Deleted Process Binary Attack On Linux Sandfly Security
Sandfly Security Sans Internet Storm Center Linux malware often deletes its binary from the disk to evade detection and analysis. learn how to detect and respond to this attack in this video. A deleted process binary on linux is a common malware evasion tactic. learn more about the threat, how to detect it, and command line linux forensics to recover the binary for analysis in this.
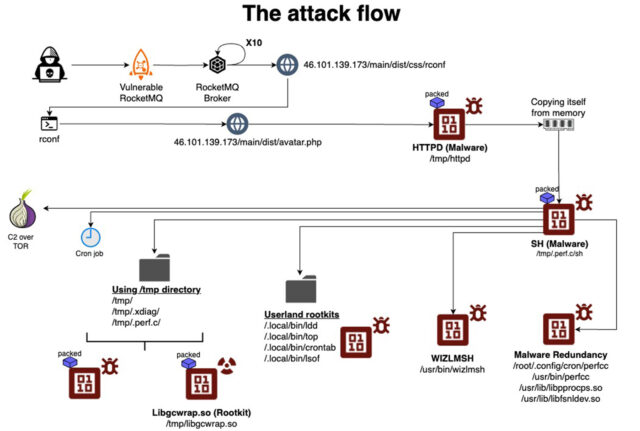
Thousands Of Linux Systems Infected By Stealthy Malware Since 2021 In this video we will discuss the threat and how to find it with sandfly's agentless linux edr. we'll then show you how to investigate it with command line forensics and recover the running process binary for analysis. In this video we will discuss the threat and how to find it with sandfly's agentless linux edr. we'll then show you how to investigate it with command line forensics and recover the running process binary for analysis. Malware on linux will often delete the on disk binary to evade detection with traditional anti virus and file integrity monitoring tools. in this video we wi. You can easily recover a deleted linux process binary that has been removed by malware or other malcious actor. we'll show you how to do it.
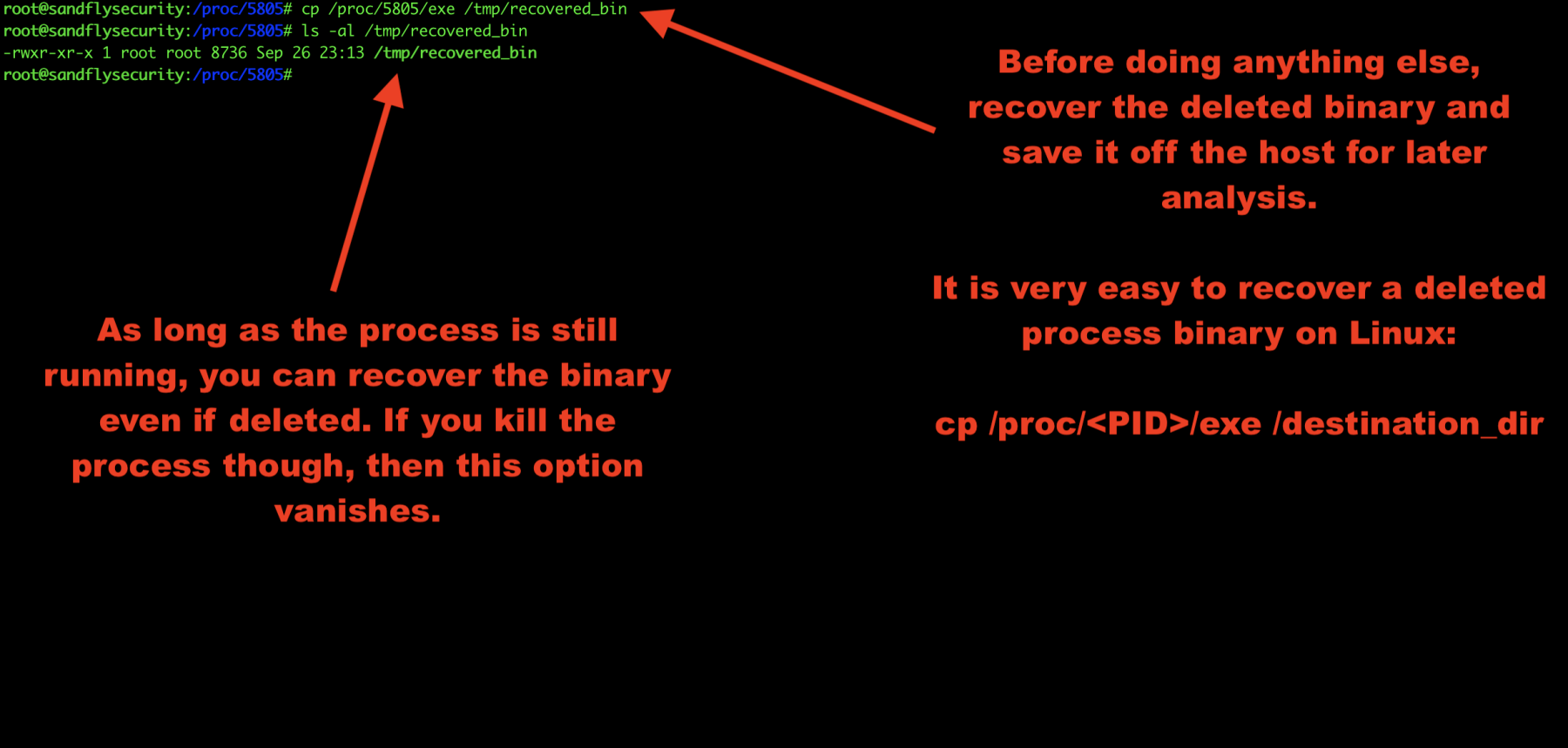
How To Basic Linux Malware Process Forensics For Incident Responders Malware on linux will often delete the on disk binary to evade detection with traditional anti virus and file integrity monitoring tools. in this video we wi. You can easily recover a deleted linux process binary that has been removed by malware or other malcious actor. we'll show you how to do it. Bpfdoor is an stealthy linux backdoor operating for years undetected. we disclose full technical details and detection techniques here. A deleted process binary on linux is a common malware evasion tactic. learn more about the threat, how to detect it, and command line linux forensics to recover the binary for analysis. Agentless intrusion detection and incident response for linux.learn about digital forensics and intrusion detection for linux. When you set sandfly to kill a suspicious process we will terminate the process immediately on the host. while this will stop the process in question, it may also cause any forensic data it has in memory to be immediately lost.

How To Basic Linux Malware Process Forensics For Incident Responders Bpfdoor is an stealthy linux backdoor operating for years undetected. we disclose full technical details and detection techniques here. A deleted process binary on linux is a common malware evasion tactic. learn more about the threat, how to detect it, and command line linux forensics to recover the binary for analysis. Agentless intrusion detection and incident response for linux.learn about digital forensics and intrusion detection for linux. When you set sandfly to kill a suspicious process we will terminate the process immediately on the host. while this will stop the process in question, it may also cause any forensic data it has in memory to be immediately lost.
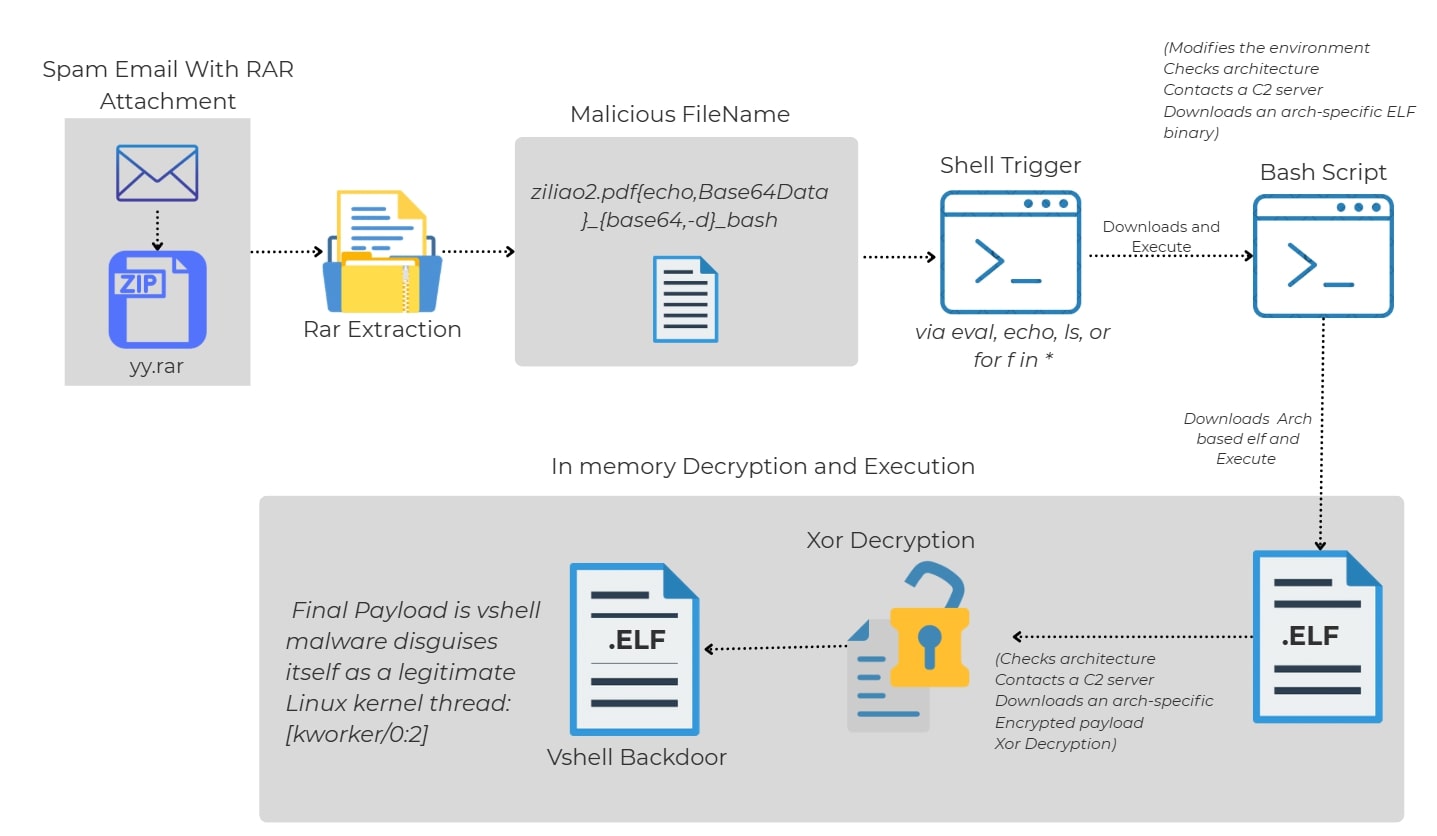
Attackers Weaponise Linux File Names As Malware Vectors Itnews Agentless intrusion detection and incident response for linux.learn about digital forensics and intrusion detection for linux. When you set sandfly to kill a suspicious process we will terminate the process immediately on the host. while this will stop the process in question, it may also cause any forensic data it has in memory to be immediately lost.

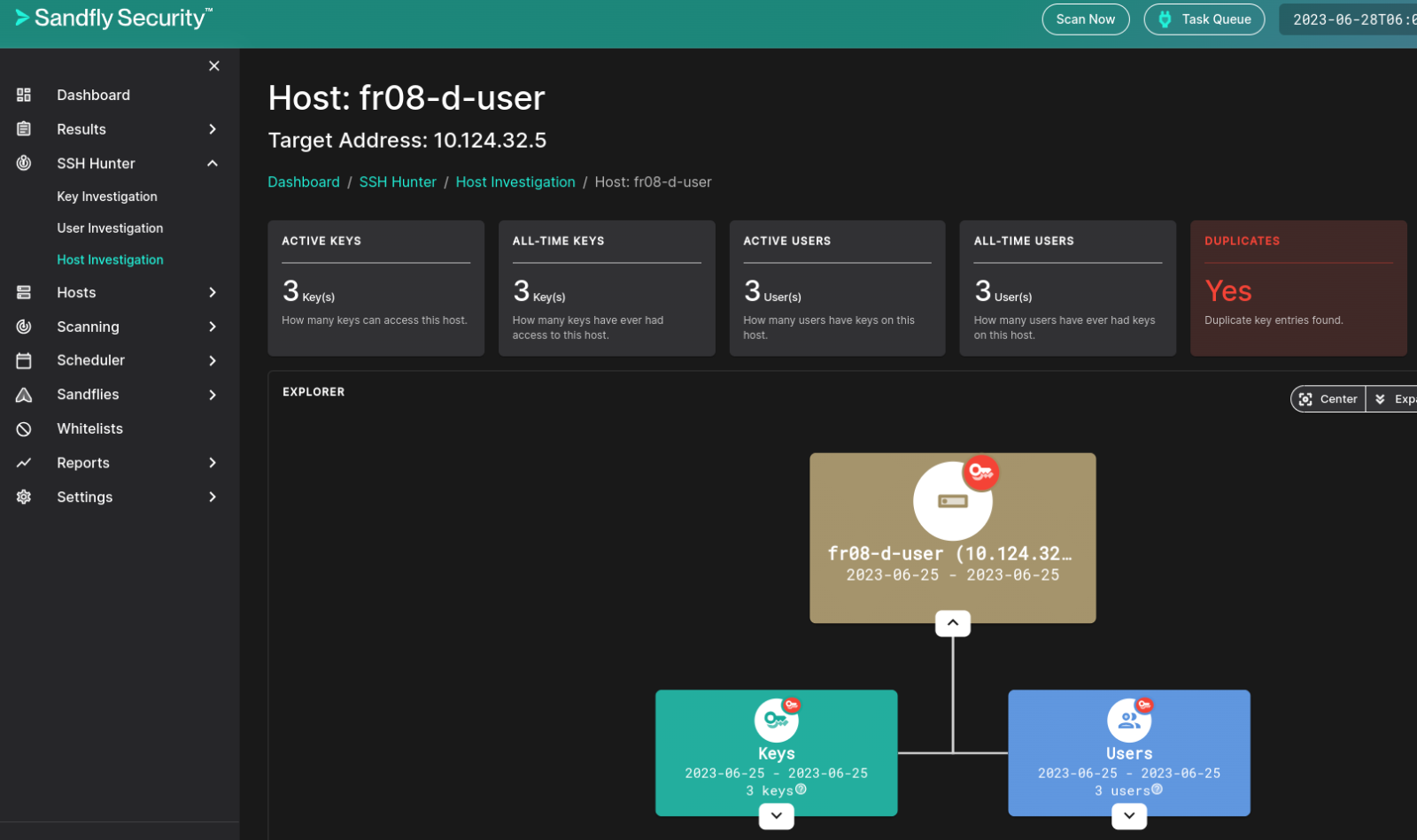
Sandfly Agentless Security For Linux Splunkbase
Comments are closed.