Defining Boundaries Firewall Rules

Firewall Rules Pdf Firewall Computing Port Computer Networking Firewall zones categorize network interfaces, defining trust boundaries, while firewall rules dictate traffic handling between zones. zones organize network segments, and rules enforce security policies by specifying conditions for permitted or denied actions. Network boundaries are the limits that define where a network begins and ends. they are used to specify the range of devices and services that are allowed on the network. network boundaries are also used to protect the network from unauthorized access and malicious attacks.

Firewall Rules To Create Pdf Ip Address Port Computer Networking Network boundaries, within the realm of firewalls, define the line between internal and external networks. think of them as digital security checkpoints that manage incoming and outgoing traffic. by setting up these boundaries, you can control who gets access to your network and who doesn’t. What is a boundary firewall? in the digital age, where information flows freely and cyber threats loom large, security protocols have become paramount. one of the frontline defenders in network security is the boundary firewall. Below, we explain each type and provide specific firewall rule examples in tables to illustrate how they work, along with expanded explanations for clarity. access rules access rules define what types of traffic are permitted or denied based on ip addresses, ports, and protocols. Learn about the different types of firewall rules, and what are some important points to consider when defining firewall rules.

Best Practices For Firewall Rules Configuration Pdf Port Computer Below, we explain each type and provide specific firewall rule examples in tables to illustrate how they work, along with expanded explanations for clarity. access rules access rules define what types of traffic are permitted or denied based on ip addresses, ports, and protocols. Learn about the different types of firewall rules, and what are some important points to consider when defining firewall rules. By defining a set of conditions for traffic evaluation, firewall rules play an instrumental role in defending against cyber threats, unauthorized access, and safeguarding sensitive data. Configure restrictions on your firewall rules depending on which profile the rules are applied to. for applications and services that are designed to only be accessed by devices within a home or small business network, it's best to modify the remote address restriction to specify local subnet only. In this article, we will explore the basics of firewall rules, discuss common types of firewall rules, and provide best practices for configuring and managing firewall rules to enhance your organization’s cybersecurity posture. Establish clear policies for firewall rule management by defining the organization's security requirements, identifying critical assets, and determining the necessary protection levels.
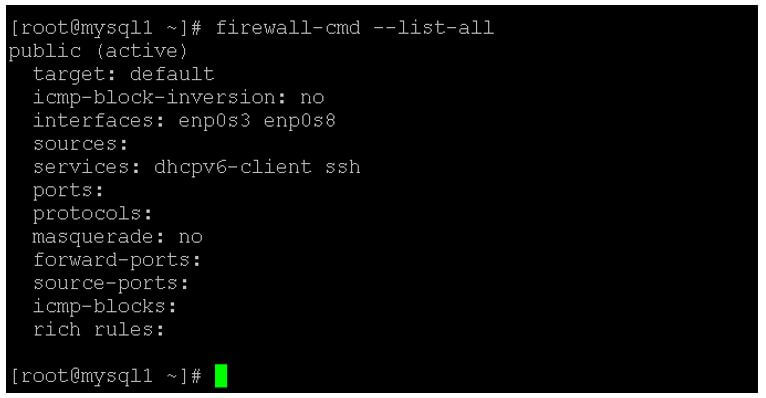
Firewall Rules How Firewall Rules Works With Examples By defining a set of conditions for traffic evaluation, firewall rules play an instrumental role in defending against cyber threats, unauthorized access, and safeguarding sensitive data. Configure restrictions on your firewall rules depending on which profile the rules are applied to. for applications and services that are designed to only be accessed by devices within a home or small business network, it's best to modify the remote address restriction to specify local subnet only. In this article, we will explore the basics of firewall rules, discuss common types of firewall rules, and provide best practices for configuring and managing firewall rules to enhance your organization’s cybersecurity posture. Establish clear policies for firewall rule management by defining the organization's security requirements, identifying critical assets, and determining the necessary protection levels.
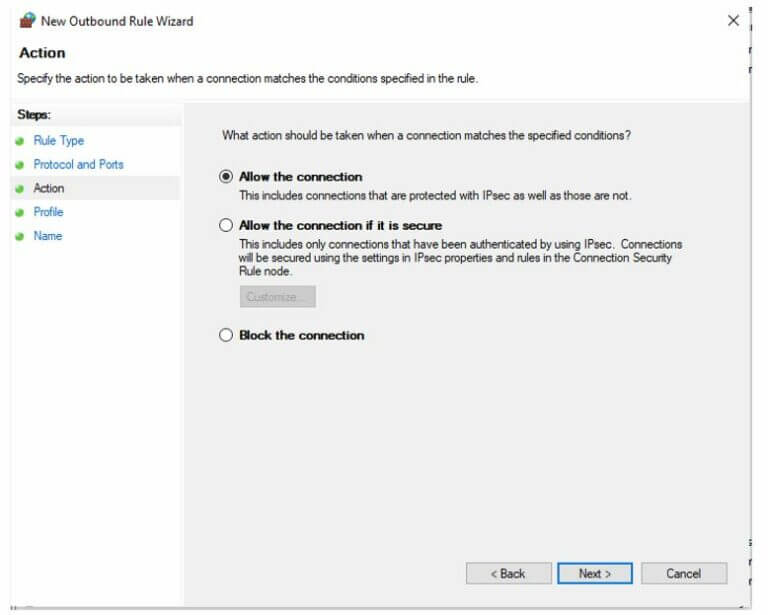
Firewall Rules How Firewall Rules Works With Examples In this article, we will explore the basics of firewall rules, discuss common types of firewall rules, and provide best practices for configuring and managing firewall rules to enhance your organization’s cybersecurity posture. Establish clear policies for firewall rule management by defining the organization's security requirements, identifying critical assets, and determining the necessary protection levels.
Comments are closed.