Decsoft Blog Two Factor Authentication
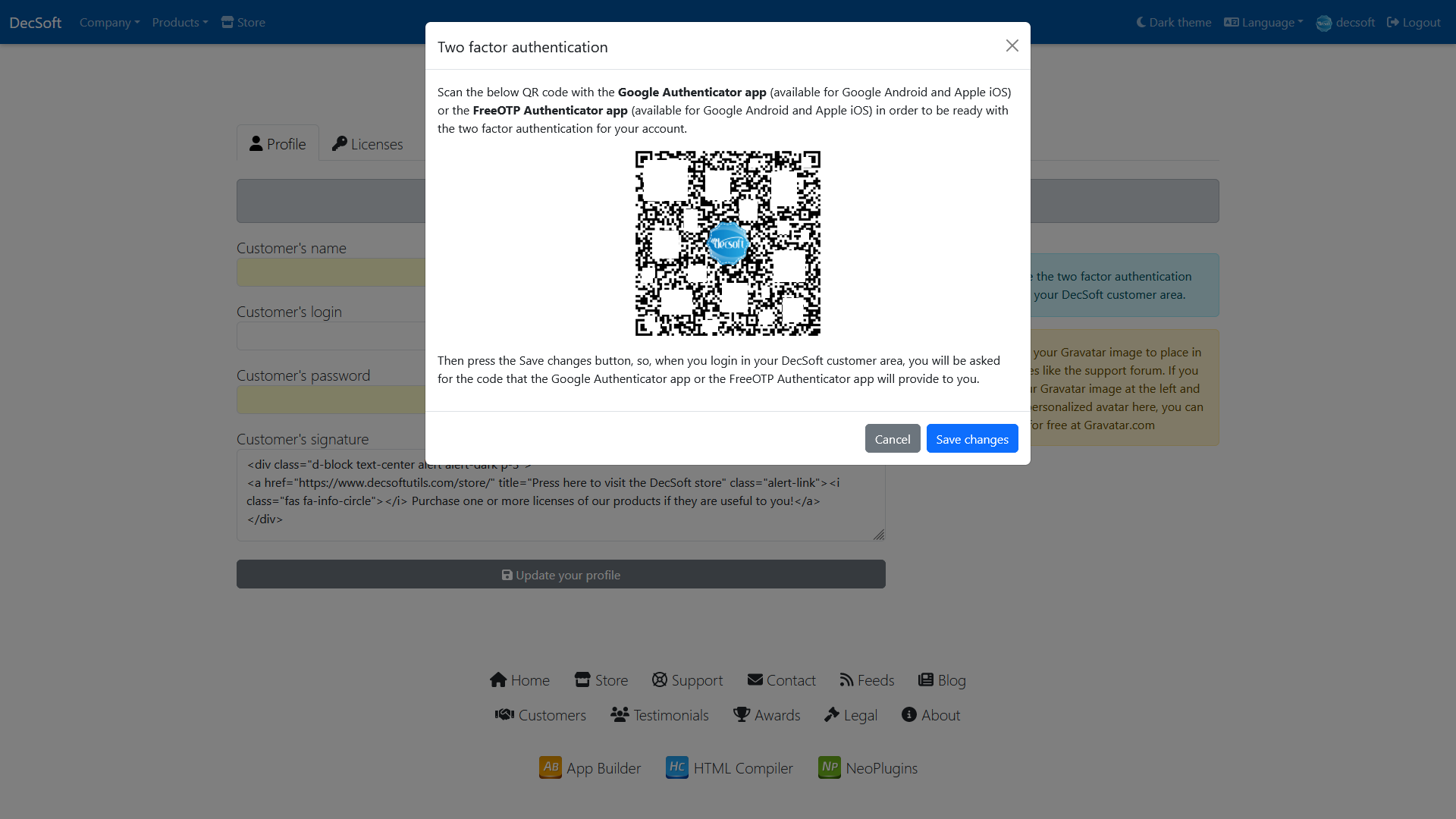
Decsoft Blog Two Factor Authentication We are happy to announce that you can now enable and use a two factor authentication to be used when login into your decsoft customer area here in this website. Kesimpulan two factor authentication adalah salah satu langkah paling sederhana dan efektif untuk menjaga keamanan akun digital kamu. sebagai bagian dari multi factor authentication (mfa), 2fa menggunakan dua kategori otentikasi yang berbeda untuk memastikan hanya kamu yang bisa mengakses akun kamu.

Decsoft Blog Two Factor Authentication Now you can enable a two factor authentication to login into your decsoft customer area! see how easy is to activate it by reading this entry in our blog: lnkd.in duxs7sa5. We are happy to announce that you can now enable and use a two factor authentication to be used when login into your decsoft customer area here in this website. 2fa adds a crucial layer of login security. learn how it works, why it matters, and which methods best protect your accounts from hacking and data theft. Two factor authentication, atau autentikasi dua faktor, adalah metode keamanan yang mengharuskan pengguna untuk memberikan dua jenis bukti identitas sebelum mendapatkan akses ke sistem, aplikasi, atau layanan online.

Enable The Two Factor Authentication Reloadly 2fa adds a crucial layer of login security. learn how it works, why it matters, and which methods best protect your accounts from hacking and data theft. Two factor authentication, atau autentikasi dua faktor, adalah metode keamanan yang mengharuskan pengguna untuk memberikan dua jenis bukti identitas sebelum mendapatkan akses ke sistem, aplikasi, atau layanan online. From the decsoft website you can get information, download and purchase licenses of our software products: decsoft app builder, decsoft html compiler and decsoft neoplugins. In this blog, let’s understand the top 7 best multi factor authentication (mfa) software to prevent unauthorized users from accessing your data. conventional authentication mechanisms get exploited through keylogging, phishing, or simple brute force attacks. Step by step guide to setting up two factor authentication (2fa) with authenticator apps, hardware keys, and backup codes for maximum security. Two factor authentication (2fa) —the non negotiable security standard that adds a critical second layer of protection to your accounts and data. this two factor authentication guide will show you why it's the bedrock of modern account security.

Two Factor Authentication For Software Products Sdh From the decsoft website you can get information, download and purchase licenses of our software products: decsoft app builder, decsoft html compiler and decsoft neoplugins. In this blog, let’s understand the top 7 best multi factor authentication (mfa) software to prevent unauthorized users from accessing your data. conventional authentication mechanisms get exploited through keylogging, phishing, or simple brute force attacks. Step by step guide to setting up two factor authentication (2fa) with authenticator apps, hardware keys, and backup codes for maximum security. Two factor authentication (2fa) —the non negotiable security standard that adds a critical second layer of protection to your accounts and data. this two factor authentication guide will show you why it's the bedrock of modern account security.

Two Factor Authentication A Deep Dive Gemini Step by step guide to setting up two factor authentication (2fa) with authenticator apps, hardware keys, and backup codes for maximum security. Two factor authentication (2fa) —the non negotiable security standard that adds a critical second layer of protection to your accounts and data. this two factor authentication guide will show you why it's the bedrock of modern account security.
Comments are closed.