Detecting Linux Kernel Process Masquerading With Command Line Forensics
Detecting Linux Kernel Process Masquerading With Command Line Forensics Now that you know what linux kernel thread masquerading looks like, let’s setup a test so you can play with how to find it using command line forensics. we’ll use the sleep command for our simulation as you can do it on any system without fear of causing trouble. Now you have two solid ways to use the linux command line to investigate suspicious processes trying to masquerade as kernel threads. adapted from original post which appeared on sandfly security.
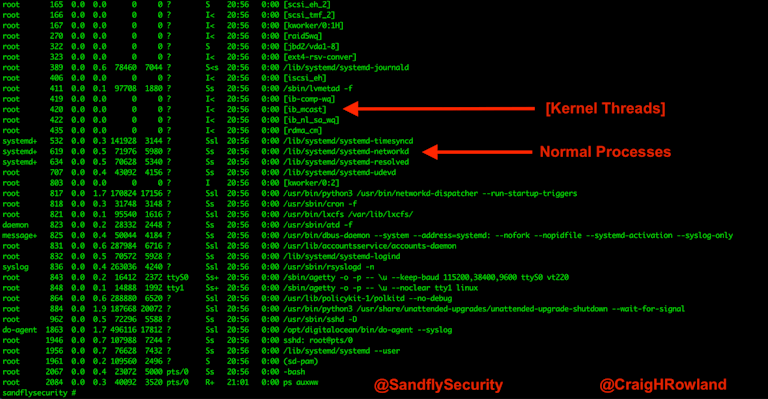
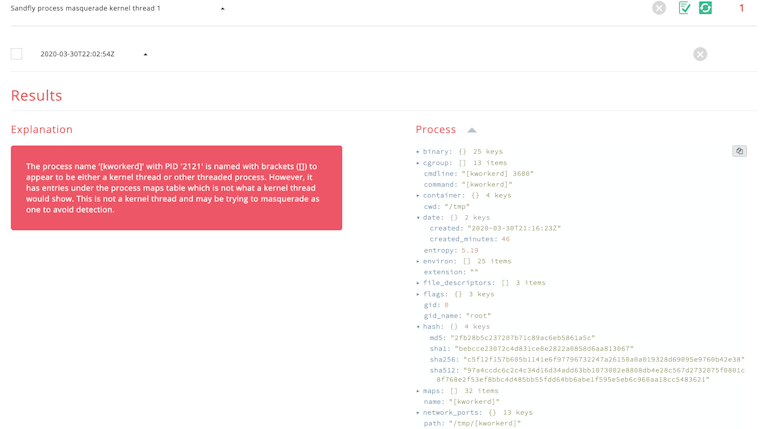
Detecting Linux Kernel Process Masquerading With Command Line Forensics Now that you know what linux kernel thread masquerading looks like, let’s setup a test so you can play with how to find it using command line forensics. we’ll use the sleep command for. Linux kernel process masquerading is sometimes used by malware to hide when it is running. let’s go over how you can unmask a piece of linux malware using this tactic. My hackable attempt to automate the process of detecting malicious kernel process thread (dmkpt) based on the blog post ( sandflysecurity blog detecting linux kernel process masquerading with command line forensics ). In linux environments, kernel processes like `kthreadd` and `kworker` typically run without associated executable paths. adversaries exploit this by naming malicious executables after these processes to evade detection.
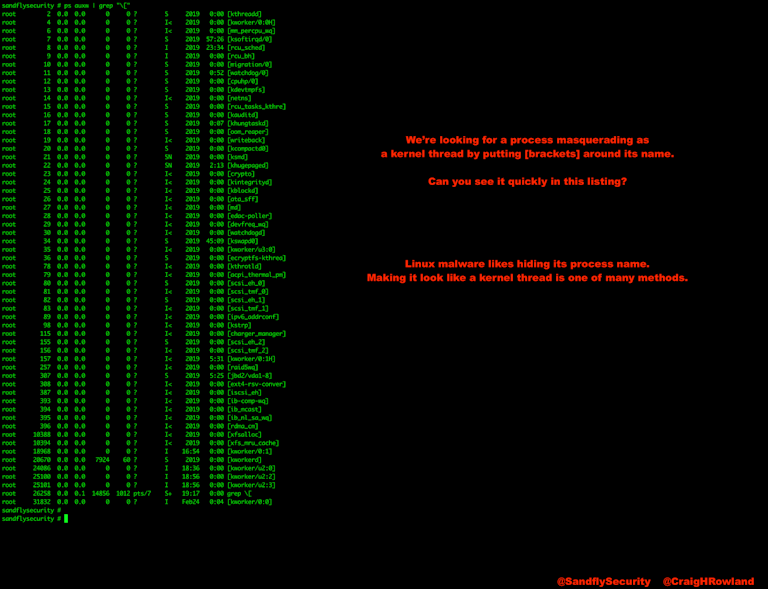
Detecting Linux Kernel Process Masquerading With Command Line Forensics My hackable attempt to automate the process of detecting malicious kernel process thread (dmkpt) based on the blog post ( sandflysecurity blog detecting linux kernel process masquerading with command line forensics ). In linux environments, kernel processes like `kthreadd` and `kworker` typically run without associated executable paths. adversaries exploit this by naming malicious executables after these processes to evade detection. → utility to quickly scan for linux process ids (pids) that are hidden by common and not so common loadable kernel module stealth rootkits and decloak them so they are visible. Learn to identify malware indicators on linux. use command line tools for basic forensic analysis, system monitoring, and detecting suspicious process and file activity. The document is a comprehensive cheat sheet for advanced linux detection and forensics, detailing various commands and file paths for analyzing system processes, logs, and kernel states. Learn practical linux command line forensics techniques to detect and respond to security threats. discover how to use basic linux commands for effective system analysis and protection.

Detecting Linux Kernel Process Masquerading With Command Line Forensics → utility to quickly scan for linux process ids (pids) that are hidden by common and not so common loadable kernel module stealth rootkits and decloak them so they are visible. Learn to identify malware indicators on linux. use command line tools for basic forensic analysis, system monitoring, and detecting suspicious process and file activity. The document is a comprehensive cheat sheet for advanced linux detection and forensics, detailing various commands and file paths for analyzing system processes, logs, and kernel states. Learn practical linux command line forensics techniques to detect and respond to security threats. discover how to use basic linux commands for effective system analysis and protection.
Comments are closed.