Detect Hardcoded Secrets In Pre Commit Hooks Github Actions With Ggshield The Gitguardian Cli

How To Use Github Actions Secrets To Hide Sensitive Data Ggshield is a cli application that runs in your local environment or in a ci environment to help you detect more than 500 types of secrets. ggshield uses our public api through py gitguardian to scan and detect potential vulnerabilities in files and other text content. Detect secrets in source code, scan git repos, and use pre commit hooks to prevent api key leaks. from @gitguardian. 🛠 fasten your security belt with ggshield. it's a free and open source cli from @gitguardian that detects 🔐 secrets 🔐 in your git repos. try it (and don't forget to star the repo 🌟).
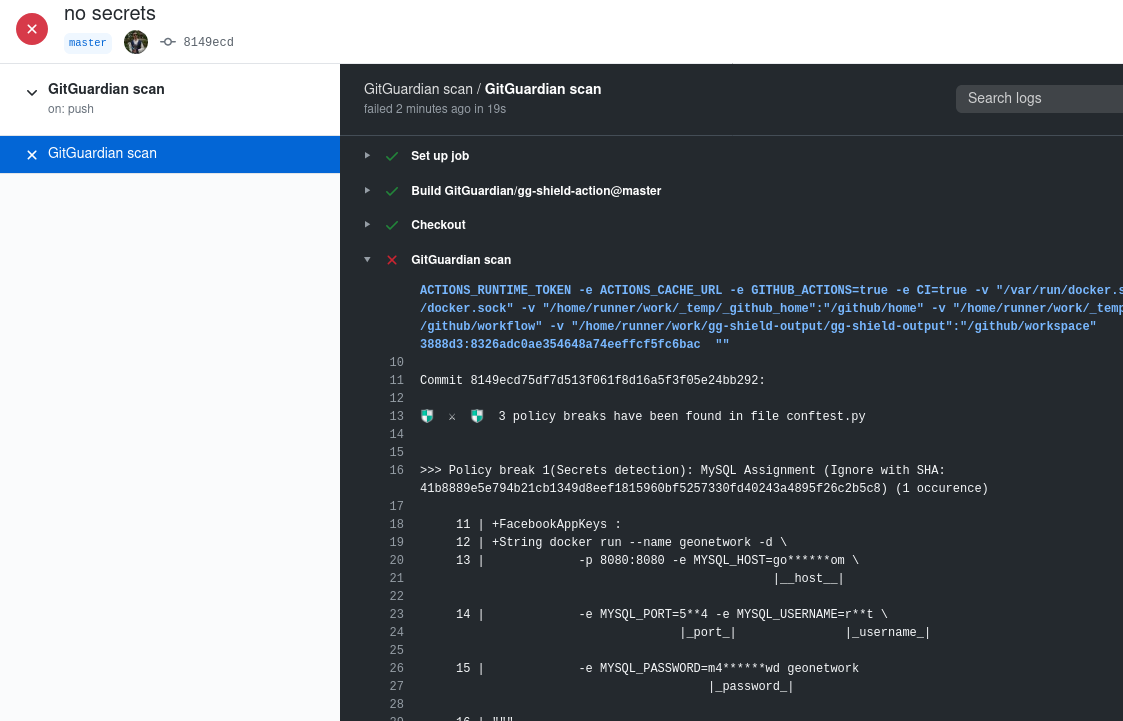
Github Actions Gitguardian Documentation In a sdlc, it is majorly used as a pre commit hook but there are other solutions that is also used to scan all the commits and the history to check for an exposed secret. This page explains how to integrate ggshield with git's pre commit hook system to detect secrets in code before they are committed to a repository. for information about pre push and pre receive hooks. In this video, we will run through how to use gitguardian shield to create a pre commit hook and github action workflow to scan your commits for secrets. In this tutorial, you will learn how to add gitguardian real time monitoring to a circleci workflow to scan every new commit for secrets. gitguardian detects secrets in your repositories in the history or in incremental commits.
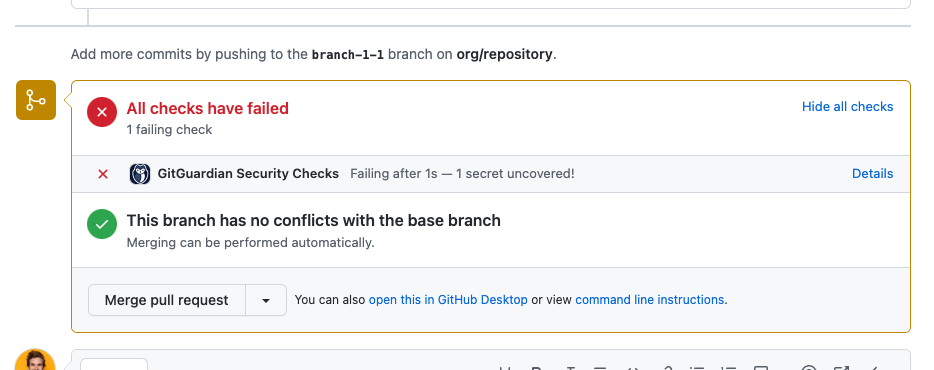
Detect Secrets In Github Prs Gitguardian Documentation In this video, we will run through how to use gitguardian shield to create a pre commit hook and github action workflow to scan your commits for secrets. In this tutorial, you will learn how to add gitguardian real time monitoring to a circleci workflow to scan every new commit for secrets. gitguardian detects secrets in your repositories in the history or in incremental commits. A pre commit hook is a short (or long!) snippet of code that is run, as you guessed before anything is committed in git. for our use case, this is actually the best moment to scan for credentials and secrets, since once one has created a git commit, it can be annoying to have to rewrite the history. Git hooks allow you to "hook" into different git lifecycle events in order to run your own code. for example, the pre commit hook allows you to run your own code before you create a new git commit. this is the perfect place to scan for secrets, and ggshield supports this workflow out of the box. Gitguardian's ggshield can help you quickly find any secrets in your repos, local files, archives, and commits. the cli tool can also help you avoid sharing your secrets in your ci pipeline, docker files, and even dependencies. Setting up a pre commit git hook with ggshield, the gitguardian cli. in this tutorial we are going to run through how to create a pre commit git hook using gitguardian shield to detect secrets before they enter your repository.
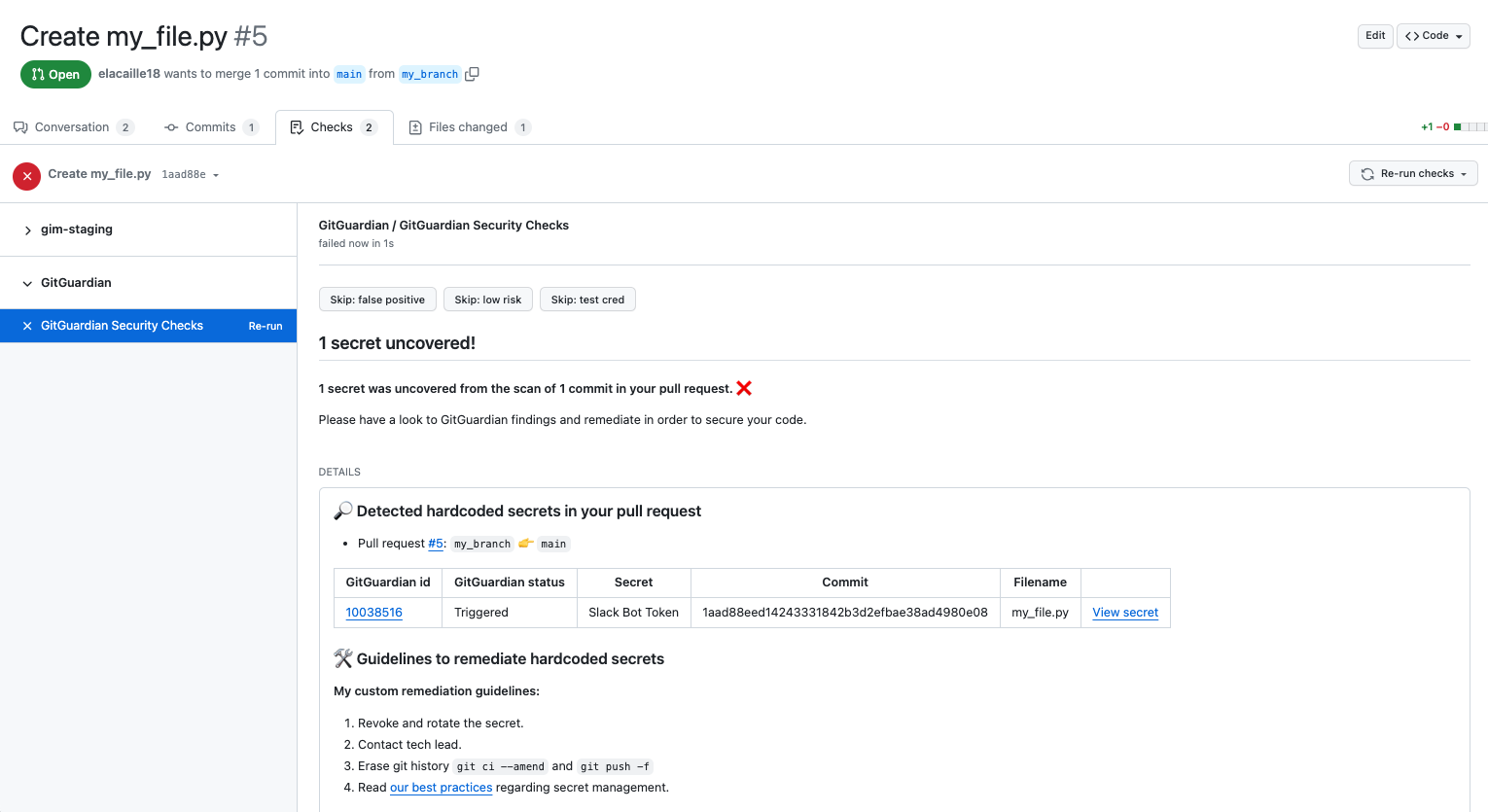
Detect Secrets In Github Prs Gitguardian Documentation A pre commit hook is a short (or long!) snippet of code that is run, as you guessed before anything is committed in git. for our use case, this is actually the best moment to scan for credentials and secrets, since once one has created a git commit, it can be annoying to have to rewrite the history. Git hooks allow you to "hook" into different git lifecycle events in order to run your own code. for example, the pre commit hook allows you to run your own code before you create a new git commit. this is the perfect place to scan for secrets, and ggshield supports this workflow out of the box. Gitguardian's ggshield can help you quickly find any secrets in your repos, local files, archives, and commits. the cli tool can also help you avoid sharing your secrets in your ci pipeline, docker files, and even dependencies. Setting up a pre commit git hook with ggshield, the gitguardian cli. in this tutorial we are going to run through how to create a pre commit git hook using gitguardian shield to detect secrets before they enter your repository.
Comments are closed.