact, validating software authenticity, or detecting corruption. all processing happens locally in your browser for privacy. In cybersecurity, these hash values serve as digital fingerprints for files, enabling rapid identification of malware samples, verification of file integrity, and detection of unauthorized modifications.
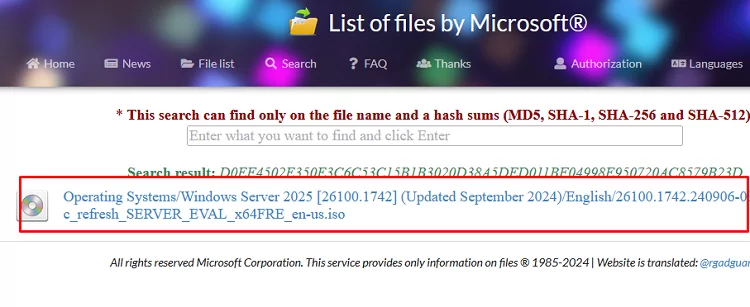
How To Verify A File Hash Checksum On Windows Windows Os Hub Verify file integrity instantly with our free online file hash checker. upload any file to compute md5, sha 1, sha 256, and sha 512 hashes—then compare with original or expected checksums. perfect for ensuring downloaded files are intact, validating software authenticity, or detecting corruption. all processing happens locally in your browser for privacy. In cybersecurity, these hash values serve as digital fingerprints for files, enabling rapid identification of malware samples, verification of file integrity, and detection of unauthorized modifications.

Methodology Of Malicious File Hash Detection Download High
Comments are closed.