Detection And Blocking Wallarm Documentation

Wallarm Cyber Security Solutions Pdf Vulnerability Computing If your user reports a legitimate request being blocked despite the wallarm measures, you can review and evaluate their requests as this articles explains. to resolve the issue of a legitimate request being blocked by wallarm, follow these steps:. Wallarm delivers real time protection for apis and ai agents, stopping automated threats and abuse while also providing full security visibility with complete api inventory and risk detection.
Detection And Blocking Wallarm Documentation Wallarm delivers real time protection for apis and ai agents, stopping automated threats and abuse while also providing full security visibility with complete api inventory and risk detection. It is wallarm’s ability to map out network services landscapes and discover application vulnerabilities—wallarm scanner—that we want to talk about here. The wallarm platform continuously analyzes application traffic and mitigates malicious requests in real time. from this article, you will learn resource types wallarm protects from attacks, methods of detecting attacks in traffic and how you can track and manage detected threats. Wallarm is a set of protection tools. if they work not as expected, you can always tune them under your specific needs and situation. this article describes how to do that.

Wallarm Detection Updates Wallarm Api Security Wallarm Updates The wallarm platform continuously analyzes application traffic and mitigates malicious requests in real time. from this article, you will learn resource types wallarm protects from attacks, methods of detecting attacks in traffic and how you can track and manage detected threats. Wallarm is a set of protection tools. if they work not as expected, you can always tune them under your specific needs and situation. this article describes how to do that. Wallarm provides a set of default mitigation controls that, when enabled, significantly enhance the detection capabilities of the wallarm platform. these controls are pre configured to offer robust protection against a variety of common attack patterns. From this article, you will learn resource types wallarm protects from attacks, methods of detecting attacks in traffic and how you can track and manage detected threats. As wallarm provides many different methods of detecting vulnerabilities, the questions arise about which of them to choose and how to combine them. consider the information below to answer this. Configuration of the blocking page and error code is supported in nginx based wallarm node deployments but is not supported in envoy and cdn based wallarm node deployments.
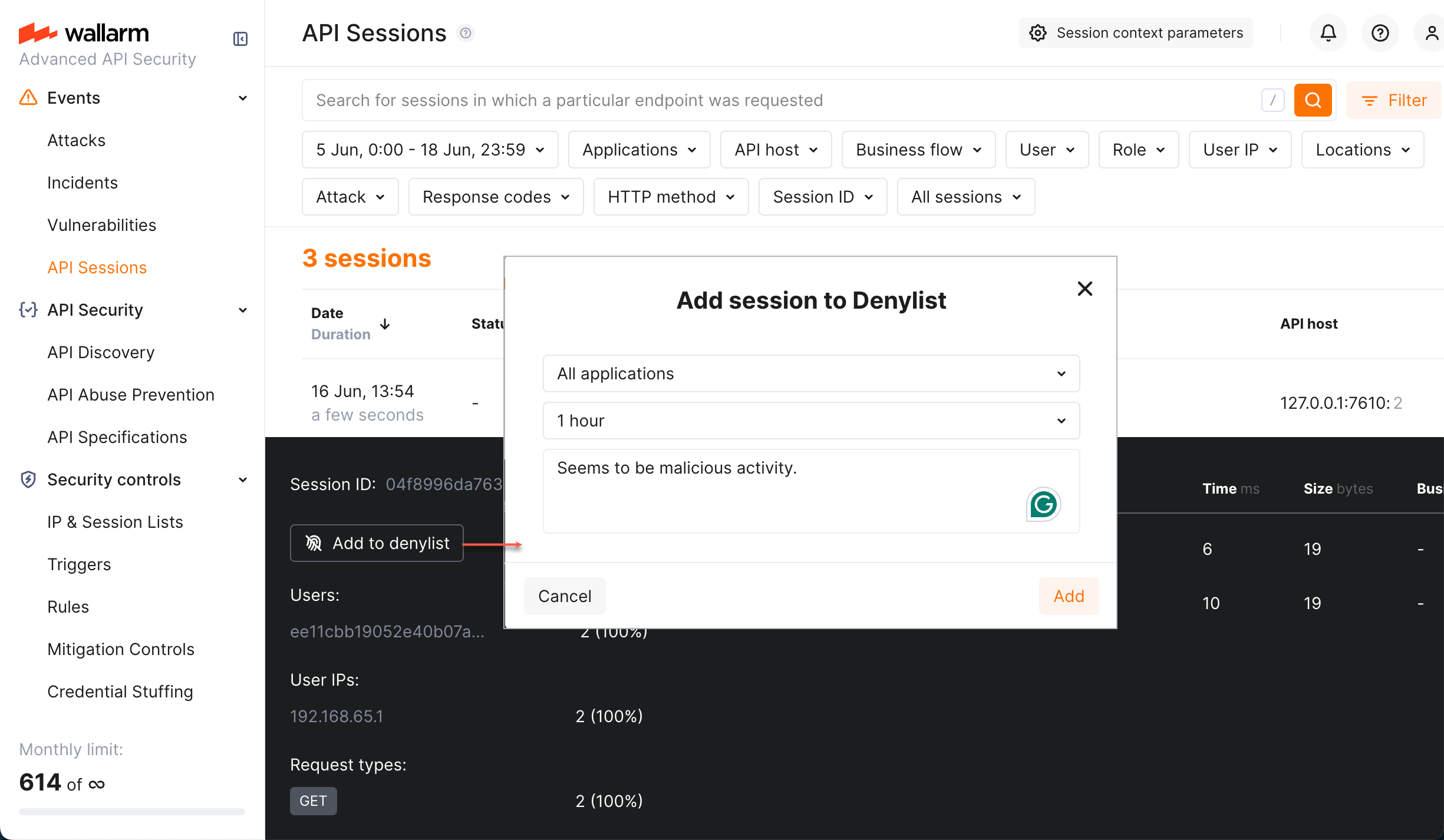
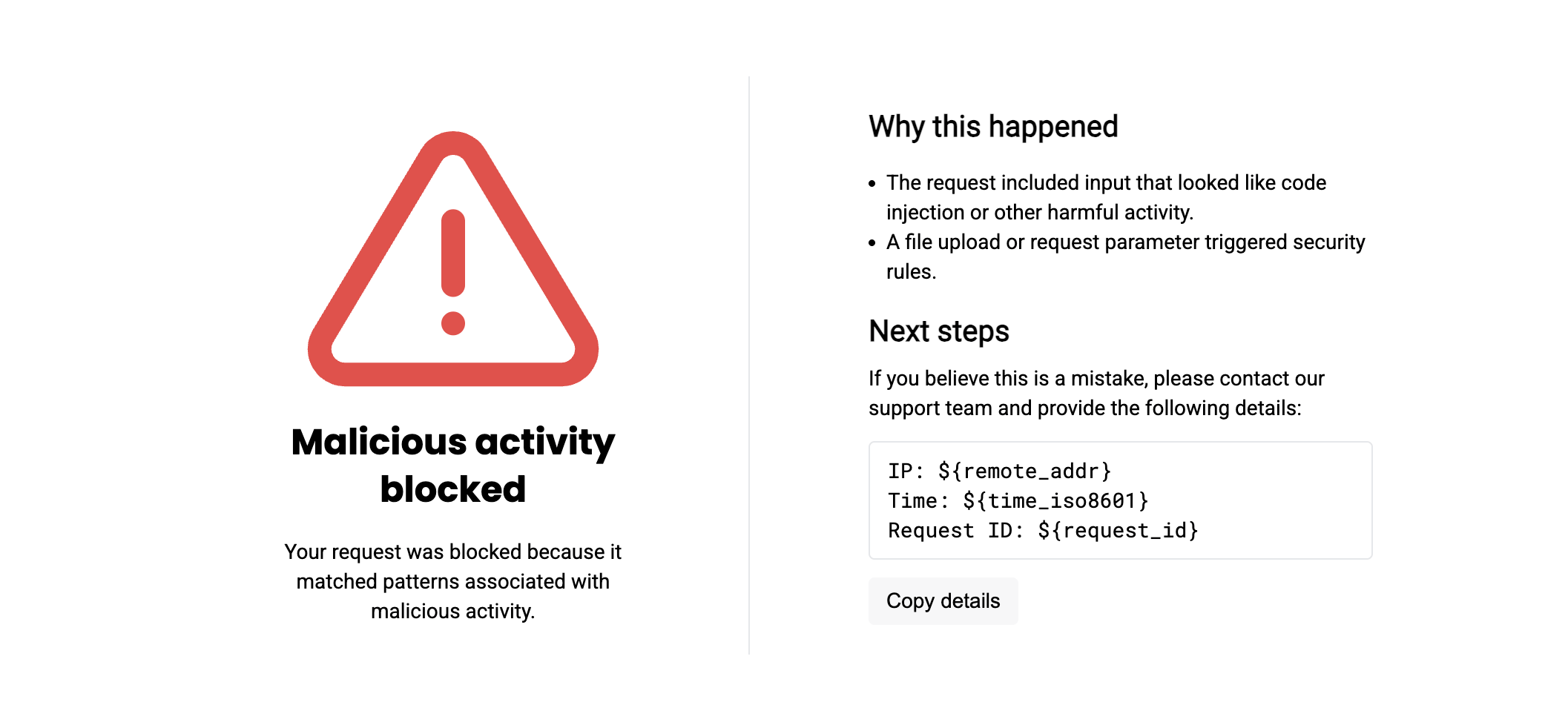
Blocking Wallarm Documentation Wallarm provides a set of default mitigation controls that, when enabled, significantly enhance the detection capabilities of the wallarm platform. these controls are pre configured to offer robust protection against a variety of common attack patterns. From this article, you will learn resource types wallarm protects from attacks, methods of detecting attacks in traffic and how you can track and manage detected threats. As wallarm provides many different methods of detecting vulnerabilities, the questions arise about which of them to choose and how to combine them. consider the information below to answer this. Configuration of the blocking page and error code is supported in nginx based wallarm node deployments but is not supported in envoy and cdn based wallarm node deployments.

Wallarm Cloud Native Application And Api Security As wallarm provides many different methods of detecting vulnerabilities, the questions arise about which of them to choose and how to combine them. consider the information below to answer this. Configuration of the blocking page and error code is supported in nginx based wallarm node deployments but is not supported in envoy and cdn based wallarm node deployments.
Comments are closed.