Demo Iptable Netfilter Nmap
Nmap Firewall Bypass Nutcrackerssecurity Iptables netfilter firewall examples for new linux sysadmin & developer. learn how to protect the server, display, set, modify, delete rules. We have collected the most frequently asked questions (and their respective answers) from the mailinglists. please read this faq first, before asking questions on the mailnglists.
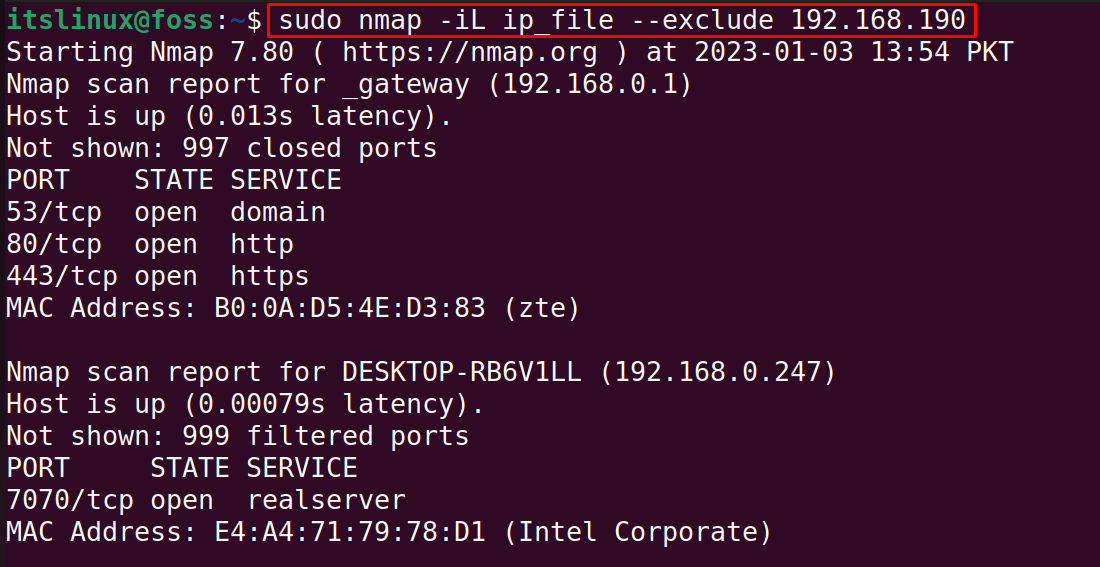
How To Scan Ip Ranges Using Nmap Its Linux Foss This repository explores firewall behavior with nmap scans and basic iptables configuration. it demonstrates identifying open and filtered ports, applying interface specific rules, using port spoofing, and testing proxy routing. All netfilter chains (phases) are listed in the table below. all the chains are ordered in a sequence they are processed in. tables (filter, nat, etc.) will be explained in the next chapter. In this article we will use iptables to build simple but effective firewalls for the following scenarios using allow disallow rules based on ip addresses, ports, and states:. Netfilter is a framework provided by the linux kernel that allows packet manipulation to be implemented in the form of customised handlers.

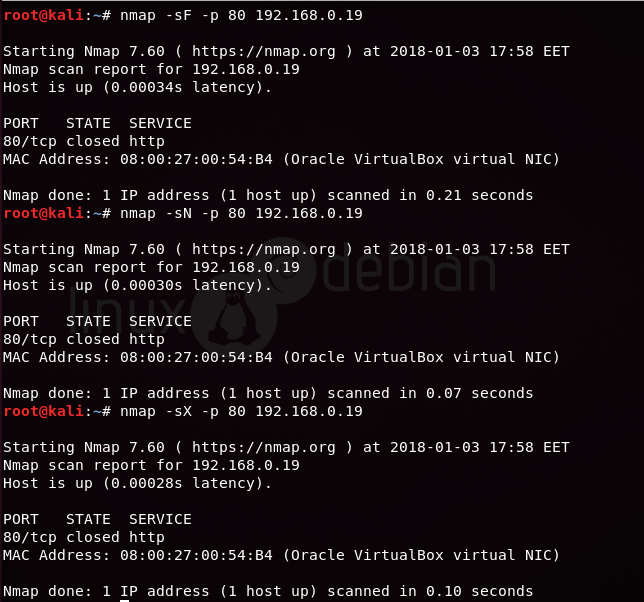
How To Use Nmap To Scan A Network A Step By Step Guide In this article we will use iptables to build simple but effective firewalls for the following scenarios using allow disallow rules based on ip addresses, ports, and states:. Netfilter is a framework provided by the linux kernel that allows packet manipulation to be implemented in the form of customised handlers. In this lab, you will learn how to use nmap to detect firewall restrictions and bypass them. you'll set up a local service for scanning, perform basic nmap scans bypassing host discovery, and explore advanced firewall evasion techniques using packet fragmentation. Today, we will demonstrate how to perform an nmap firewall scan using iptable rules and attempt to bypass the firewall filter to perform advanced nmap scanning. Iptables is the userspace command line program that allows configuring the underlying linux kernel firewall called netfilter. netfilter hooks into networking stack of the kernel and is designed to filter, mangle, log, and process network packets. It is a user space utility program that allows system administrators to configure the tables provided by the linux kernel's netfilter framework. by defining rules, `iptables` can control the flow of network traffic, deciding which packets should be allowed, blocked, or modified.
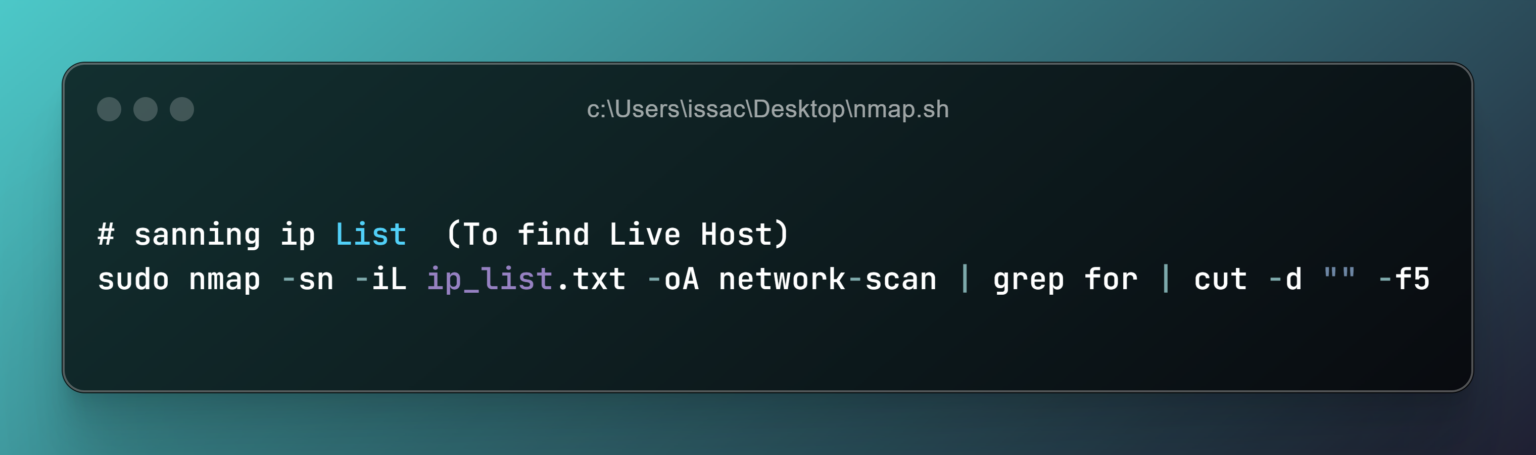
Network Enumeration Using Nmap A Beginner S Guide Part 1 Simbasys In this lab, you will learn how to use nmap to detect firewall restrictions and bypass them. you'll set up a local service for scanning, perform basic nmap scans bypassing host discovery, and explore advanced firewall evasion techniques using packet fragmentation. Today, we will demonstrate how to perform an nmap firewall scan using iptable rules and attempt to bypass the firewall filter to perform advanced nmap scanning. Iptables is the userspace command line program that allows configuring the underlying linux kernel firewall called netfilter. netfilter hooks into networking stack of the kernel and is designed to filter, mangle, log, and process network packets. It is a user space utility program that allows system administrators to configure the tables provided by the linux kernel's netfilter framework. by defining rules, `iptables` can control the flow of network traffic, deciding which packets should be allowed, blocked, or modified.

Nmap For Reconnaissance 2 Techgeeks Iptables is the userspace command line program that allows configuring the underlying linux kernel firewall called netfilter. netfilter hooks into networking stack of the kernel and is designed to filter, mangle, log, and process network packets. It is a user space utility program that allows system administrators to configure the tables provided by the linux kernel's netfilter framework. by defining rules, `iptables` can control the flow of network traffic, deciding which packets should be allowed, blocked, or modified.

Learning Nmap Host Discovery With Iptables And Wireshark Analysis
Comments are closed.