Demystifying Code To Cloud Security Devops
Demystifying Code To Cloud Security Devops Code to cloud security is an approach that blends security practices at every stage of the software development life cycle (sdlc) — from planning and development to deployment — helping prevent security breaches that could compromise your organization’s data and reputation. What is code to cloud security? code to cloud security refers to a holistic security strategy that spans the entire software development and deployment process, ensuring that security is embedded throughout—from the moment code is written to the point it runs in the cloud.

The Importance Of Devops In Cloud Security Management Bestarion In 2025, devsecops transforms software delivery by embedding development security into every phase, from code to cloud. unlike the devops vs devsecops debate, devsecops ensures speed, security, and compliance. Learn how a code to cloud security strategy integrates development and runtime data into a unified exposure management view to prioritize critical cyber risks. Code to cloud security integrates protection across the entire sdlc—from code to deployment—minimizing vulnerabilities, supporting compliance, and fostering secure devsecops practices. By embedding security into every stage—from code commits to cloud deployment—you mitigate risks like data breaches, unauthorized access, and compliance violations.

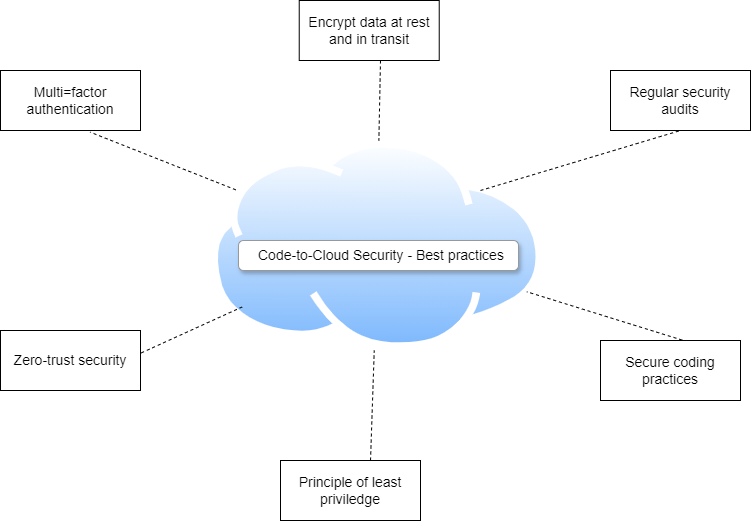
Devops Definitions Cloud Security Matoffo Code to cloud security integrates protection across the entire sdlc—from code to deployment—minimizing vulnerabilities, supporting compliance, and fostering secure devsecops practices. By embedding security into every stage—from code commits to cloud deployment—you mitigate risks like data breaches, unauthorized access, and compliance violations. By integrating automated security tools and best practices, organizations can achieve faster, safer, and more resilient software delivery. the goal is to make security seamless, allowing development teams to focus on innovation while ensuring applications remain protected from emerging threats. Learn how to implement security as code across your ci cd pipeline. covers sast, sca, container scanning, dast, secrets detection, and policy as code with practical tool recommendations for devops and engineering teams. In this guide, we explain what code to cloud is, map out code to cloud security tools, processes and security requirements for the different stages of the sdlc, discuss various approaches, details the risks and provide best practices and tools that can help. That’s where code to cloud security comes into play. here, we’ll focus on the importance of code to cloud security, its impact on organizational security posture, how companies can adopt it, and the best practices to ensure optimum results.

Demystifying Infrastructure As Code Iac Scanning Enhancing Security By integrating automated security tools and best practices, organizations can achieve faster, safer, and more resilient software delivery. the goal is to make security seamless, allowing development teams to focus on innovation while ensuring applications remain protected from emerging threats. Learn how to implement security as code across your ci cd pipeline. covers sast, sca, container scanning, dast, secrets detection, and policy as code with practical tool recommendations for devops and engineering teams. In this guide, we explain what code to cloud is, map out code to cloud security tools, processes and security requirements for the different stages of the sdlc, discuss various approaches, details the risks and provide best practices and tools that can help. That’s where code to cloud security comes into play. here, we’ll focus on the importance of code to cloud security, its impact on organizational security posture, how companies can adopt it, and the best practices to ensure optimum results.

The Role Of Devops In Cloud Security Management Infoq In this guide, we explain what code to cloud is, map out code to cloud security tools, processes and security requirements for the different stages of the sdlc, discuss various approaches, details the risks and provide best practices and tools that can help. That’s where code to cloud security comes into play. here, we’ll focus on the importance of code to cloud security, its impact on organizational security posture, how companies can adopt it, and the best practices to ensure optimum results.

Integrating Security Into Devops Security As Code
Comments are closed.