Deployment Example 1 With Inline Ssl Decryption
How To Implement And Test Ssl Decryption Palo Alto Networks Live Pdf In this deployment, the gigavue os and gigavue‑fm node does not have access to the private keys of the server, but as a trusted mitm, the gigavue os and gigavue‑fm node can look at tls ssl traffic. In an inline deployment, the system processes the tls ssl handshake, potentially modifying the clienthello message and acting as a tcp proxy server for the session. the following figure shows an inline deployment.

How To Implement And Test Ssl Decryption Knowledge Base Palo Alto Configure ssl inbound inspection to decrypt and inspect inbound ssl tls traffic from clients to targeted network servers and block suspicious sessions. for example, suppose a malicious actor wants to exploit a known vulnerability with your web server. This document will provide a comprehensive overview of inline tls ssl decryption using gigasmart, including its configuration, validation of the solution, and best practices. For such solutions to work effectively, we need dedicated decryption solutions so that the security devices can enforce policies without the hassle of decryption. this guide provides step by step instructions for the deployment of a10 thunder® ssl insight® (ssli®) using appcentric templates. You can use this procedure to deploy a certificate to multiple client machines with active directory domain services and a group policy object (gpo). a gpo can contain multiple configuration options, and is applied to all computers in the scope of the gpo.
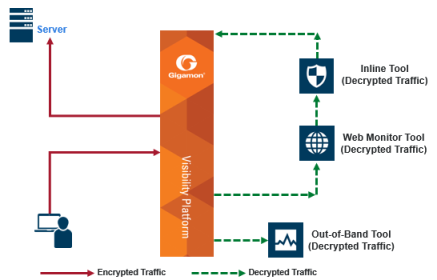
Example Inline Tls Ssl Decryption For such solutions to work effectively, we need dedicated decryption solutions so that the security devices can enforce policies without the hassle of decryption. this guide provides step by step instructions for the deployment of a10 thunder® ssl insight® (ssli®) using appcentric templates. You can use this procedure to deploy a certificate to multiple client machines with active directory domain services and a group policy object (gpo). a gpo can contain multiple configuration options, and is applied to all computers in the scope of the gpo. Appliance is connected to the network inline, as shown in the following diagram. the appliance decrypts the ssl traffic and sends it to an active security device. This use case illustrates deploying gigavue hc2 device for ssl decryption and fortigate firewall in virtual wire pair for inspection and in nat route mode for routing the user’s traffic to the internet, as illustrated in figure 2 1. In this session, we'll show you best practices in deploying inline ssl tls decryption based on our experience with over 1,000 deployments. learn from our field experts how to deploy inline ssl with minimal pain and maximum gain. Once the topology is selected, you will define one or more security services to attach to the ssl orchestrator. a security service is the external component (appliance, module) that receives decrypted traffic and performs layered security functions on that traffic.
Comments are closed.