Deleted Process Binary Attack On Linux

How To Kill A Process In The Linux Terminal Tom S Hardware Linux malware often deletes its binary from the disk to evade detection and analysis. learn how to detect and respond to this attack in this video. A deleted process binary on linux is a common malware evasion tactic. learn more about the threat, how to detect it, and command line linux forensics to recover the binary for analysis in this.
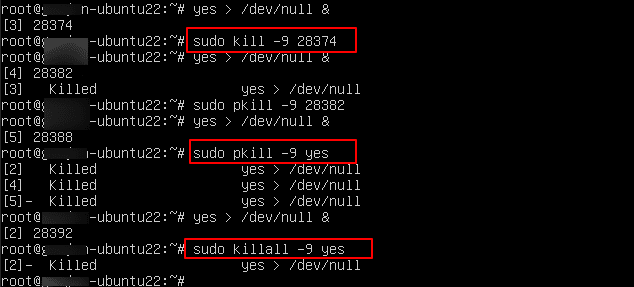
How To Kill A Process In Linux Kamatera In this video we will discuss the threat and how to find it with sandfly's agentless linux edr. we'll then show you how to investigate it with command line forensics and recover the running process binary for analysis. In this video we will discuss the threat and how to find it with sandfly's agentless linux edr. we'll then show you how to investigate it with command line forensics and recover the running process binary for analysis. Malware on linux will often delete the on disk binary to evade detection with traditional anti virus and file integrity monitoring tools. in this video we wi. This bash script detects deleted files still held open by running processes on linux systems for malware detection and rootkit discovery, exposing hidden malicious binaries that evade standard filesystem enumeration tools through post execution deletion techniques.
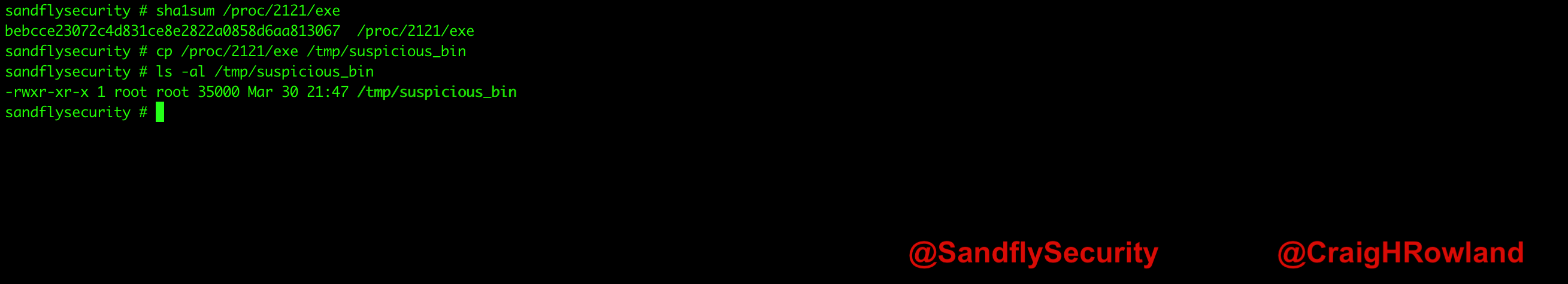
Detecting Linux Kernel Process Masquerading With Command Line Forensics Malware on linux will often delete the on disk binary to evade detection with traditional anti virus and file integrity monitoring tools. in this video we wi. This bash script detects deleted files still held open by running processes on linux systems for malware detection and rootkit discovery, exposing hidden malicious binaries that evade standard filesystem enumeration tools through post execution deletion techniques. Now that we’ve saved the linux binary somewhere off the system, we can recover the hashes easily. if you are using netcat to simulate the attack, you can recover the deleted binary and run a hash on the system netcat command and the recovered binary and see they match. In this detailed guide, we explore how to recover deleted files from running processes on linux by leveraging the proc filesystem. Malware on linux will often delete the on disk binary to evade detection with traditional anti virus. File metadata and controls code blame 16 lines (16 loc) · 551 bytes raw 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 linux forensics processes with deleted binary: query: 'select datetime (start time, "unixepoch", "utc") as start time, name, path, pid from processes where on disk=0; ' defense evasion: ta0005 indicator removal on host: t1070.
Comments are closed.