Detection Based On Return Codes
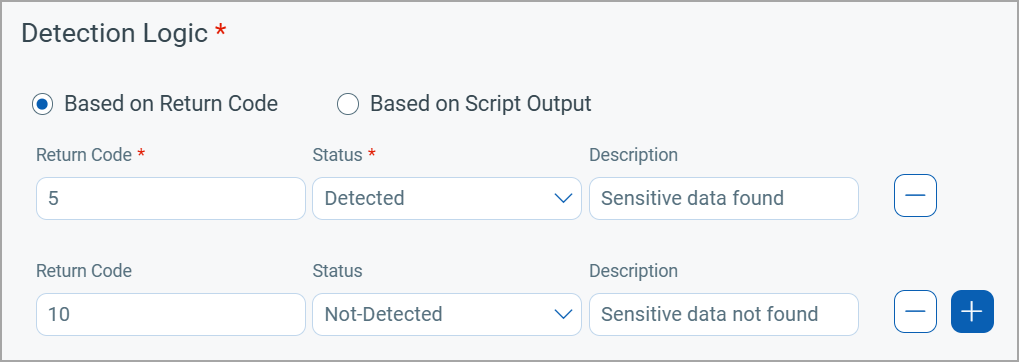
Detection Based On Return Codes The detection logic for a custom qid is based on the exit code the script returns. the exit codes returned by the script must match the provided return codes to detect the custom qid. Use copyleaks' ai powered programming code plagiarism checker to find plagiarized code & safeguard your org against code plagiarism.

Detect Label Format And Enrich Code Detection as code (dac) is a structured approach to writing detections by incorporating software engineering best practice principles. this means that detection engineers and analysts will. This paper introduces a transfer learning based method to tackle the imbalanced data issue in cybersecurity using return oriented programming (rop) payload detection as a case study. Return oriented programming (rop) is a code reuse attack that chains short snippets of existing code to perform arbitrary operations on target machines. existing detection methods against rop exhibit unsatisfactory detection accuracy and or have high runtime overhead. This process is based on finding correspondences between points in the real environment and their 2d image projection. this is usually a difficult step, and thus it is common to use synthetic or fiducial markers to make it easier.
Error Detection And Correction Codes Return oriented programming (rop) is a code reuse attack that chains short snippets of existing code to perform arbitrary operations on target machines. existing detection methods against rop exhibit unsatisfactory detection accuracy and or have high runtime overhead. This process is based on finding correspondences between points in the real environment and their 2d image projection. this is usually a difficult step, and thus it is common to use synthetic or fiducial markers to make it easier. This research develops a common framework for profile guided code self verification based on predetermined security and performance requirements. we use return oriented programming (rop) which is used mostly by adversaries for the defensive purpose to build self verifying rop chain. There are three mech anisms proposed by researchers for detecting and defeating return oriented attacks. the first method suggests a defense that looks for frequent instruction streams with returns. Examples # this is the gallery of examples that showcase how scikit learn can be used. some examples demonstrate the use of the api in general and some demonstrate specific applications in tutorial form. also check out our user guide for more detailed illustrations. This article describes some effective methods for detecting rop attacks and hooks that we apply for protecting our applications.
Github Linhnvhdev Detection As Code Fpt Intern Detection As Code Project This research develops a common framework for profile guided code self verification based on predetermined security and performance requirements. we use return oriented programming (rop) which is used mostly by adversaries for the defensive purpose to build self verifying rop chain. There are three mech anisms proposed by researchers for detecting and defeating return oriented attacks. the first method suggests a defense that looks for frequent instruction streams with returns. Examples # this is the gallery of examples that showcase how scikit learn can be used. some examples demonstrate the use of the api in general and some demonstrate specific applications in tutorial form. also check out our user guide for more detailed illustrations. This article describes some effective methods for detecting rop attacks and hooks that we apply for protecting our applications.
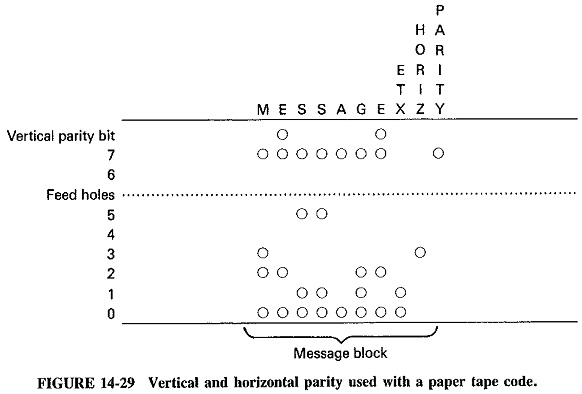
Error Detection And Correction Codes Redundant Codes Retransmission Examples # this is the gallery of examples that showcase how scikit learn can be used. some examples demonstrate the use of the api in general and some demonstrate specific applications in tutorial form. also check out our user guide for more detailed illustrations. This article describes some effective methods for detecting rop attacks and hooks that we apply for protecting our applications.
Comments are closed.