Defining Encryption Profiles

Encryption Profiles This example illustrates the fields and controls on the encryption profile page. to define a new encryption profile, specify a new profile id, then select an algorithm chain id. each algorithm in the chain appears in order, in its own row with its algorithm id and chain sequence number. An encryption profile refers to an existing trust store file and optionally to an existing private keystore file. encryption profiles can be managed with the configuration tool. encryption profiles are stored in the secrets.jks file in the cdc replication keystore directory.

Encryption Profiles The internet protocol security (ipsec) profiles provide information about the algorithms that are used to authenticate, encrypt, and establish a shared secret between network sites when you establish an ipsec tunnel. To use your encryption profile, follow the steps below: you can have different encryption profiles for each available environment mode (uat, dev, prod). go to your web service miniapp where you want to use the encryption service. Encryption profiles the confidentiality and integrity of data exchanged over a vpn (site to site or client to site) depend on the use of robust cryptographic algorithms negotiated between both parties. by using encryption profiles, allowed algorithms can be specified. This document explains the encryption profiles used within the readium licensed content protection (lcp) system. encryption profiles define the specific cryptographic algorithms, parameters, and implementations used to protect digital publications.
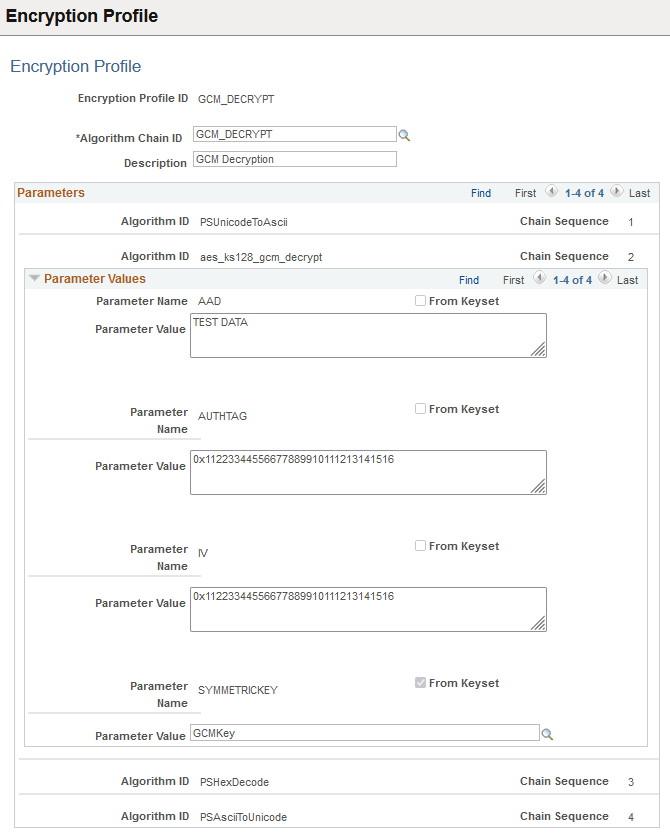
Defining Encryption Profiles Encryption profiles the confidentiality and integrity of data exchanged over a vpn (site to site or client to site) depend on the use of robust cryptographic algorithms negotiated between both parties. by using encryption profiles, allowed algorithms can be specified. This document explains the encryption profiles used within the readium licensed content protection (lcp) system. encryption profiles define the specific cryptographic algorithms, parameters, and implementations used to protect digital publications. To define a new encryption profile, specify a new profile id, then select an algorithm chain id. each algorithm in the chain appears in order, in its own row with its algorithm id and chain sequence number. This example illustrates the fields and controls on the administer encryption profile page for an existing profile (1 of 3). you can find definitions for the fields and controls later on this page. You can define a default encryption for a single pool. when an encryption profile has been defined as the default, it is applied whenever documents are archived in this pool. if no encryption profile is defined as the default, documents are not encrypted when archived in this pool. An encryption profile refers to an existing trust store file and optionally to an existing private keystore file. encryption profiles can be managed with either a graphical user interface or with a command line interface. encryption profiles are stored in the secrets.jks file in the cdc replication keystore directory.

Encryption Profiles To define a new encryption profile, specify a new profile id, then select an algorithm chain id. each algorithm in the chain appears in order, in its own row with its algorithm id and chain sequence number. This example illustrates the fields and controls on the administer encryption profile page for an existing profile (1 of 3). you can find definitions for the fields and controls later on this page. You can define a default encryption for a single pool. when an encryption profile has been defined as the default, it is applied whenever documents are archived in this pool. if no encryption profile is defined as the default, documents are not encrypted when archived in this pool. An encryption profile refers to an existing trust store file and optionally to an existing private keystore file. encryption profiles can be managed with either a graphical user interface or with a command line interface. encryption profiles are stored in the secrets.jks file in the cdc replication keystore directory.

Encryption Profiles You can define a default encryption for a single pool. when an encryption profile has been defined as the default, it is applied whenever documents are archived in this pool. if no encryption profile is defined as the default, documents are not encrypted when archived in this pool. An encryption profile refers to an existing trust store file and optionally to an existing private keystore file. encryption profiles can be managed with either a graphical user interface or with a command line interface. encryption profiles are stored in the secrets.jks file in the cdc replication keystore directory.

Defining Encryption Profiles
Comments are closed.