Detecting Identity Attacks With Crowdstrike Itdr Wwt
Detecting Identity Attacks With Crowdstrike Itdr Wwt Learners use crowdstrike itdr to detect identity based threats, validate network activity with security onion, and confirm automated containment with falcon soar. Download this data sheet to learn how to strengthen your identity security posture and stop identity based attacks in real time with crowdstrike’s itdr modules.

Identity Threat Detection And Response Itdr Cybercloud Services Crowdstrike falcon identity protection detects and blocks identity threats in real time across hybrid environments. it’s built for enterprise security teams who want identity detection tightly unified with their endpoint and workload telemetry. Crowdstrike identity for ad anyone using it? this month our ciso was made aware of a new acronym itdr and now i've been tasked with identifying who provides "itdr" *sigh* to that end i found crowdstrike identity and the identity module. Crowdstrike falcon identity protection delivers identity threat detection and response (itdr) capabilities, protecting organizations from identity based attacks in real time. Itdr is a critical piece of an enterprise’s identity fabric. it adds an additional layer of protection, identifying both insider threats and external threat actors who have gained access to the.
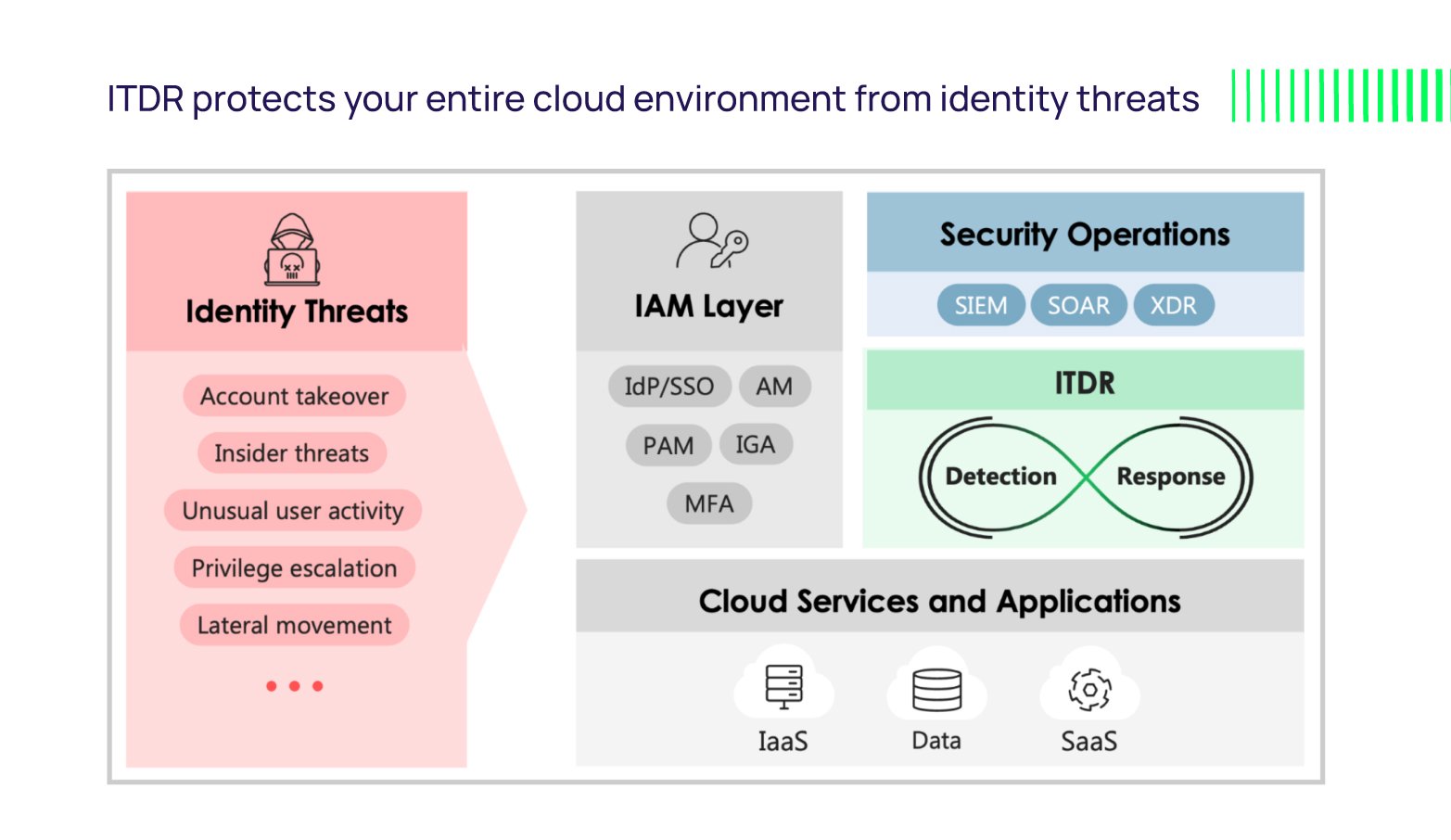
How To Protect Against Identity Based Attacks With Itdr Crowdstrike falcon identity protection delivers identity threat detection and response (itdr) capabilities, protecting organizations from identity based attacks in real time. Itdr is a critical piece of an enterprise’s identity fabric. it adds an additional layer of protection, identifying both insider threats and external threat actors who have gained access to the. One such treasure within the crowdstrike suite is the identity protection module (idp). as we began exploring this module, we recognized the possibilities it offered but finding detailed guidance was a challenge. Protect your organization with crowdstrike falcon identity threat detection and response (itdr) to detect identity based attacks, anomalies, and lateral movement in real time. Learn how to prevent, detect, and respond to identity attacks in real time with identity threat protection and response (itdr). Learn how to detect and stop identity based attacks before attackers move laterally through your network.

Identity Threat Detection And Response Itdr Rips In Your Identity One such treasure within the crowdstrike suite is the identity protection module (idp). as we began exploring this module, we recognized the possibilities it offered but finding detailed guidance was a challenge. Protect your organization with crowdstrike falcon identity threat detection and response (itdr) to detect identity based attacks, anomalies, and lateral movement in real time. Learn how to prevent, detect, and respond to identity attacks in real time with identity threat protection and response (itdr). Learn how to detect and stop identity based attacks before attackers move laterally through your network.
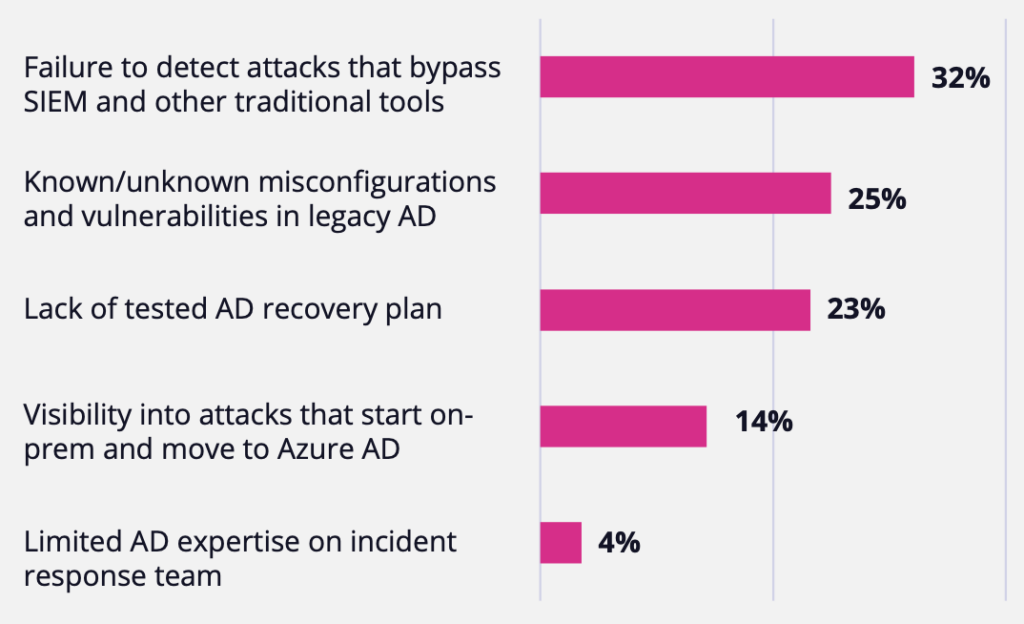
Evaluate Identity Threat Detection Response Solutions Semperis Learn how to prevent, detect, and respond to identity attacks in real time with identity threat protection and response (itdr). Learn how to detect and stop identity based attacks before attackers move laterally through your network.

Identity Threat Detection And Response Itdr Explained
Comments are closed.